Trustname[.]com: Inside a “Bulletproof” ICANN-Accredited Registrar Serving Scam Casinos
An ICANN-accredited registrar (IANA #4318) marketing itself as the “fastest growing independent registrar.” Estonian tax filings show €120 in revenue, one employee, negative equity, and a deletion notice. Both owners are Belarusian. The scam casino domains keep flowing.
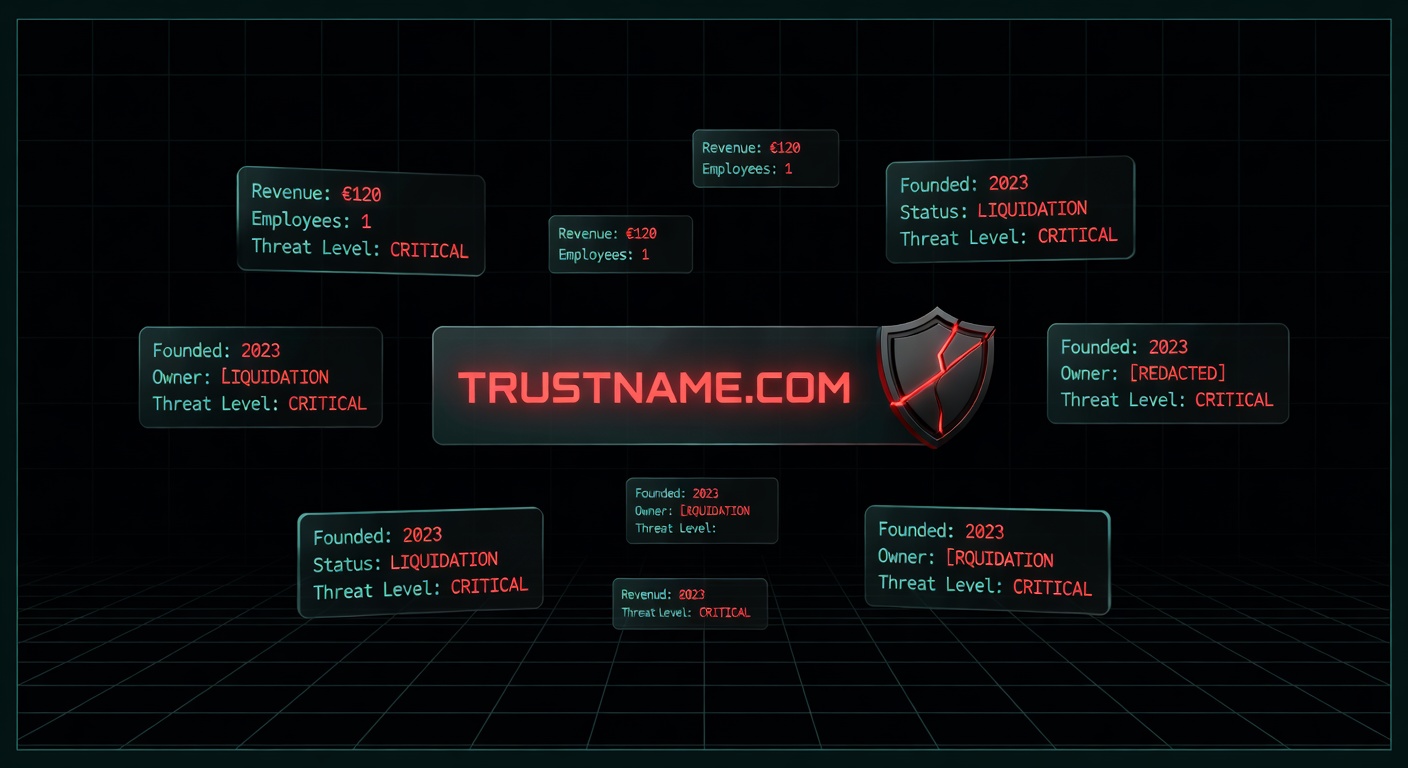
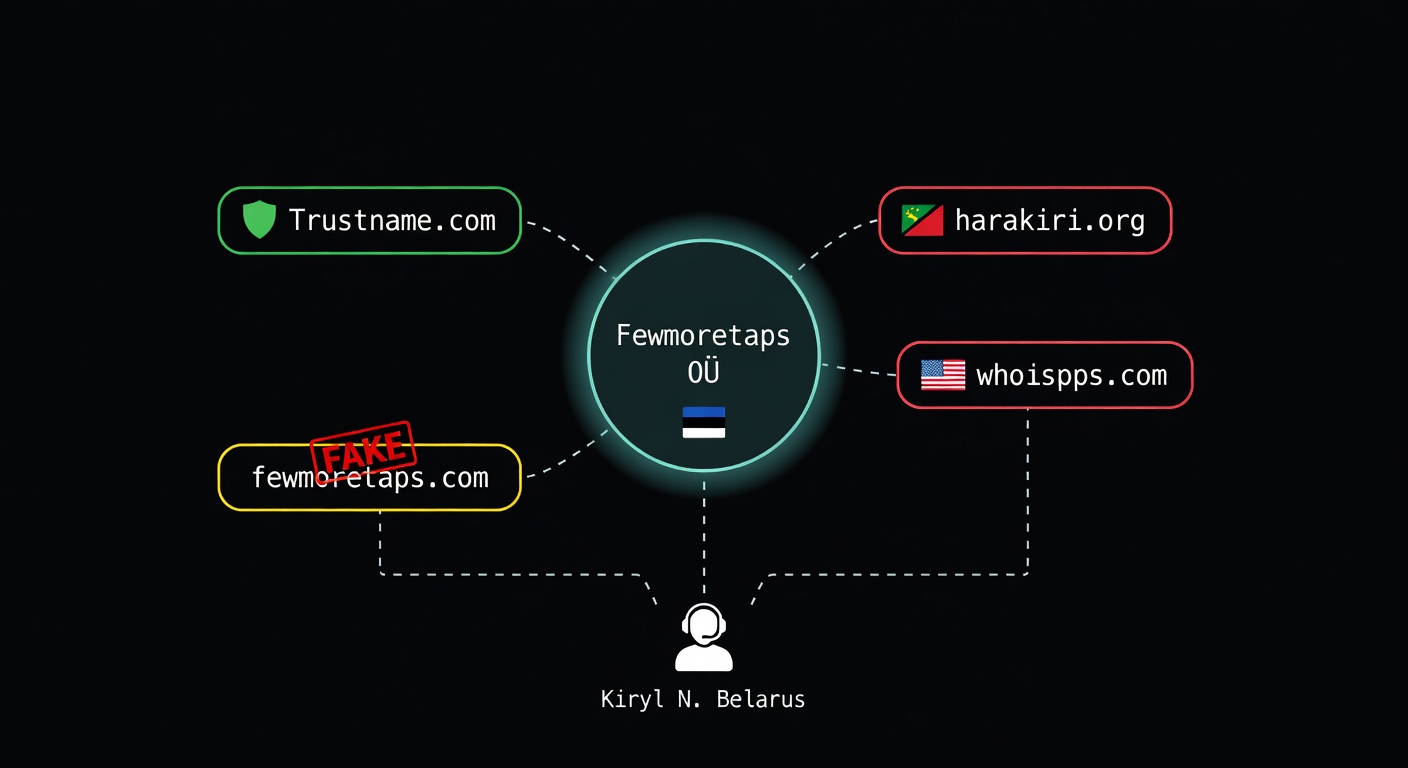
Trustname.com is operated by Fewmoretaps OÜ — an Estonian shell company with unpaid share capital, €120 in declared annual revenue, one employee, negative equity of −€71,648, and a deletion notice published in the Estonian Business Registry. The company literally calls itself a “bulletproof domain registrar” in its own DNS TXT record. Both owners are Belarusian citizens. The registrar is actively being used to register fake Elon Musk crypto casinos hidden behind its own offshore privacy proxies.
