Anatomy of a Crypto Drainer: How $1.93B Vanished in 6 Months
A drainer doesn't steal your seed phrase. It steals your signature. One click — one click on the wrong "Claim", "Verify", or "Connect Wallet" — and a chain of pre-built smart contracts empties your holdings before you can move your finger off the trackpad.
What a drainer actually is
A crypto drainer is a phishing tool purpose-built for Web3. It doesn't try to phish your password or extract a private key. Instead it gets you to sign a transaction — usually an approve(), setApprovalForAll(), or an off-chain Permit message — that hands the attacker permission to move your assets at will. The wallet stays "yours". The funds don't.
The model is brutally efficient because it abuses legitimate blockchain primitives. Your private key is never compromised. There is no malware on your machine. There is just one signature, on one transaction, that on-chain analysts will see and whose effect cannot be reversed by any authority.
According to Chainalysis, a drainer is "a phishing tool designed for the web3 ecosystem" that pretends to be a legitimate dApp. Group-IB, Check Point Research, and ScamSniffer have catalogued thousands of campaigns built on this exact mechanic.
The 6-step kill chain
Every drainer attack — Inferno, Pink, Angel, MS, CLINKSINK, Rugging, and the dozens of unnamed forks — follows the same six stages. The art is in compressing all of them into the seconds between a wallet connection and a confirmed transaction.
1. Lure
Fake airdrops, sponsored Google/X ads, compromised verified accounts (the SEC and Mandiant accounts have both been used as drainer megaphones), Discord verification bots, fake NFT mints, "exclusive" beta invites, and IP-licensing scams. Whatever the wrapper, the goal is to get you onto a domain the attacker controls.
2. Connect
You hit "Connect Wallet". MetaMask, Rabby, WalletConnect, Phantom — all fine, all expected. The drainer JavaScript now has read access to your wallet object via window.ethereum (or the equivalent), and starts firing eth_call requests in the background.
3. Recon
The drainer enumerates your holdings: native balance, ERC-20 tokens, NFT collections, DeFi positions across multiple chains. It hits CoinGecko-style price oracles to USD-rank everything. Premium kits like Inferno Drainer store their config on-chain (BNB Chain) so it can be updated without redeploying the JS payload.
4. Sign
The dApp prompts you to "Verify ownership", "Claim airdrop", "Approve collection", or "Sign to enter". Wallet UI shows what looks like a benign message. In reality the calldata is carefully chosen to maximize damage — see the next section.
5. Drain
The moment your signature lands, the attacker calls transferFrom() from a separate wallet (operational separation — the "Address" that received the approval is never the "Receiver" that holds the loot). Premium kits batch native ETH, ERC-20s, ERC-721/1155 NFTs, and Permit2 transfers in a single multicall. Net latency from signature to fund movement: seconds.
6. Launder
Funds route through SushiSwap / Uniswap (legitimate DEXs are deliberately allow-listed by most security tools), then through bridges to other chains, then through Tornado Cash forks, then to Monero. The $284M Trezor incident ended up in XMR within hours.
Your wallet (before signing)
Attacker contract (after one signature)
One signed Permit2 message can authorize the entire batch. No second confirmation. No recovery.
The four killer payloads
Every drainer in the wild uses some combination of these four primitives. Each one is a legitimate ERC standard or RPC method. There is no "patch" — only awareness.
1. approve(spender, type(uint256).max) — ERC-20 unlimited spend
The classic. You approve a token contract for the maximum possible amount (2^256 − 1) to a spender address you don't control. The spender — i.e. the attacker — then calls transferFrom(you, attacker, balance) at their leisure. The approval persists forever unless you explicitly revoke it via Revoke.cash or the token contract directly.
2. setApprovalForAll(operator, true) — full NFT collection
Worse than ERC-20 approval, because it's all-or-nothing per collection. One signature = every NFT in that contract is now movable by the attacker. This is how Seth Green lost 4 Bored Apes in 2022 and how a single victim lost 14 BAYCs to the fake "Forte Pictures" licensing scam in December 2022.
3. EIP-2612 / Permit2 off-chain signatures
This is the 2024–2026 weapon of choice. Instead of an on-chain approve() (which costs gas and shows up clearly in your wallet), the attacker collects an off-chain EIP-712 signature via eth_signTypedData_v4. No transaction. No gas from your side. Just a pop-up that says "Sign this message". The wallet UI for typed-data signing is notoriously hard to read, and Uniswap's Permit2 turns one signature into approvals for multiple tokens at once.
See Blockaid's full Permit2 case study for a real attack walkthrough including the SushiSwap-routing trick that hides ETH drainage inside what looks like a normal swap.
