The End of xmrwallet[.]com: NameSilo Lied to Protect a $2M Thief
After 10 years of stealing Monero private keys, the operation is destroyed. Three registrars acted within days. The fourth — NameSilo — contacted the scammer, believed his story, and became his press secretary.

What xmrwallet[.]com Actually Did
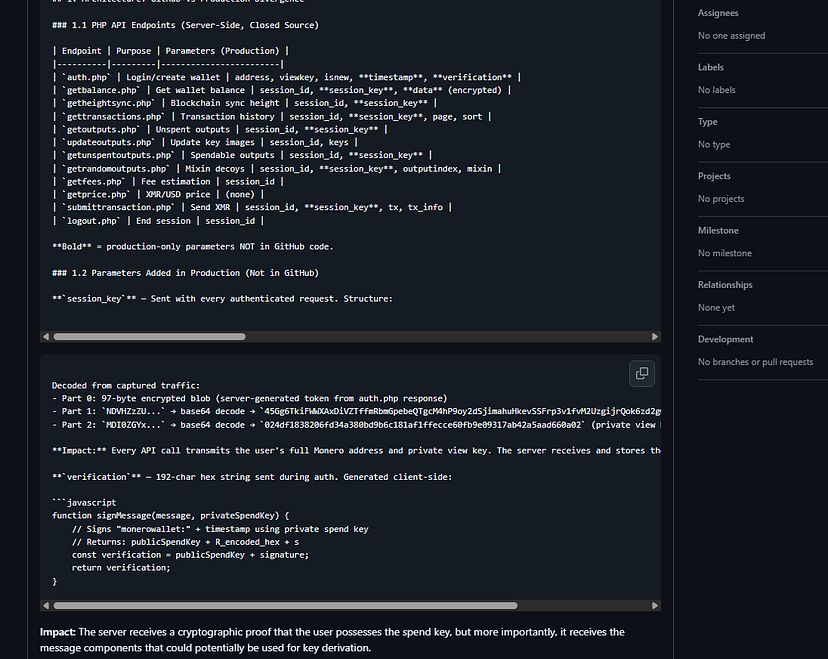
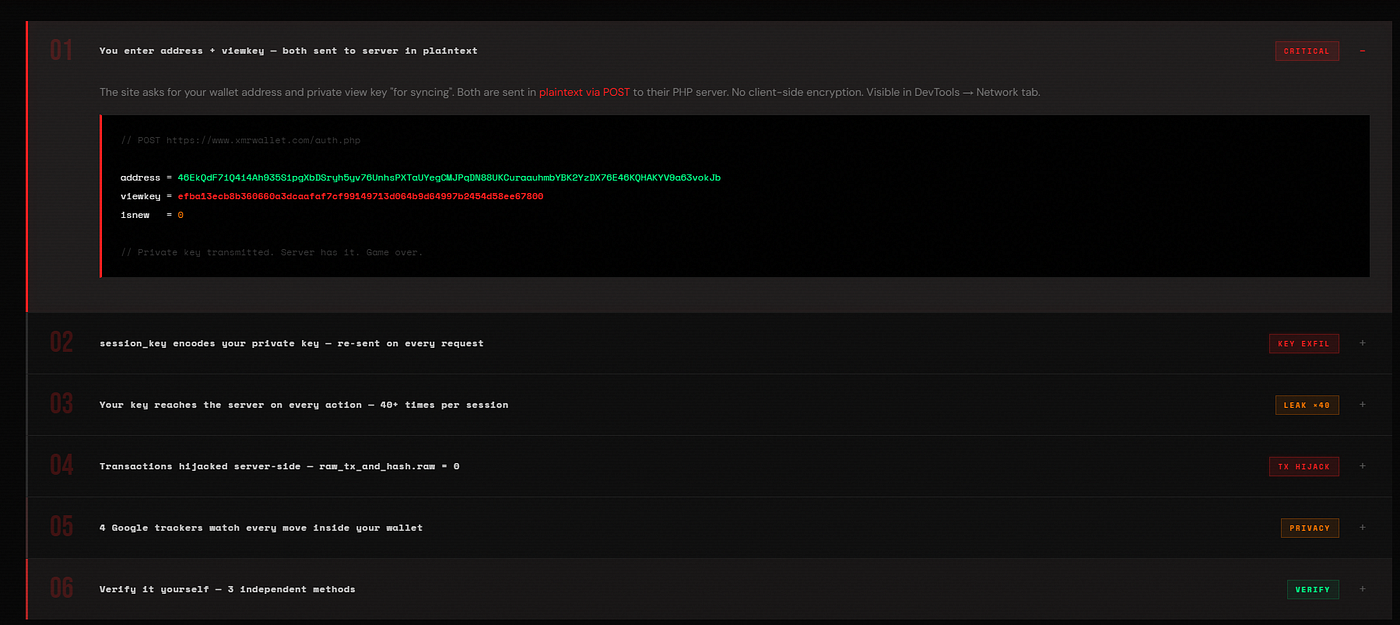
Since 2016, xmrwallet[.]com marketed itself as a free, open-source Monero wallet. Our live network capture on February 18, 2026 proved it was doing something very different: stealing private Monero view keys on every login and hijacking transactions server-side.