The Estonian Shell: Fewmoretaps OÜ
Fewmoretaps OÜ is registered with the Estonian Business Registry under reg. code 16354846, VAT EE102702659, at a virtual office address — Roseni tn 13, Tallinn. Incorporated 01.11.2021 with €2,500 in share capital that was never paid in (“Established without making contribution” — Annual Report 2022).
fewmoretaps.com.Ownership chain
Financials: €120/year and Growing Losses
Mandatory Estonian annual reports are public. The numbers are unambiguous:
Financial table (EUR)
| Metric | 2022 | 2023 | 2024 |
|---|---|---|---|
| Revenue | €0 | €0 | €120 |
| Net loss | 0 | −20,711 | −50,937 |
| Staff costs | 0 | 8,324 | 24,084 |
| Long-term liabilities | 0 | 35,370 | 175,310 |
| Equity | 0 | −20,711 | −71,648 |
| Employees (FTE) | 0 | 1 | 1 |
ICANN accreditation fee alone is ~$4,000/year. AWS (3 Kafka brokers + EKS + S3) runs $500–2,000/month. OpenSRS wholesale domain costs €8–12 per .com. Plus Vercel, Freshdesk, Brevo, Stripe fees. Minimum operating cost: €35–50K/year. Declared revenue: €120. The gap is funded by €175,310 in “long-term liabilities” from undisclosed sources.
“Bulletproof” — Their Own Word
This is not marketing framing by PhishDestroy — it is literally on Trustname’s own DNS TXT record:
“Trustname is ICANN-accredited and the world’s most trusted independent domain registrar for privacy-conscious individuals and businesses in sensitive niches. Count on us to be your bulletproof domain registrar. We’re trustworthy, we’re reliable, and we’re affordable.”
Verifiable by anyone with a DNS client: dig TXT trustname.com. In the hosting and registrar industry, “bulletproof” is a term of art — it unambiguously refers to services that resist abuse takedown requests and serve operators of illicit content.
The Scam Casino Network
Within a single week (April 8–13, 2026), six fraudulent crypto casino domains were registered through Trustname, all hidden behind Trustname’s own privacy proxies:
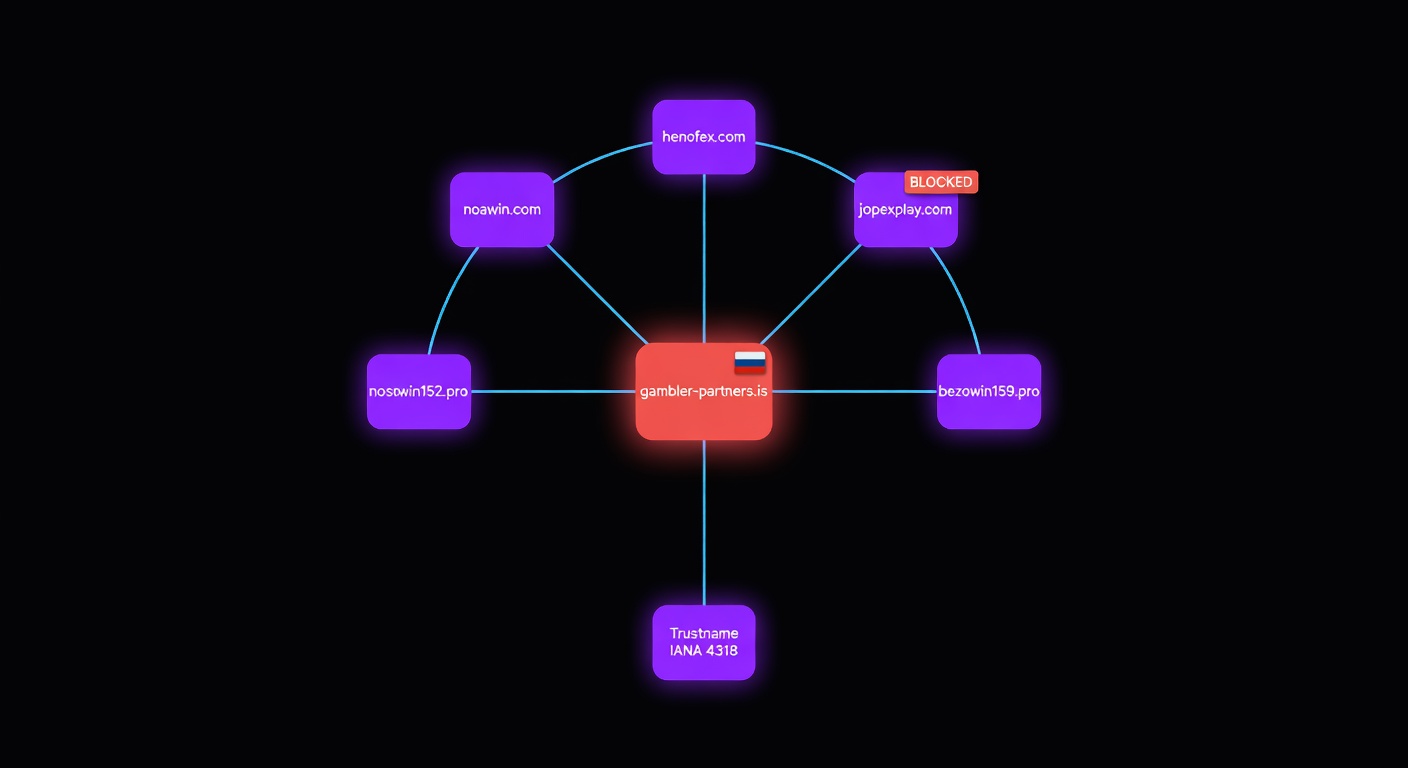
