$0 Takedowns, Priceless Tantrums
Since 2019, we've removed thousands of phishing domains at zero cost. Scammers retaliated with DDoS attacks, fake companies, mass reports, and forged legal documents. None of it worked. Here's the evidence.

How We Operate
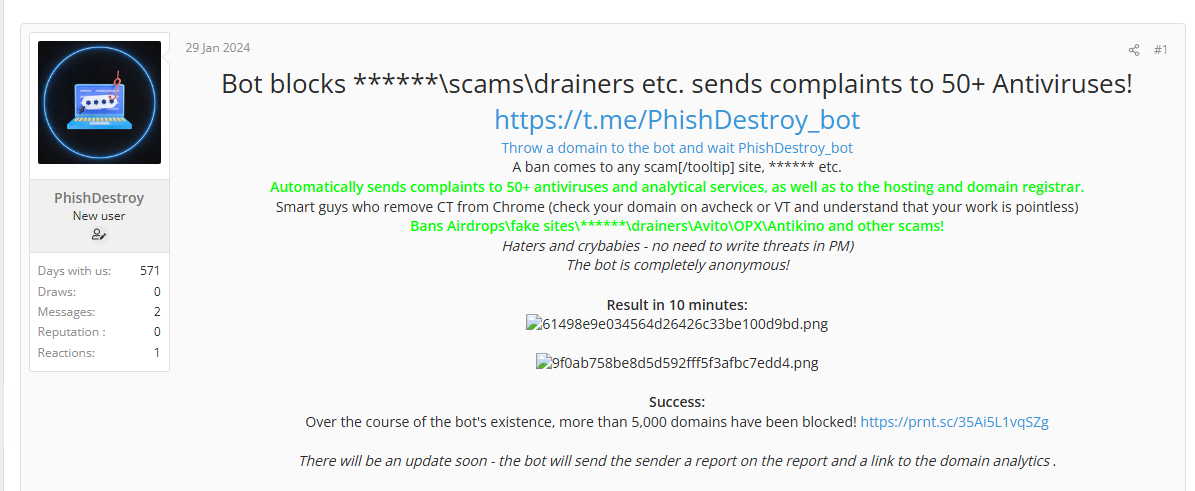
Our model is intentionally boring. We scan for phishing infrastructure, archive evidence, file structured abuse reports, and remove domains. No PR wars, no ego plays. Just automation and email.
No doxx by default. We focus on infrastructure, not individuals. When threat actors cross legal lines (threats, fraud, identity theft), we escalate to law enforcement with full evidence packages. Otherwise, we just turn off their domains.
What Scammers Tried (and Why It Failed)
Over the years, threat actors have thrown everything they could think of at us. Here's a comprehensive breakdown of every tactic, and why each one was a waste of their money.
| Attack | Method | Their Cost | Our Impact | Status |
|---|---|---|---|---|
| Email floods | 2,000-5,000 msgs/day for months | $50-300/mo | Zero | Failed |
| UK shell company | Paper company + forged "ownership" docs | $500-2,000 | Zero | Failed |
| Social takedowns | Mass-reporting X, Telegram, Medium | $100-500 | Accounts suspended, archives live | Nuisance |
| DDoS attacks | Rented botnets against our lander | $200-2,000 | Zero | Failed |
| Bot farms | Fake followers/likes/reports | $50-300 | Zero | Failed |
| False abuse reports | Fake complaints to our hosting provider | Time | Zero | Failed |
