newexodus[.]store
Domain Security & Threat Intelligence Report“– New Exodus”
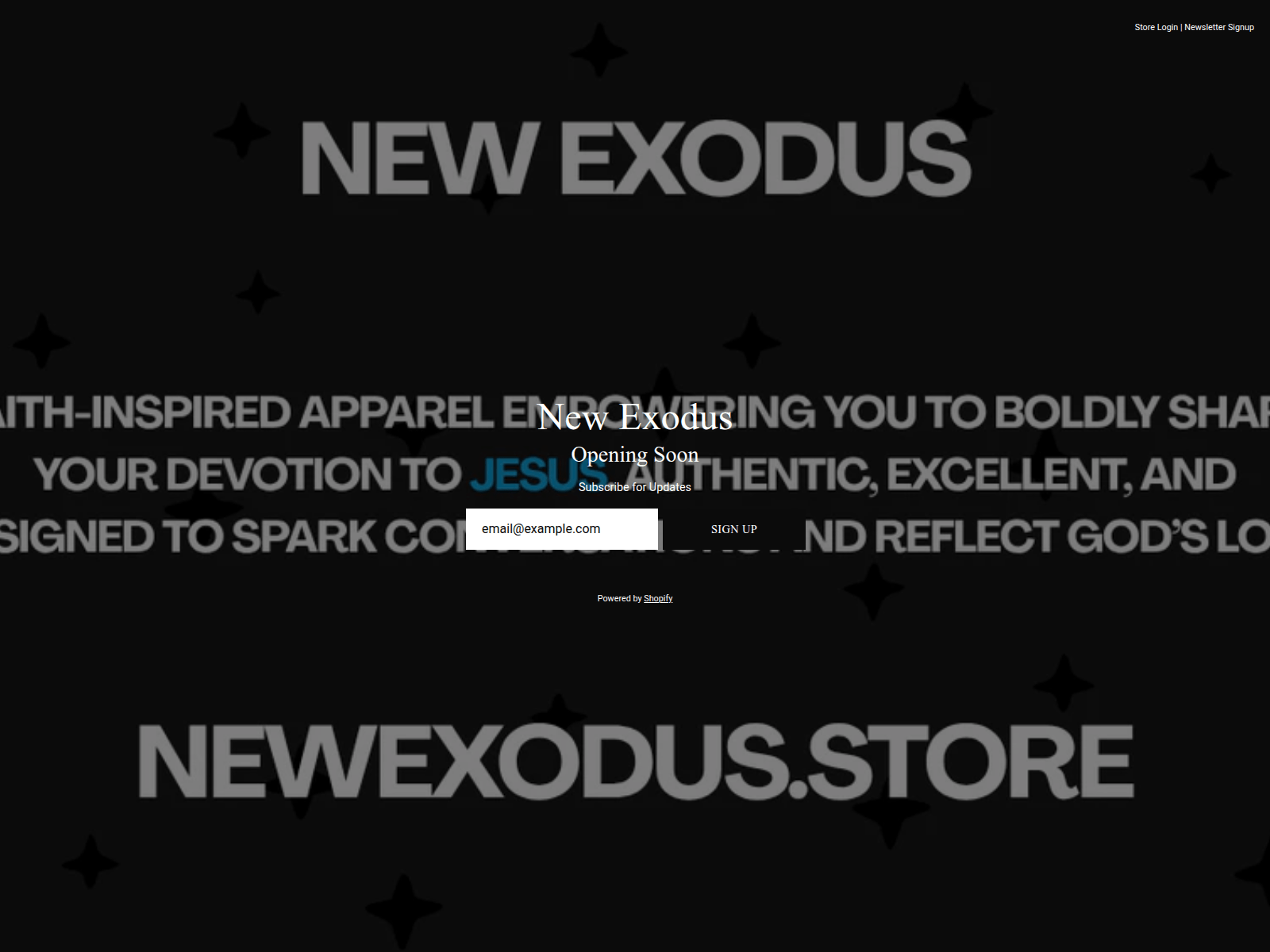
This phishing domain was registered through Tucows Domains Inc. and was flagged by 4 out of 95 security vendors on VirusTotal. It resolved to IP 23.227.38.73 and appeared on two security blocklists before being taken offline. The site’s page title mimicked Exodus branding to deceive visitors into submitting sensitive information.
Users who visited newexodus[.]store should immediately change any passwords or wallet access details they may have entered. It is crucial to verify domain authenticity before providing credentials and to rely on official Exodus channels for downloads or updates. Reporting suspicious domains helps prevent further victimization.
Network Security Intelligence
Threat Response Pipeline
Public Blocklist Status
Evidence Capture
Domain Intelligence
Technical detailsDNS, SSL SANs, timestamps
Threat Intel Cross-Reference · external sources
- · PhishDestroy — Active Phishing & Crypto Scam Domains by phishdestroy
Related Campaign Members · 8 sharing fingerprint
Technologies · 5 identified
Shopify is a subscription-based software that allows anyone to set up an online store and sell their products. Shopify store owners can also sell in physical locations using Shopify POS, a point-of-sale app and accompanying hardware.
shopify.com 100% confidenceHTTP Strict Transport Security (HSTS) informs browsers that the site should only be accessed using HTTPS.
www.rfc-editor.org 100% confidenceCloudflare is a web-infrastructure and website-security company, providing content-delivery-network services, DDoS mitigation, Internet security, and distributed domain-name-server services.
www.cloudflare.com 100% confidenceBugsnag is a cross-platform error monitoring, reporting, and resolution software.
bugsnag.com 100% confidenceHTTP/3 is the third major version of the Hypertext Transfer Protocol used to exchange information on the World Wide Web.
httpwg.org 100% confidenceVirusTotal Analysis
Site Performance Analysis
Google PageSpeed Insights — mobile performance audit of newexodus.store · checked Mar 2, 2026
Site Configuration Analysis
Evidence & External Reports
Were You Affected by This Site?