gambler-partners.is.Confirmed scam domains (all registered via IANA #4318)
noawin.com
Proxy: Perfect Privacy LLC (KN)
henofex.com
Proxy: WHOIS Privacy (FL)
jopexplay.com
Proxy: WHOIS Privacy (FL)
bezowin159.pro
Proxy: WHOIS Privacy (FL)
noswin152.pro
Proxy: WHOIS Privacy (FL)
bazowin781.pro
Proxy: WHOIS Privacy (FL)
JavaScript analysis of noawin.com revealed API calls to https://gambler-partners.is/api, /api/slots, /payser, and image CDN https://pictures-cdn.is/. The gambler-partners.is website itself displays a Russian-language admin panel titled “Gambler | Главная” (Gambler | Home) with description “Панель для управления трафиком” (Traffic management panel). Same codebase, same backend, same CDN — this is an organized scam casino network.
Offshore Privacy Proxies — Owned by the Registrar
Trustname does not use independent third-party privacy services. It operates its own:

harakiri.org
whoispps.com
When an abuse complaint arrives for a privacy-protected domain, Trustname receives it and forwards it to… itself. The whoispps.com site openly states that “physical mail is discarded.” This is not privacy — it is an abuse-laundering structure engineered to ensure complaints go nowhere.
Where Does the Money Go?
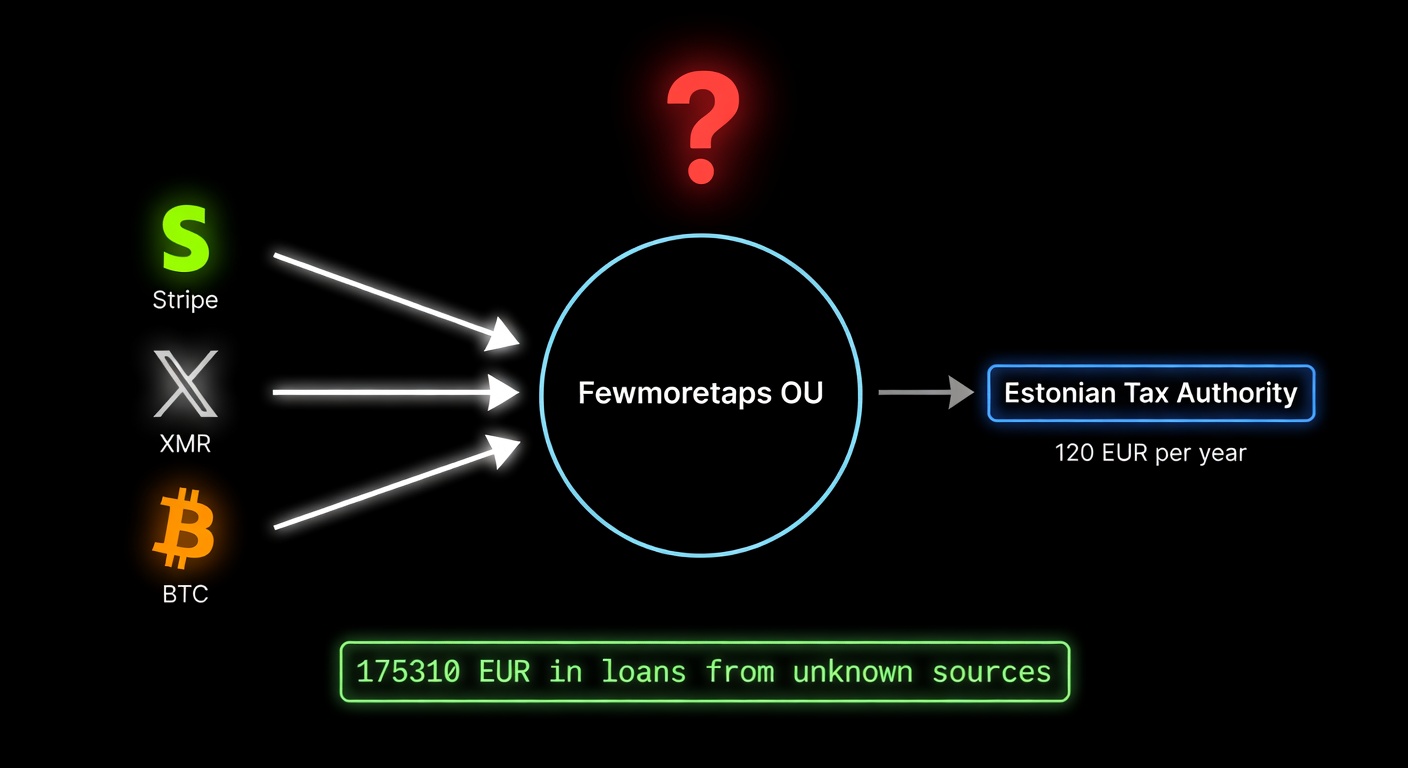
The Trustname platform accepts card payments via Stripe (/v2/users/billing/stripe/payment-methods) and cryptocurrency via the following wallet addresses embedded in the authenticated API notification endpoint:
ETH: 0xdee6582dc53fa56180311393018121c6f1e8bd7c
LTC: MEREvHtzqAUTJ1XvEevmci8UqMnDvfe2ri
ZEC: t1d19KevpcXpesr9XA9UUyMW9XGYVDxkK9S
XMR: 8B5N29BocrTjkRCeGCARnkhKgBeHBhg4oH7ay4RfXfnL7RqBdyiuL4k6iN4GVUVxt1EQJvZRqLg8n4qgCNWmYHQQDZmfytMThe acceptance of Monero (XMR) — a cryptocurrency specifically designed to be untraceable — alongside a regulated KYC-requiring processor (Stripe), while declaring €120 in annual revenue to Estonian tax authorities, creates a compliance paradox. A single .com registration at wholesale cost (~$13) already exceeds the declared revenue for the entire year.