4. Direct seed-phrase social engineering
Not technically a "drainer" by the narrow definition — but the highest-yield variant in 2026. The January 2026 Trezor incident didn't bypass any encryption. A "support agent" called the victim, walked them through a fake "verification" process, and got them to read out the recovery seed. Result: 1,459 BTC + 2.05M LTC = $284M, 71% of all crypto theft losses for that month, converted to Monero before the news cycle picked it up.
Hardware wallets prevent remote key extraction. They do not prevent you from typing your seed into a phisher's website. Use a BIP-39 passphrase.
The Drainer-as-a-Service economy
None of the actors who actually steal your money write the code. They rent it. Drainer-as-a-Service (DaaS) is a fully commoditized B2B market with branding, pricing tiers, support channels, version releases, and an obvious downward pressure on operator commissions.
Entry cost for an affiliate: a $5,000–$10,000 deposit, sometimes a turnkey kit for the same. The affiliate keeps 75–95% of stolen funds and outsources every technical concern — JS payload, smart contract, hosting, laundering pipeline, even 24/7 Telegram support — to the operator. SentinelOne and the IMC 2025 academic study trace the supply chain in detail.
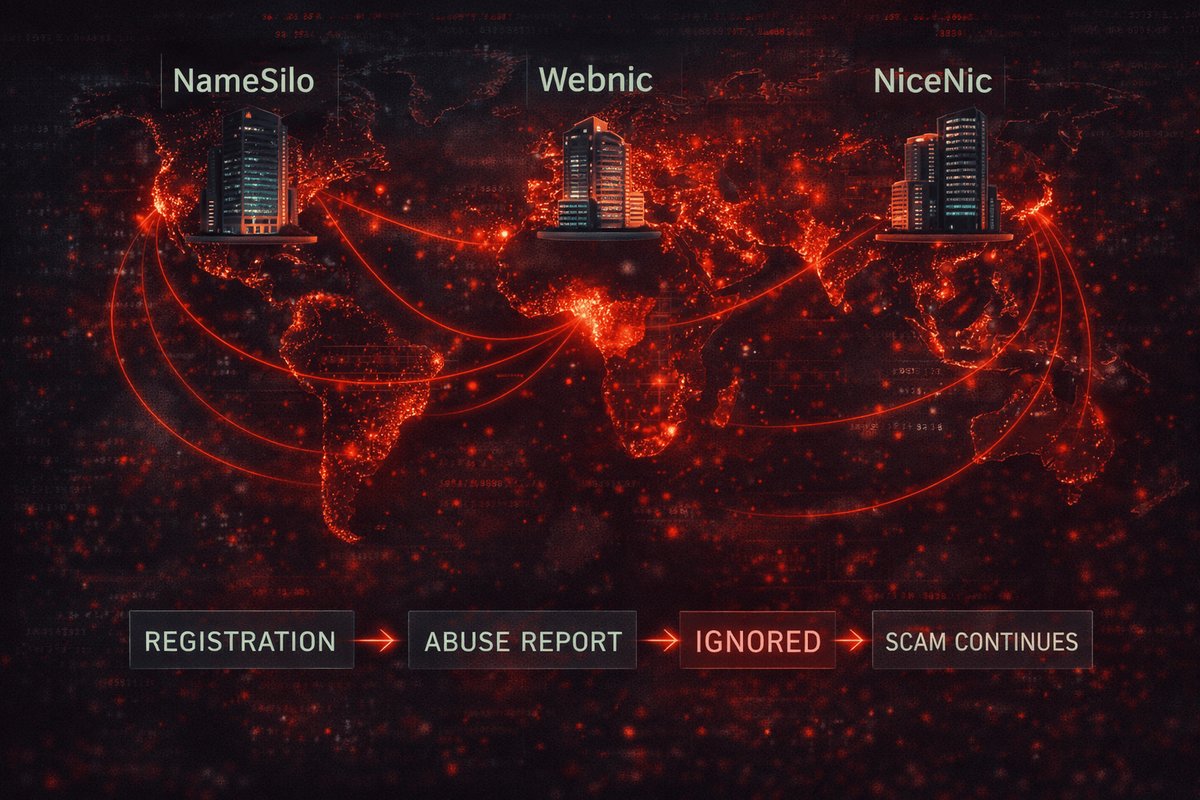
This is why one-off whack-a-mole takedowns aren't enough — and why registrars that ignore abuse are the actual bottleneck. PhishDestroy has documented and reported 16,000+ Inferno-related domains alone.
Red flags before you sign
The signature dialog is the last line of defense. If any of these are true, cancel — there is no legitimate flow that requires them:
- You arrived via a sponsored search result, DM, or email link. Sponsored crypto results have been compromised at every major search engine. Always navigate from a bookmark.
