fortcomp[.]lol
Forensic brief
Read full brief
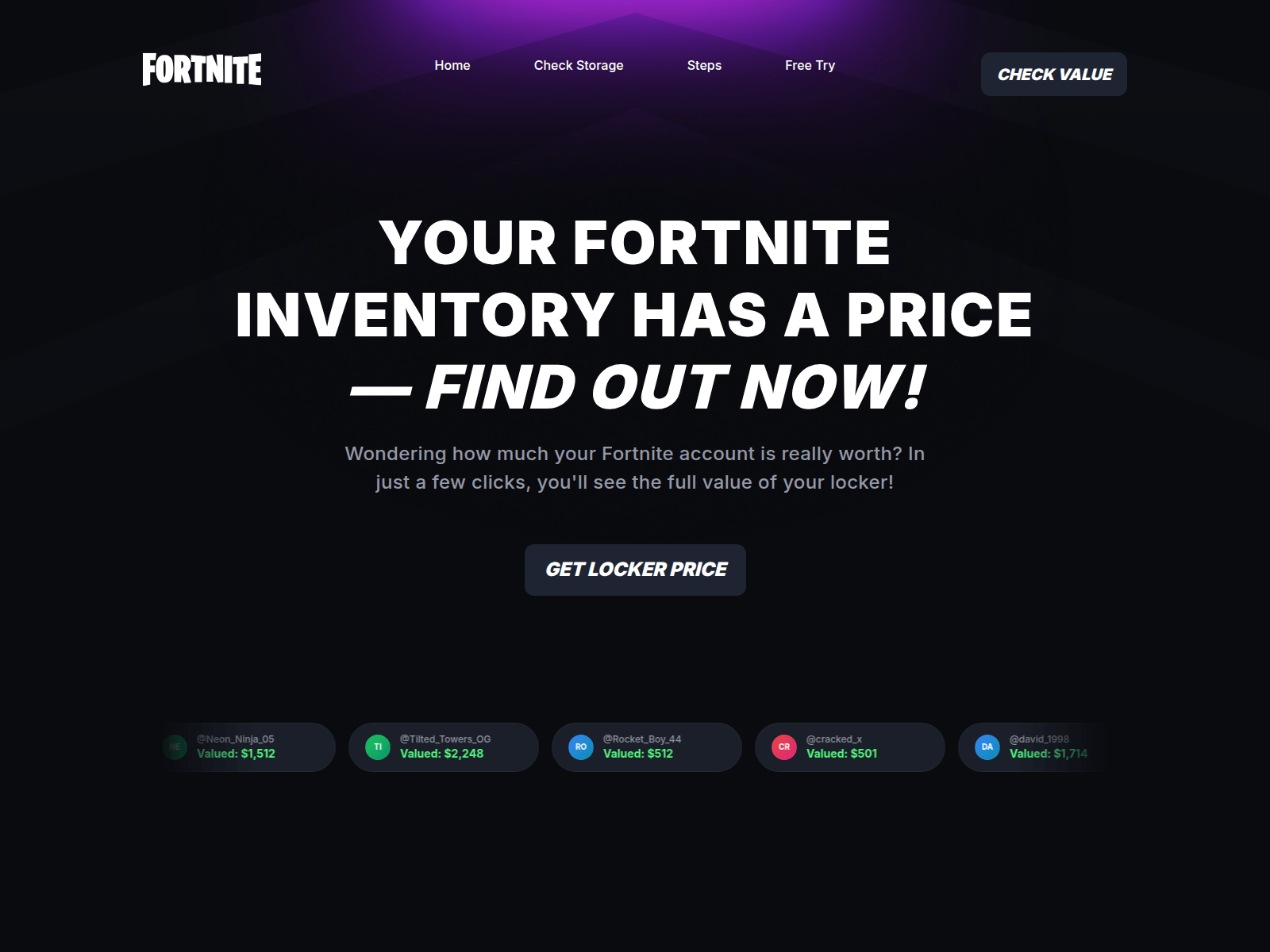
PhishDestroy identifies fortcomp.lol as an active phishing domain posing as a fraudulent compensation scam, specifically targeting job seekers seeking fraudulent payouts. The domain masquerades as a legitimate claims portal to harvest sensitive personal and financial data under false pretenses. Security researchers note that threat actors frequently exploit job-related themes to lure victims into disclosing credentials or payment details, making this a high-risk deception tactic.
The domain’s recent creation and lack of detection underscore its stealthy deployment, requiring immediate scrutiny from both users and cybersecurity professionals. This domain was flagged with a threat type of generic_phishing and is currently under investigation by PhishDestroy. VirusTotal analysis shows 0 detections out of 95 security engines, indicating it has evaded conventional antivirus tools as of the latest scan.
The domain fortcomp.lol was registered through Global Domain Group LLC and went live on April 23, 2026, resolving to IP address 104.21.5.64. It holds a valid SSL certificate issued by Let’s Encrypt, which threat actors often use to appear legitimate. While not yet widely blacklisted, its recent activity and low detection rate suggest it may soon be weaponized at scale.
Users who visited fortcomp.lol should immediately cease any interaction with the site and avoid entering personal, financial, or login credentials. Run a full antivirus scan using updated software to detect potential malware or credential-stealing scripts. Report the domain to your browser provider or security vendor and consider blocking it via your network firewall or hosts file.
If you entered sensitive information, contact your bank or payment provider immediately and monitor accounts for unauthorized activity. Share this advisory with colleagues or contacts who may have been targeted to prevent further exploitation.
Threat response pipeline
 Cloudflare Radar
Cloudflare Radar Forensic Evidence Collection
Forensic Evidence Collectionabuse@globaldomaingroup.com with forensic evidence (metadata, screenshots, PDF).Evidence capture
Domain Intelligence
 Global Domain Group LLC
Global Domain Group LLC
Public blocklist status
Technologies
Technologies · 4 identified
VirusTotal consensus
Aggregated detection across 95 security vendors.
Evidence & external reports
Were you affected by this site?
Were You Affected?
Recommendations & Advice for Victims
- Do not pay anything else. Recovery agents demanding upfront fees are a second-stage scam.
- Disconnect compromised wallets. Move remaining funds to a fresh seed phrase generated offline.
- Preserve evidence. Screenshot transactions, save URLs, archive emails — chain-of-custody matters for prosecution.
- Report to authorities (see section 15 below) — even small reports help build case patterns.
- Notify your bank/exchange. Some chargebacks may still be possible within 24-72h.
Report to your local authorities
Email template — registrar abuse
abuse@globaldomaingroup.com
Registrar: Global Domain Group LLC Case: PD-20260517-405C66
Embed this report
About this report
About this report: fortcomp.lol
This domain security report is maintained by PhishDestroy's automated threat-intelligence pipeline. Our system continuously monitors this domain across 95 security vendors on VirusTotal and 1 public blocklists.
The site displays a page titled “Fortnite Inventory Checker | Epic Games”.
fortcomp.lol has been flagged by 0 security vendors as of May 17, 2026.
If you believe this listing is inaccurate, you can submit an appeal. For more information about our methodology, visit our FAQ page.