Estonian law (Money Laundering and Terrorist Financing Prevention Act) requires Virtual Asset Service Providers to hold a license from the Financial Intelligence Unit. Does Fewmoretaps OÜ hold this license? If not, accepting cryptocurrency payments for services may itself constitute a regulatory violation.
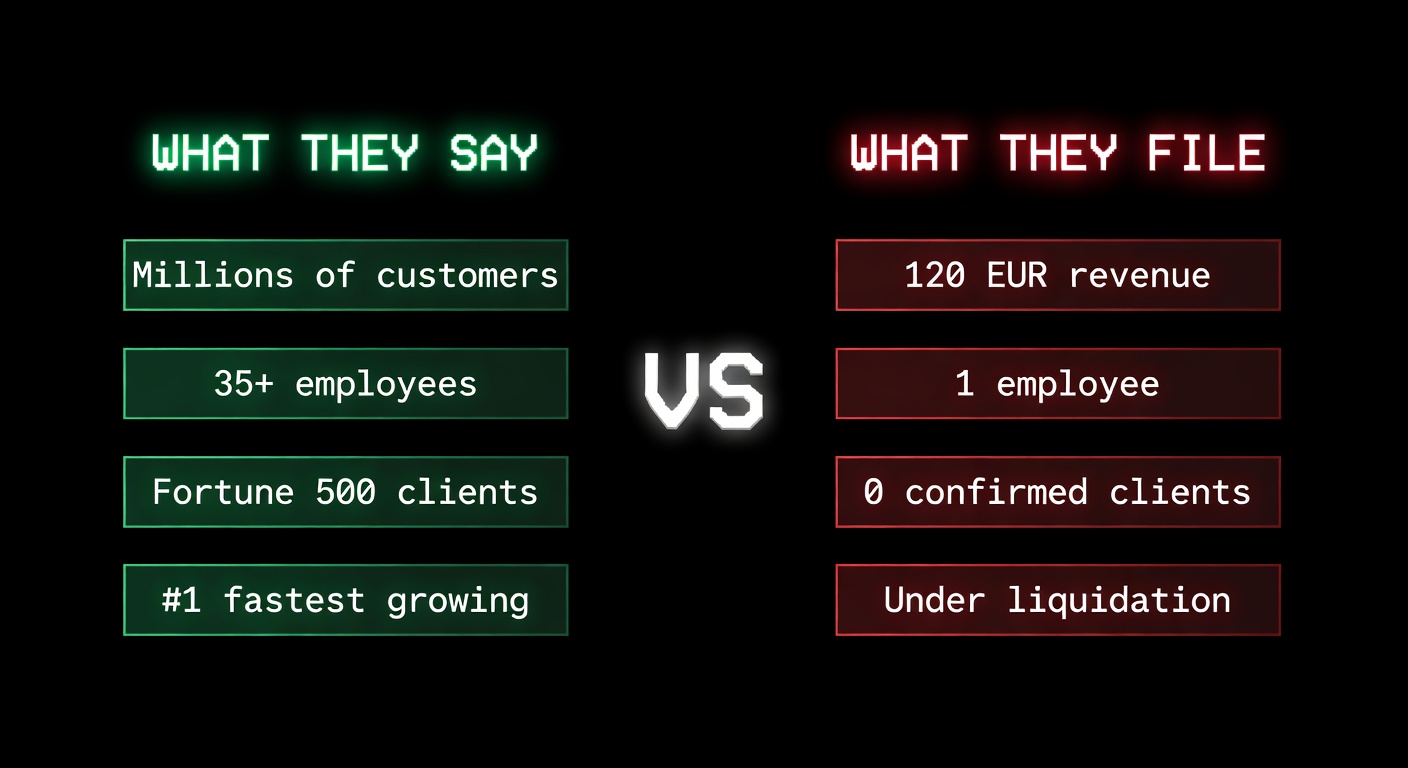
Marketing Claims vs. Tax Filings
What they tell customers
- “#1 fastest growing independent domain registrar in 2025”
- “Trusted by millions of domain owners”
- “Trusted by Fortune 500 companies”
- “A team of over 35 people based in various locations around the world”
- Offices listed in London, Beverly Hills, Melbourne
- Clients: McDonald’s, Vodafone, Adidas, Tata, Yahoo, BCG (fewmoretaps.com logo wall)
- “Since 1997” (fewmoretaps.com)
What they file with the Estonian tax authority
- €0 revenue in 2023, €120 revenue in 2024
- 1 employee (FTE) in both years
- Equity −€71,648, unpaid capital of €2,500
- Virtual office at Roseni tn 13, Tallinn
- Incorporated 2021, not 1997
- Company under liquidation
Fake testimonials (“Wall of Love”)
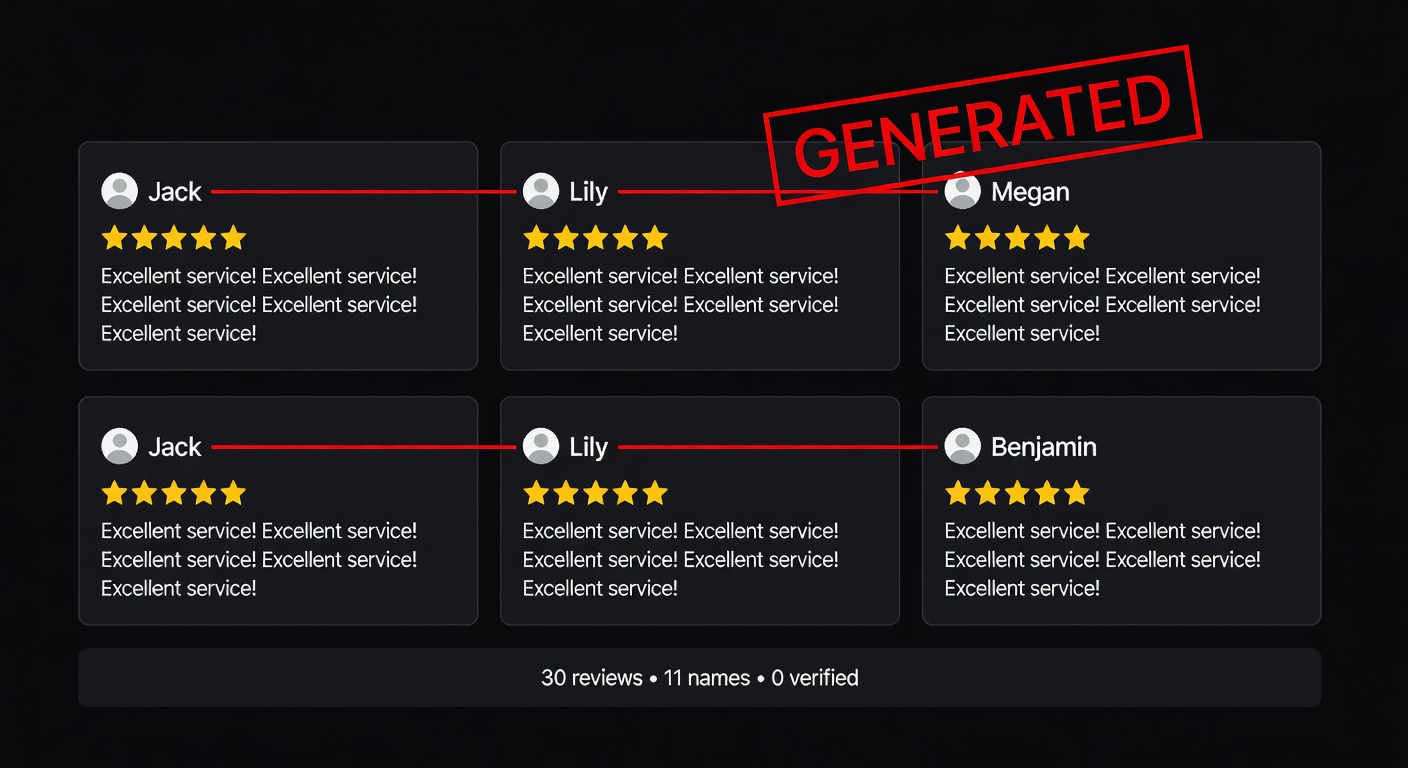
Analysis of the trustname.com/wall-of-love page: 30 “customer reviews,” only 11 unique first names. “Jack” appears five times. “Lily” six times. “Megan” three times. All reviews are generic single-line praise in