| Content swapping | Inject illegal content to trigger auto-bans | Time | Zero | Failed |
| Impersonation | Fake "Russian hacker" forums selling our work | Time | Zero | Failed |
| DDoS → host kill | 283M requests / 1.21 TB — Namecheap dropped us | $2,000+ | Migrated to Cloudflare + Hetzner | Nuisance |
| Fake DMCA | Forged OnlyFans copyright claim to Google | Time | Zero — OnlyFans denied filing | Failed |
| Trust user infiltration | Trusted user injected 46 false-positive domains | Time | Caught fast, hardened all roles | Failed |
| Appeals form spam | 9,000+ fake domain appeals via hCaptcha solving | $100-500 | Zero — trivially filtered | Failed |
| Email bombing (ongoing) | 400,000+ messages, non-stop, auto-deleted | $500+/mo | Zero | Failed |
| X/Twitter ban (again) | Gov-style emergency request → account suspended | $3,000+ | Not restoring. Done with X. | Nuisance |
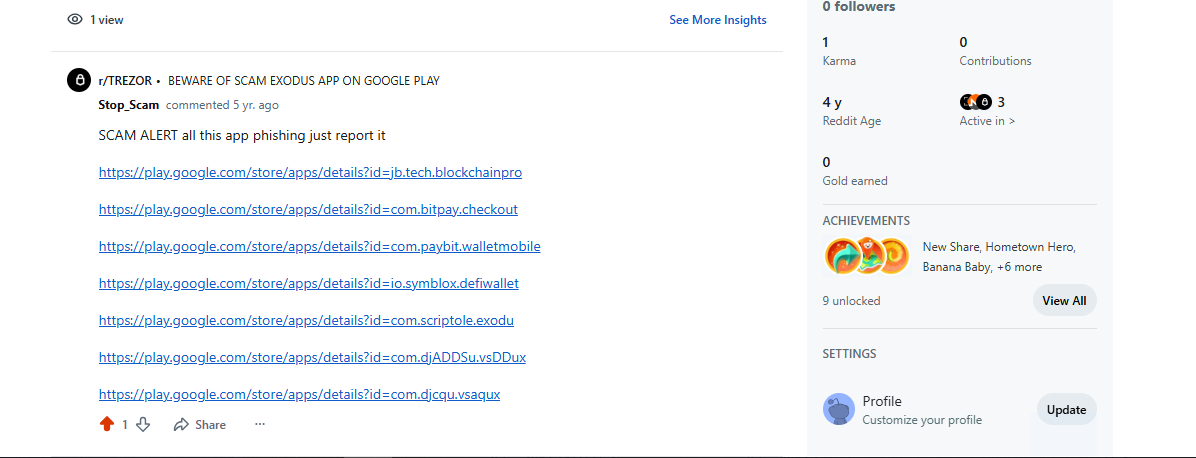
| Reddit ban | Account banned. 1 post from 5 years ago. | Time | Zero | Failed |
They spend $3,000+ per "government-style" social takedown. We spend $0 per domain removal. Our takedown pipeline is email-based automation — the website is optional. DDoS attacks against a lander are like bombing a billboard: the mail trucks keep moving.
Attack Timeline
Evidence Archive
Below is documented evidence of specific incidents. Click any card to view the full-size screenshot. All evidence is preserved for transparency and potential legal proceedings.