Not injected code — the core architecture. A session system across 8 PHP endpoints, transmitting the victim’s private view key 40+ times per session. When users sent XMR, their transaction was silently discarded (raw_tx_and_hash.raw = 0) and replaced with the scammer’s.
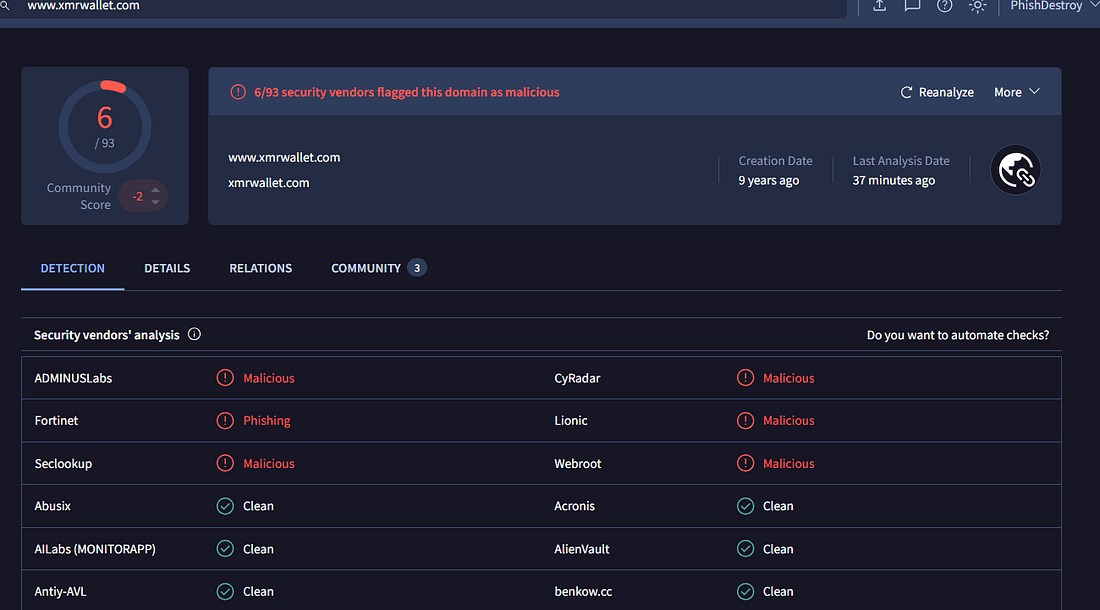
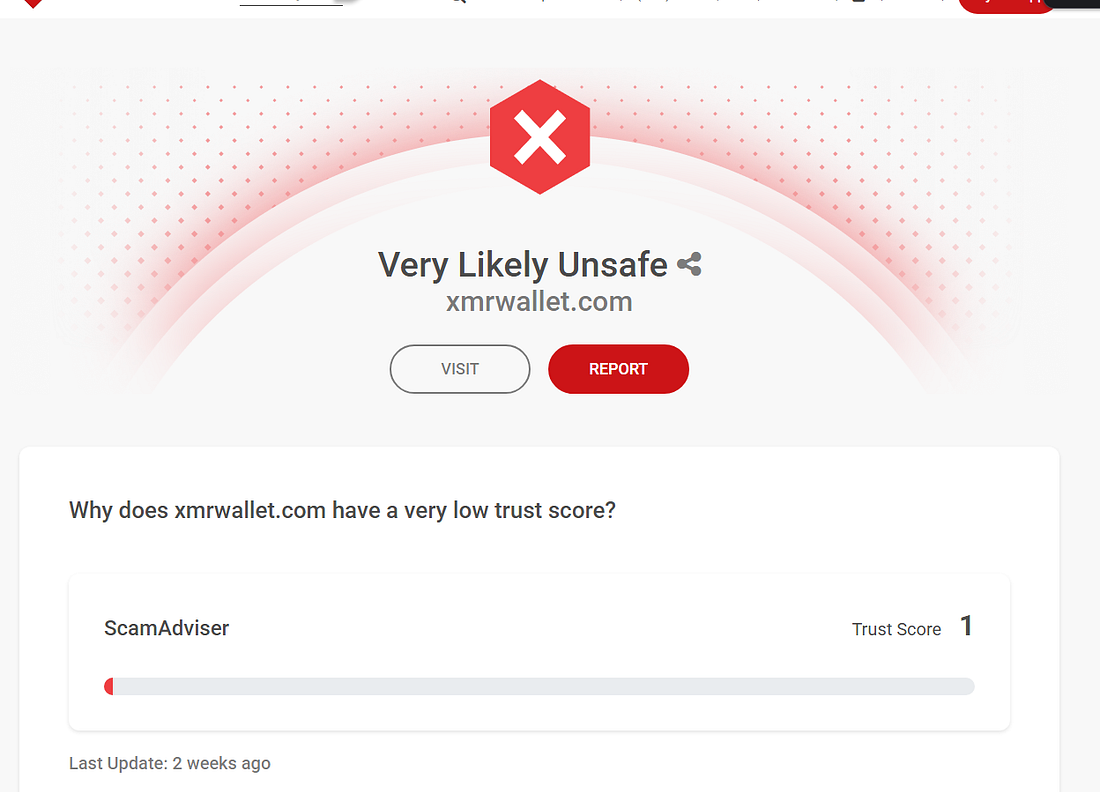