a uniform writing style. There are no independent review platform links. No verifiable customer identities. For comparison, Namecheap and Porkbun have thousands of verified reviews on Trustpilot and G2.
Infrastructure & Security Exposure
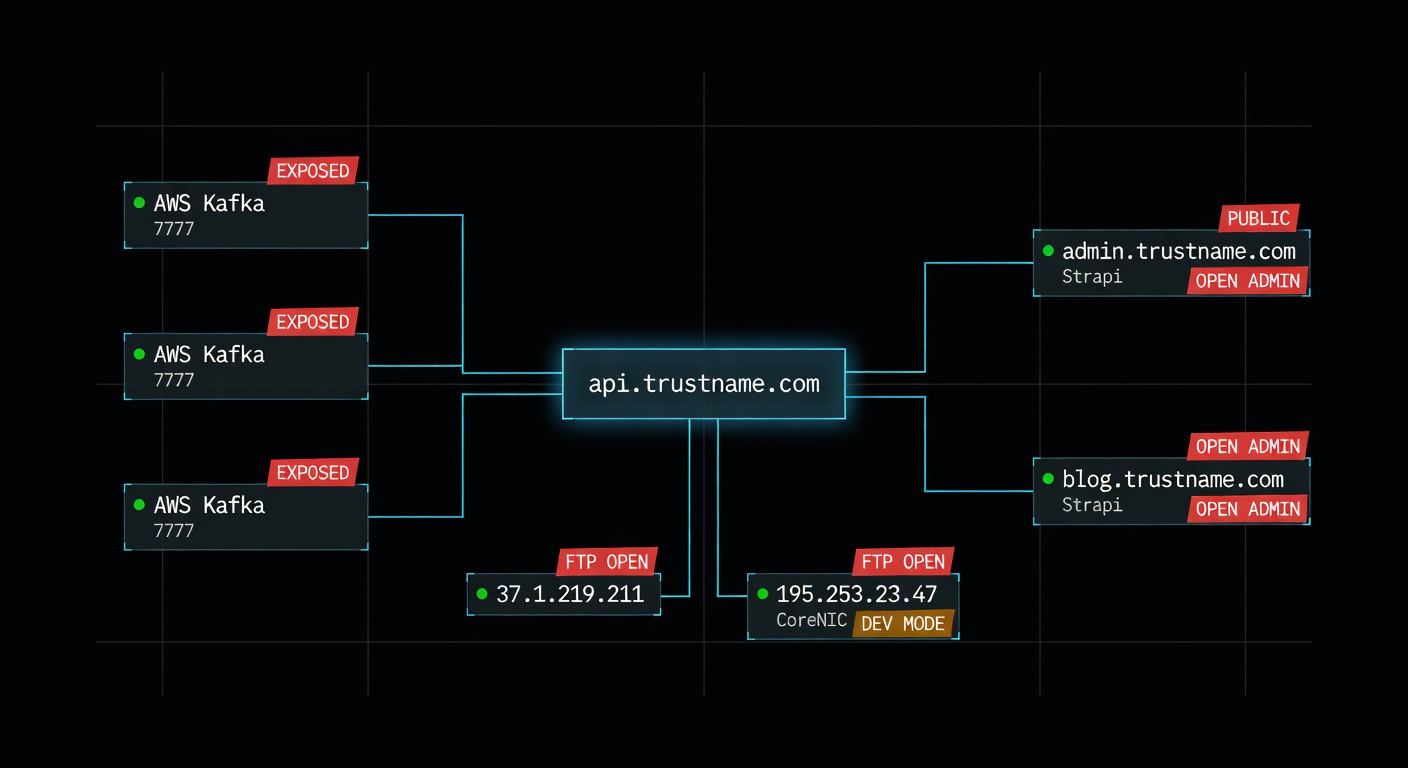
trustname.com (Vercel / Next.js)
├── api.trustname.com Fastify API (Swagger behind Basic Auth only)
├── admin.trustname.com React-Admin panel (publicly accessible)
├── blog.trustname.com Strapi CMS (admin UI exposed)
├── support.trustname.com Freshdesk (EU instance)
└── whois-fewmoretaps.corenic.net Knipp DomainSRS (JSF Development mode)
fewmoretaps.com (WordPress) origin: 37.1.219.211
Open ports: FTP:21 (vsftpd 3.0.5), SSH:22, HTTP:80, HTTPS:443
AWS eu-central-1 (EKS Kubernetes):
35.156.29.145 / 18.196.68.81 / 52.28.105.156
Port 7777 — Apache Kafka (Strimzi)
SSL cert CN: kafka-staging-kafka SAN: staging.kafka-0.trustname.com
Namespace: backend-staging
Upstream registrar: OpenSRS (Tucows)
Invoicing: Quaderno · Payments: Stripe + Crypto
Email: Brevo · Analytics: Google, Fuago
S3: domain-registrar-strapi-media (eu-central-1, leaked via CSP header)- Admin panel publicly accessible (
admin.trustname.com) — login-only protection, no IP allowlist. - Strapi CMS admin UI reachable at
blog.trustname.com. - JSF in Development mode on the CoreNIC WHOIS system.