If you have interacted with this domain, entered personal information, or connected a cryptocurrency wallet — take immediate action. Below are resources to help you report the incident and protect yourself.
Report to Your Local Authorities
Select your country to get official cybercrime contacts, or generate an AI-powered complaint →
Related Domain Reports
Other Domains on 23.227.38.73 6 phishing domains
This IP hosts multiple phishing domains — infrastructure shared across campaigns
 More Domains at Tucows 6 flagged
More Domains at Tucows 6 flagged
Other Exodus Impersonation Domains
These domains also target Exodus users. View all Exodus threats →
About This Report: newexodus.store
This domain security report for newexodus.store is maintained by PhishDestroy's automated threat intelligence pipeline. Our system continuously monitors this domain across 4 security vendors on VirusTotal, 3 public blocklists.
The site displays a page titled “– New Exodus”, which may be designed to impersonate Exodus.
newexodus.store has been flagged by 4 security vendors as of April 27, 2026.
If you believe this listing is inaccurate, you can submit an appeal. For more information about our methodology, visit our FAQ page.
Check Any Domain
Instant threat analysis with 50+ security engines, AI classification & forensic evidence
Scan NowReport Phishing
Submit suspicious domains to our threat database — protect the community
ReportLive Threat Feed
Real-time monitoring of active phishing campaigns & takedown progress
MonitorStay Informed, Stay Safe
Monitor live threats or contest this listing if you believe it's a false positive
Recommendations & Advice for Victims
An estimated $51 billion flowed to illicit crypto wallets in 2024 (source). If you interacted with newexodus.store — act now.
What should I do immediately?
Urgent
- Revoke token approvals — use revoke.cash to remove access granted to malicious smart contracts
- Move remaining funds to a brand-new wallet. The compromised wallet is no longer safe
- Change all passwords — email, exchange accounts, anything that shares the same password
- Enable 2FA using an authenticator app (not SMS). Disable SMS-based recovery
- Freeze cards if you entered banking details on the phishing site
What information should I collect for my report?
FBI guidelines
According to the FBI, the most important details are transaction data:
- Cryptocurrency addresses — scammer's wallet (e.g.,
0x5856...35985) - Amount & crypto type — exact amount (e.g., 1.02345 ETH, 0.5 BTC, 500 USDT)
- Transaction ID (hash) — the unique blockchain transaction identifier
- Exact dates & times — of each transaction and first contact with scammer
- Screenshots — scam website, chat messages, emails, wallet transactions, social media
- All URLs & domains used by the scammer (including
newexodus.store) - Communications — emails, texts, phone numbers, usernames the scammer used
Even if you don't have all details — file a report anyway. Partial information still helps investigations.
Where should I report the scam?
- FBI IC3 — Internet Crime Complaint Center (US federal reporting)
- Europol — European cybercrime reporting (EU)
- Chainabuse — flag scam wallets across exchanges & platforms
- Your crypto exchange — contact Coinbase/Binance/Kraken support to freeze scammer's address
- Local police — creates an official record, even if they can't act immediately
The FBI recovered over $1 billion in crypto fraud in 2024 thanks to victim reports. Your report matters.
How do crypto scams typically work?
- Fake websites — pixel-perfect clones of legitimate sites with slightly altered domains
- Malicious approvals — "connect wallet" prompts that grant unlimited token spending to attackers
- Pig butchering — trust built over weeks via Telegram/WhatsApp/dating apps, then money stolen
- Recovery scams — victims targeted AGAIN by fake "recovery agents" demanding upfront fees. Always a scam
- Fake ads & airdrops — Google/social media ads and "free token" offers leading to wallet drainers
- AI-powered scams — deepfakes, automated phishing, and AI-generated sites making fraud harder to detect
How can I protect myself in the future?
- Use a hardware wallet (Ledger, Trezor). Never store large amounts in browser wallets
- Bookmark official sites — never click links from emails, DMs, or ads
- Read every approval — verify permissions before signing. Reject unlimited approvals
- Verify domains — check on PhishDestroy before interacting. Check HTTPS, spelling, domain age
- "Too good to be true" = scam — guaranteed returns, celebrity endorsements, urgent deadlines
How big is the crypto scam problem?
- $51 billion flowed to illicit crypto wallets in 2024 — CoinLedger
- Pig butchering losses grew 40% year over year, now the fastest-growing fraud type
- Only ~5% of victims report — your report helps shut down criminal networks
- FBI recovered $1B+ in 2024 thanks to victim reports — FBI.gov
Sources: FBI · CoinLedger · WorldMetrics