Six security vendors on VirusTotal flagged it as malicious. Fifteen documented victims across Trustpilot, Sitejabber, and BitcoinTalk. One victim lost 590 XMR (~$177,000) in a single theft.
Three Registrars Did Their Job
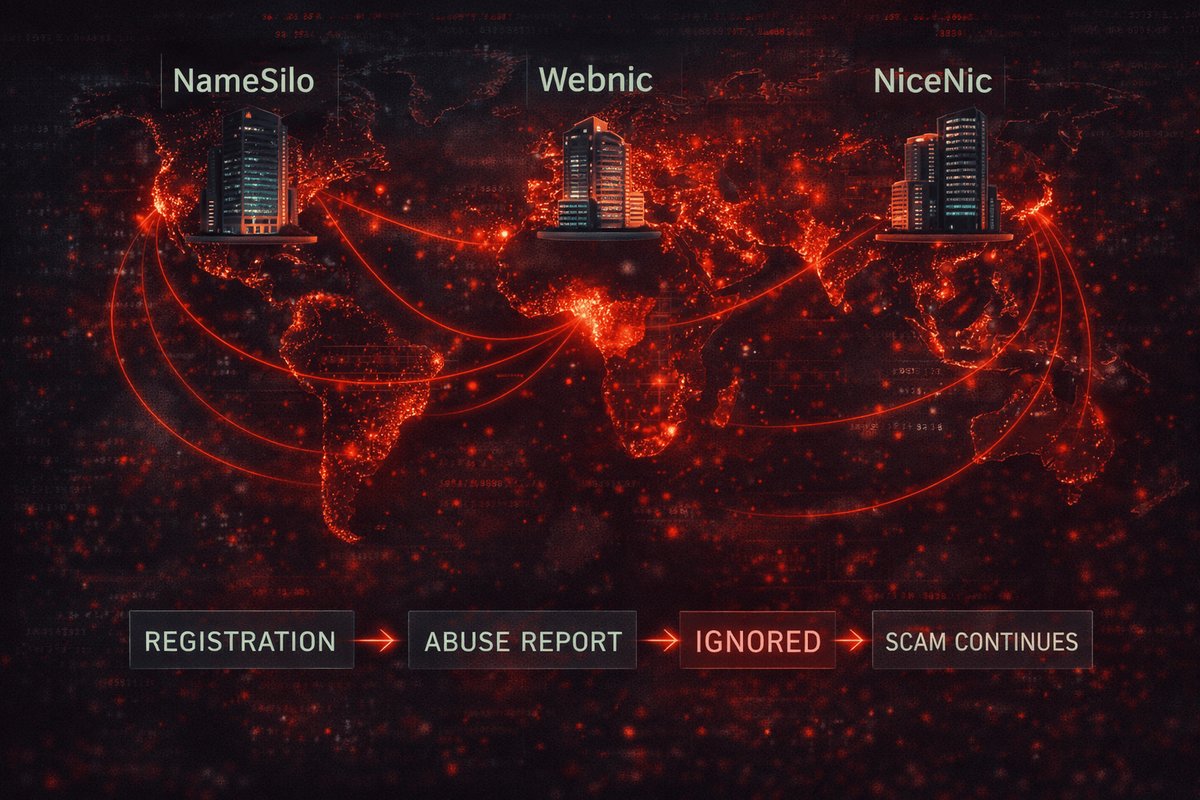
We filed identical abuse reports with all four registrars