- Three AWS Kafka brokers exposed to the public internet on port 7777; SSL SAN leaks Kubernetes namespace.
- Origin IPs bypass Cloudflare — direct access possible.
- FTP (vsftpd) open on the fewmoretaps origin server.
- Swagger / OpenAPI behind Basic Auth only on
api.trustname.com/api-json.
Timeline
trustname.com (previous owner).fewmoretaps.com registered. Entire marketing site created in 5 days by a single WordPress user “riseup”.whoispps.com privacy proxy domain registered.Who Enables This?

To ICANN
- How did a company with €0 revenue and 0 employees at the time of application obtain ICANN accreditation? What due diligence was performed?
- A registrar whose DNS TXT record literally says “bulletproof domain registrar” and “sensitive niches” — how does this align with the Registrar Accreditation Agreement?
- The registrar is now under liquidation in Estonia. What happens to ongoing abuse complaints for domains registered through IANA #4318?
- Both owners are citizens of Belarus — a country under comprehensive EU and US sanctions since 2020. Was this disclosed during accreditation?
To OpenSRS (Tucows)
- OpenSRS provides the upstream API Trustname uses to register domains (confirmed by
opensrsOrderIdin transaction data). Does Tucows conduct compliance reviews of resellers who openly market themselves as “bulletproof”? - Six scam casino domains — including one already flagged by Cloudflare — were registered through OpenSRS via Trustname in one week. What automated fraud detection exists at the reseller level?
To AWS, Stripe, Vercel, Cloudflare
- AWS: the EKS cluster, S3 bucket, and three publicly exposed Kafka brokers sit in
eu-central-1. AWS AUP prohibits fraud-facilitating services. - Stripe: card payments are processed via
/v2/users/billing/stripe/payment-methods. Stripe’s Restricted Business list prohibits services facilitating illegal activity. Has the client portfolio been reviewed? - Vercel:
trustname.comandadmin.trustname.comare hosted on Vercel. Vercel AUP prohibits “services that promote fraudulent schemes.” - Cloudflare:
jopexplay.comis flagged as “Suspected Misleading Website.” The other five casinos using identical templates remain active. Why the inconsistency?
About Belarus & Monero