- The signature is "free" / "gasless" / "off-chain". That's a Permit2-style off-chain signature. Read the typed-data fields. If
spenderis unfamiliar, walk away. - The amount is
uint256.max,0xfff…fff, or "unlimited". Almost no legitimate flow needs unlimited approval. - The function is
setApprovalForAllon a collection you don't recognize. Or for an "operator" that isn't OpenSea / Blur / LooksRare. - The site asks you to switch chains right after connecting. Multi-chain extraction loop in progress.
- The destination contract was deployed less than 7 days ago. Inferno-class drainers rotate intermediate contracts every 24h.
- You feel rushed. Countdown timers, "claim ends in 4:32", "only 12 spots left" — every drainer template ships with these.
- "Customer support" reached out to you first. Trezor, Ledger, MetaMask, Coinbase, Binance — none of them DM you. Ever.
How to actually defend yourself
- Wallet segregation. Cold (hardware, majority of net worth) → operational hot wallet (1–2 weeks of activity) → burner wallet (anything new, near-zero balance). Never connect cold to a fresh dApp.
- Hardware wallet + BIP-39 passphrase. The passphrase is the difference between "$284M Trezor incident" and "attacker has your seed and finds nothing". Memorize it. Don't store it digitally.
- Transaction simulators. Blockaid, Wallet Guard, Pocket Universe, Fire — install one. They show the actual balance delta before you sign.
- Bookmark all dApps. Never type "uniswap" into Google. Never click crypto links from social media. The sponsored result is wrong far more often than you think.
- Audit your approvals weekly. Revoke.cash shows every active allowance across every chain. Revoke anything you don't actively use.
- Run any unfamiliar site through a burner first. Empty wallet, see what it asks for, then decide if it's worth a real wallet at all.
- Disable browser extensions on the wallet profile. A separate browser profile (or Brave Tor window) for Web3 only. Extensions are a documented drainer vector — see the Mend.io npm supply-chain analysis.
- Check the domain reputation. Drop the URL into PhishDestroy domain reports, urlscan, or our Telegram bot. If we've already seen it, it's flagged.
If you already signed: do this in the next 60 seconds
- Stop. Don't sign anything else, including "fix" or "recovery" prompts — those are second-stage scams piggybacking on your panic.
- Move whatever isn't drained yet. Generate a brand-new wallet (preferably hardware), and transfer the surviving assets to it. Highest value first. Treat every address derived from the compromised key as permanently burned.
- Revoke approvals on the compromised wallet via Revoke.cash — for every chain, not just Ethereum. This is a race against the attacker's automation.
- Document everything. Tx hashes, attacker addresses, timestamps, the exact URL of the phishing site. Screenshot before clearing the tab.
- Report. File with FBI IC3, your local cybercrime unit, the affected protocols (Uniswap, OpenSea, etc. — they sometimes freeze derivatives), and submit the phishing URL to @PhishDestroy_bot so we kill the infrastructure for the next victim.
- If a seed phrase was disclosed: the wallet is gone. Stop trying to "secure" it. Move on, generate fresh, learn from it.
"Drainers don't break cryptography. They break the assumption that humans can read calldata at the speed wallets ask them to. Slow down by one signature, and the entire industry of theft collapses."
Sources & further reading
- Chainalysis — Crypto Drainers: A Web3 Threat
- Group-IB — Inferno Drainer Investigation
- Check Point Research — Inferno Drainer Reloaded
- ScamSniffer — Pink Drainer 2024 incidents
- Blockaid — Step-by-step breakdown of a crypto heist
- BleepingComputer — Mandiant X hijack via CLINKSINK
- Cyber Daily — Mandiant hijack = $900K campaign
- SentinelOne — The Rise of Drainer-as-a-Service
- Gurucul — Wallet approval abuse → malware-assisted Web3 attacks
- Mend.io — npm supply-chain attack on Web3 packages
- AInvest — January 2026 Trezor $284M analysis
- IMC 2025 academic — DaaS economy measurement study
- PhishDestroy — Registrars enabling global scams
- PhishDestroy — Anatomy of a phishing takedown
- PhishDestroy — Real-time destroy-list (130K+ active threats)
What PhishDestroy does about drainers
We are a non-profit volunteer collective. We hunt drainer infrastructure 24/7 across SEO, paid ads, Discord, X, Telegram, and registrar honeypots, then we kill it.
- 785K+ phishing & scam domains tracked since 2019.
- 89K+ abuse reports filed with registrars and hosts.
- 50+ AV vendors and threat-intel platforms ingest our feed.
- <0.5% false-positive rate across 100K+ validated reports.
- Free, public, immutable evidence archive on GitHub + HuggingFace.
Spotted a drainer? Send the URL to @PhishDestroy_bot. We'll have the abuse report filed before your coffee gets cold.