hosting xmrwallet domains. Three acted immediately:

PublicDomainRegistry
India · Days to act
WebNic
Malaysia · Days to act
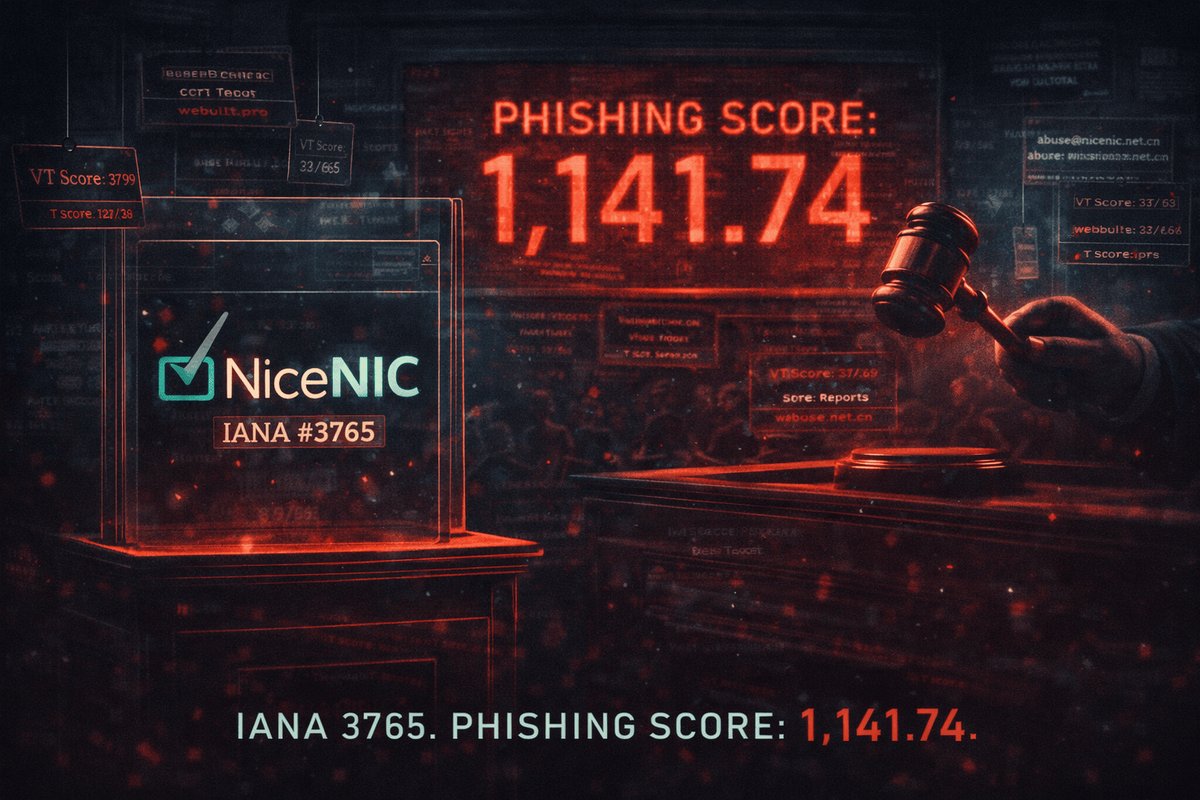
NICENIC
China · Weeks to act
NameSilo
USA · Defended scammer
India, Malaysia, China — reviewed the evidence, found fraud, suspended the domains. No questions asked.