- Both owners are Belarusian tax residents. Worldwide income should be declared in Belarus under Belarusian tax law. Belarusian authorities have no MLAT with most Western jurisdictions — enforcement effectively dead-ends.
- Trustname accepts Monero (XMR), a cryptocurrency designed to be untraceable. How are XMR payments reported for VAT, AML, and Estonian financial reporting? The annual report shows €120. Does that include crypto? If not, where does it go?
Indicators of Compromise
Registrar identifiers
IANA ID: 4318
WHOIS Server: whois.fewmoretaps.com
Abuse email: abuse@trustname.com
Abuse phone: +372.6884747Infrastructure
trustname.com
fewmoretaps.com
harakiri.org
whoispps.com
gambler-partners.is
pictures-cdn.is
37.1.219.211 fewmoretaps.com origin (FTP, SSH, HTTP, HTTPS)
195.253.23.47 CoreNIC WHOIS origin
35.156.29.145 AWS Kafka broker
18.196.68.81 AWS Kafka broker
52.28.105.156 AWS Kafka brokerConfirmed scam domains
noawin.com henofex.com jopexplay.com
bezowin159.pro noswin152.pro bazowin781.proVerdict
Trustname.com is not a “privacy-focused registrar.” It is a purpose-built infrastructure for enabling online fraud:
- Estonian shell company with unpaid capital and two Belarusian owners
- Zero legitimate revenue despite active domain registration operations
- Privately-owned “independent” offshore privacy proxies in Saint Kitts and Florida
- Acceptance of untraceable cryptocurrencies (Monero, Zcash)
- Dozens of freshly registered scam casino domains on identical templates
- A DNS TXT record where they literally call themselves bulletproof
- Company currently under liquidation — an exit strategy already in progress
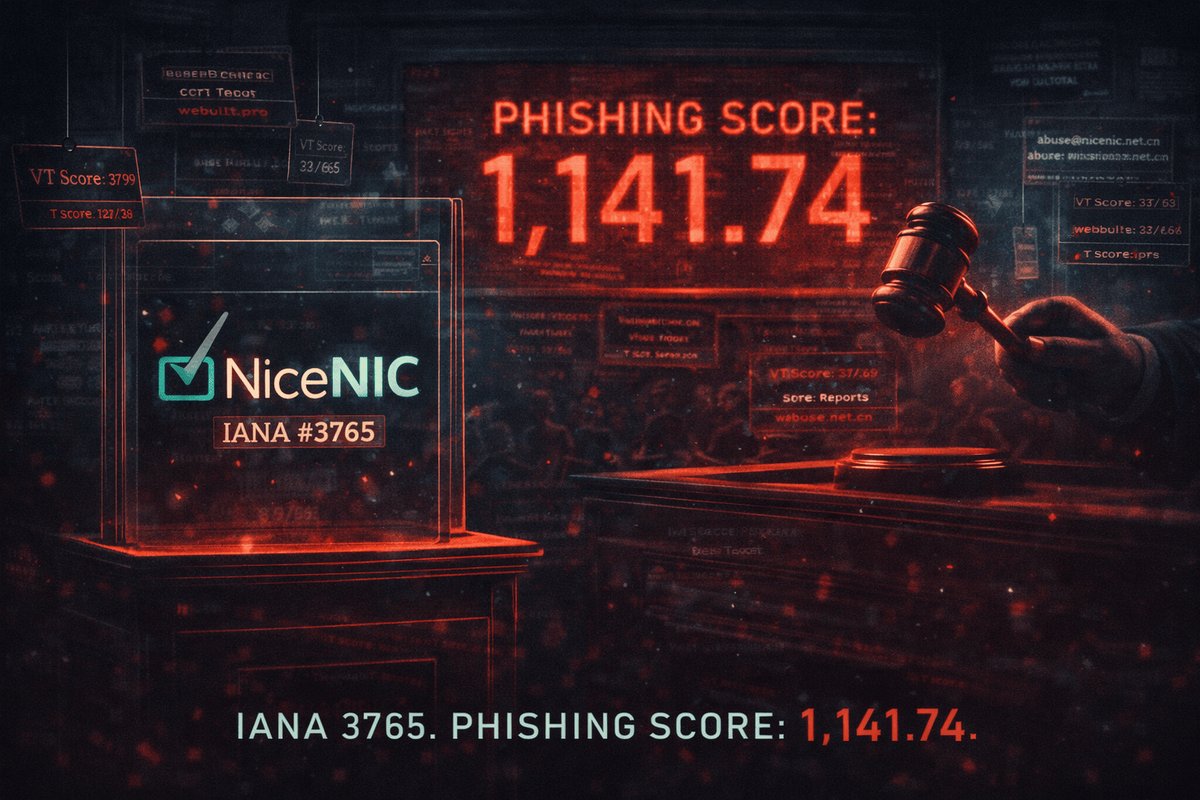
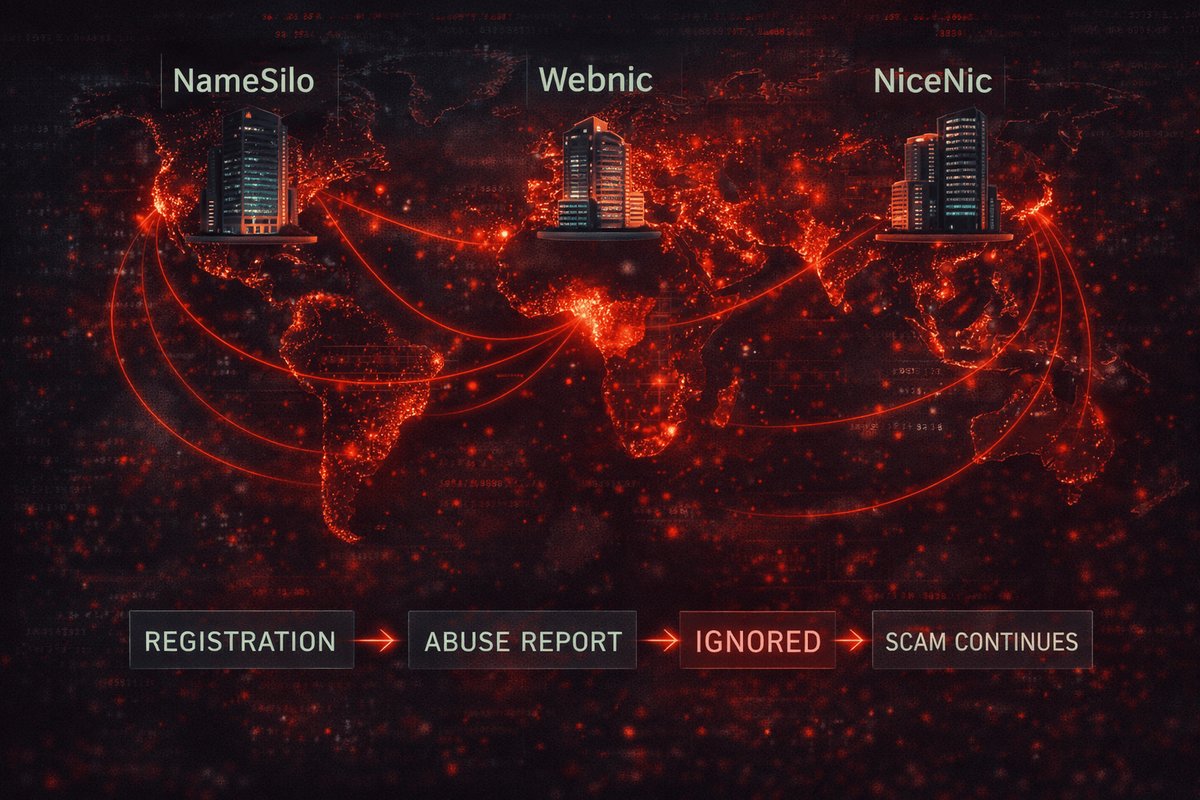
ICANN and OpenSRS (Tucows) should review the accreditation of IANA #4318. Domains registered through Trustname’s privacy proxies warrant enhanced scrutiny on abuse reports. Until then, PhishDestroy flags every Trustname-registered domain in our scanner with a registrar warning, as we do for NiceNIC and NameSilo.
Related Research
Sources & Verification
Every claim in this report is backed by publicly accessible records or by data obtained through the researcher’s own authenticated account. Below are the primary sources with instructions for independent verification.