NameSilo Chose a Different Path
The fourth registrar — NameSilo, LLC (USA) — hosting the primary domain with the most evidence and most victims — did the opposite. They contacted the scammer, believed his story, and published a public statement defending him:
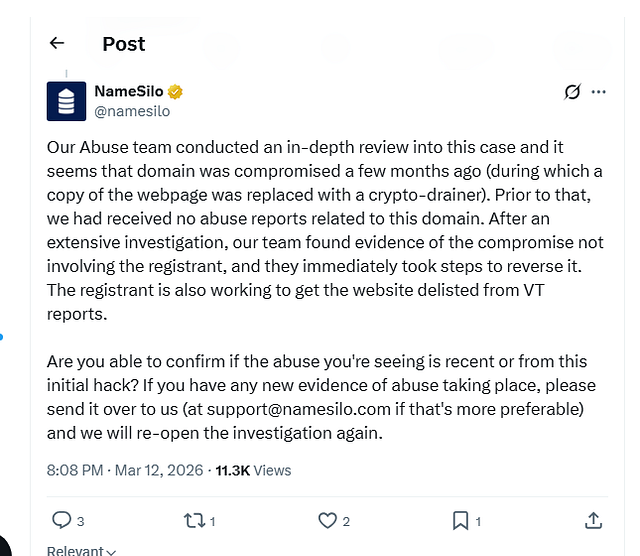
“Our Abuse team conducted an in-depth review into this case and it seems that domain was compromised a few months ago... After an extensive investigation, our team found evidence of the compromise not involving the registrant... The registrant is also working to get the website delisted from VT reports.”
— NameSilo, via X (Twitter)
We analyzed this statement line by line. Every claim was false.
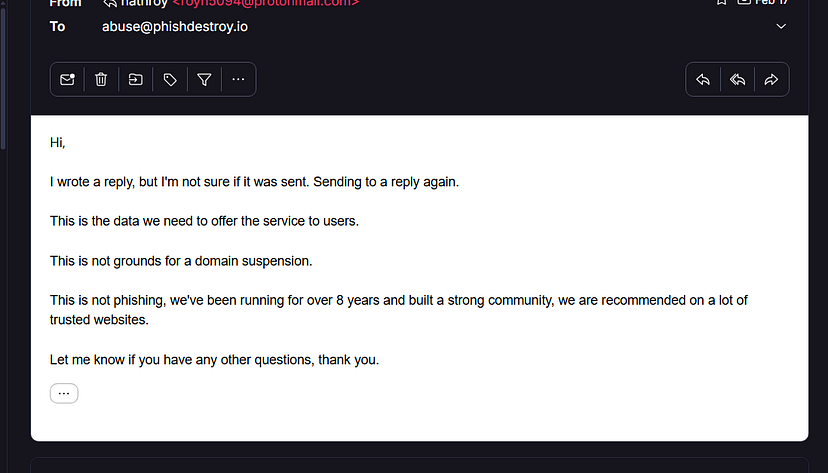
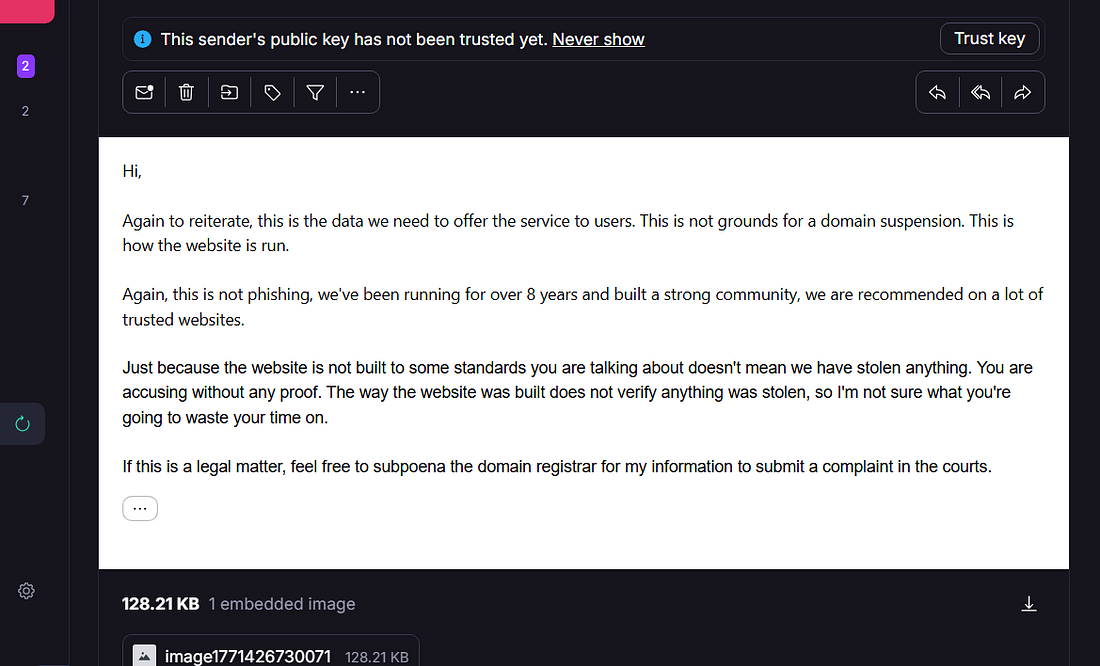
The Operator’s Own Words
Before NameSilo intervened, the operator responded directly to our abuse report. His emails confirm awareness and intent:
Seven Lies, Exposed
The theft mechanism is the core architecture — 8 PHP endpoints, Base64 key exfiltration, a 5.3-year GitHub commit gap. This system was built over years, not injected in a hack.
Six VirusTotal vendors, Trustpilot complaints going back years, a BitcoinTalk warning thread, the operator banned from r/Monero in 2018. A single Google search would have shown this.
The operator registered 4 escape domains across 4 registrars (prepaid 5-10 years each) before the investigation was published. Deleted 21+ GitHub issues. Hired developers for a captcha system. That’s not a victim — that’s an operation.
The theft code was running in production during NameSilo’s statement. Zero GitHub commits addressing any incident. Nothing was reversed.
NameSilo praised the scammer for lobbying to remove Fortinet’s “Phishing” detection — without removing the phishing code. That’s not good faith. That’s suppressing security warnings.
Shifting the burden of proof to the reporter so they can close the case. The evidence was in the report. Three peer registrars didn’t need to ask.
“Re-open” implies it was once open. Their investigation consisted of calling the scammer and writing down what he said. That’s not an investigation — that’s dictation.
Infrastructure Evidence


Timeline: The Fall of xmrwallet
The Verdict
NameSilo didn’t ignore the evidence. They read it, called the scammer, believed him, declared him innocent, and helped suppress security warnings. Then asked the researchers to prove the abuse is “recent.”
That’s not negligence. That’s a partnership.
The domain is down. The scam is over. But the fact that a US registrar chose to publicly fabricate a cover story to shield a $2M crypto thief — that is something that will follow NameSilo for a very long time. Their statement will be Exhibit A in every filing from this point forward.
If you vouch for the thief, you share his bill.
Evidence & Resources
Related Investigations
This investigation is based on publicly available evidence, live network captures, OSINT, public review platforms, and NameSilo’s own verbatim public statement. No unauthorized access was performed. All findings are independently reproducible.