Corporate registry & tax records
| Claim | Source | How to verify |
|---|---|---|
| Company registration, owners, status, deletion notice | Estonian Business Registry (Äriregister) | ariregister.rik.ee — search reg. code 16354846 |
| Annual reports 2022, 2023, 2024 — revenue, equity, employees | Estonian Business Registry — mandatory filings for OÜ entities | Same registry → “Annual reports” tab. Reports are public. |
| Owner names, IDs, nationality (Tsyvinski, Nestsiarovich) | Annual report shareholder pages (Osanikud) | Report 2022 p.6 (Tsyvinski); Reports 2023–2024 (Nestsiarovich) |
VAT registration EE102702659 | Estonian Tax & Customs Board | Verify via EU VIES |
ICANN & registrar identifiers
| Claim | Source | How to verify |
|---|---|---|
IANA ID 4318 — ICANN accreditation | ICANN Accredited Registrar list | icann.org/en/accredited-registrars — search “Fewmoretaps” or “4318” |
Abuse contact (abuse@trustname.com, +372.6884747) | WHOIS records for any Trustname-registered domain | whois trustname.com via any RDAP/WHOIS client |
WHOIS server whois.fewmoretaps.com | WHOIS records | Listed on every domain registered through IANA #4318 |
WHOIS & DNS evidence
| Claim | Method |
|---|---|
| DNS TXT record — the literal “bulletproof” quote | dig TXT trustname.com or DNSChecker |
| Privacy proxy WHOIS data (Perfect Privacy LLC, WHOIS Privacy LLC) | whois noawin.com, whois harakiri.org, whois whoispps.com |
| Scam-domain registration via Trustname | WHOIS port 43 query to 195.253.23.47:43 or any public WHOIS service |
| MX, NS records for infrastructure mapping | Standard DNS queries (dig NS trustname.com, dig MX) |
Marketing claims (live + archived)
- trustname.com/about — “over 35 people”, “Kir N. CEO”
- trustname.com homepage — “#1 fastest growing”, “trusted by millions”, “Fortune 500”
- trustname.com/wall-of-love — the 30 reviews / 11 unique first names
- fewmoretaps.com — “since 1997”, “100% project delivery”, Fortune 500 logo wall
- fewmoretaps.com/enquiry — London / Beverly Hills / Melbourne addresses
- whoispps.com — “Physical mail is discarded”
- harakiri.org — Perfect Privacy LLC, St. Kitts & Nevis
- Historical snapshots: Wayback Machine for trustname.com
Technical infrastructure (non-intrusive)
Casino-network analysis
- Casino content (“Elon Musk’s Official Casino”) —
curl https://henofex.com - Cloudflare phishing block —
curl https://jopexplay.comreturns Cloudflare interstitial - Shared template (identical chunk hashes) — compare
_next/static/chunks/across all six domains - Russian-language admin panel —
curl https://gambler-partners.isreturns title “Gambler | Главная”
Tools used
DNS / WHOIS: dig, nslookup, whois
Port scanning: nmap (service / version detection only)
HTTP: curl (header + content retrieval)
SSL: openssl s_client
JavaScript: manual deobfuscation of publicly served bundles
PDF: PyPDF2 (annual report text extraction)Financial-cost methodology
The €35–50K minimum operating cost figure is built from public price points:
- ICANN accreditation fee: ~$4,000/year (ICANN published rates)
- OpenSRS wholesale .com: $8–12/domain (Tucows reseller pricing)
- AWS eu-central-1 (3× m5.large for Kafka + EKS control plane + S3): $500–2,000/month (AWS Pricing Calculator)
- Vercel Pro: $20/month, Freshdesk: $15/agent/mo, Brevo: $25/mo (public pricing pages)
- Reported staff costs for 2024: €24,084 (the company’s own annual report)
Ethics & Methodology
- Public records research (Estonian Business Registry, ICANN, VIES, WHOIS, DNS).
- Non-intrusive technical reconnaissance: DNS queries, HTTP header reads, SSL certificate inspection, public-bundle JavaScript analysis,
nmapservice detection without exploitation. - Authenticated API testing using the researcher’s own legitimately registered Trustname account.
- Cross-referencing of Wayback Machine snapshots for marketing claims.
- No brute-force attacks against any login.
- No SQL injection, RCE, or other exploitation attempts.
- No unauthorized access to any system, account, or data.
- No data exfiltration from protected endpoints.
- No modification of any data, even where misconfigurations would have allowed it.
- Admin API endpoints were tested for BOLA (Broken Object Level Authorization) — RBAC was confirmed properly implemented; user tokens are correctly rejected by admin endpoints.
Disclosure & Reporting Position
This investigation has been published in full as a form of public disclosure. PhishDestroy is an OSINT research team and not a regulated reporting entity, so there is no legal duty under Estonian KarS § 306 or comparable EU statutes to file a private report with authorities — that obligation attaches only to banks, VASPs, and similar regulated obliged-entities.
If abuse reports filed against domains registered through IANA #4318 continue to be ignored, this dossier will be escalated formally to:
- ICANN Compliance — icann.org/compliance/complaint · RAA § 3.7.8 (WHOIS accuracy) and § 3.18 (abuse handling)
- Tucows / OpenSRS — upstream registrar;
abuse@tucows.com,compliance@opensrs.com - CERT-EE (RIA) —
cert@cert.ee - Estonian MTA (Maksu- ja Tolliamet, Tax & Customs Board) — tax-fraud tip line
vihjeliin@emta.ee - Estonian FIU (Rahapesu Andmebüroo) —
rab@politsei.eefor AML and unlicensed VASP activity - Platform abuse desks — AWS Trust & Safety, Stripe Risk, Vercel Abuse, Cloudflare Trust & Safety
- EU FIU.net via the Estonian FIU — for the Belarus-sanctions component
For now, formal escalation has been deliberately deferred: the registrar entity is already in liquidation in Estonia, the operators are based in Belarus (no MLAT ⇒ enforcement dead-end), and a public report carries more weight than a queued ticket. We will reassess if circumstances change — or if anyone reading this brings an argument that does.
This investigation was conducted using exclusively OSINT methods and non-intrusive technical analysis. All data sources are publicly accessible or were obtained through the researcher’s own authenticated account on the platform. No unauthorized access was performed at any stage. Corrections, counter-evidence, or additional data: @PhishDestroy_bot · @Phish_Destroy · github.com/PhishDestroy.