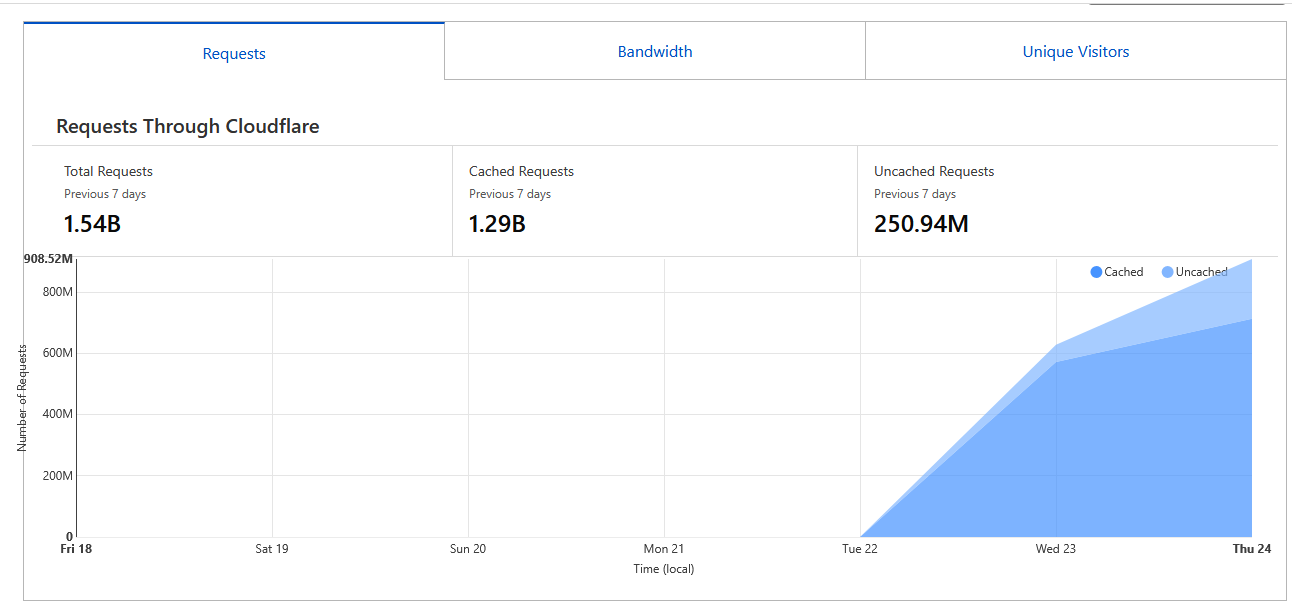
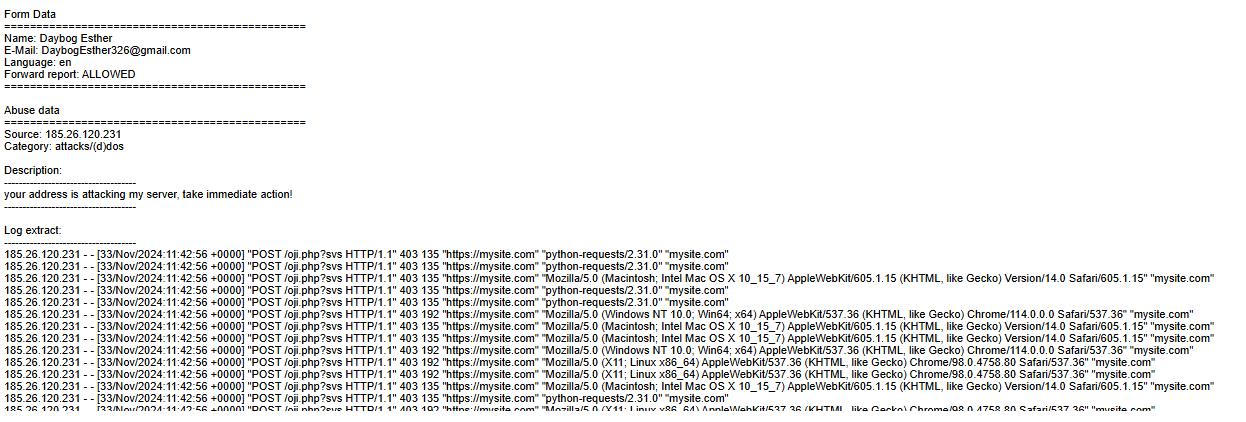

March 2026: The DDoS That Killed Our Hosting
On March 6, 2026, scammers launched the largest DDoS attack against our infrastructure to date: 283.45 million requests and 1.21 TB of bandwidth in just 7 days. The attack came from a global botnet spanning Canada (91M requests), United States (73M), Indonesia (13M), Bulgaria (13M), Guatemala (12M), Japan, Russia, and Germany.

Namecheap's $8/month hosting couldn't handle it and terminated our account. We migrated to Cloudflare + Hetzner ($25/month). After migration, they tried again — and predictably face-planted. Cloudflare absorbed everything without breaking a sweat. Zero downtime. Zero impact on takedown operations.
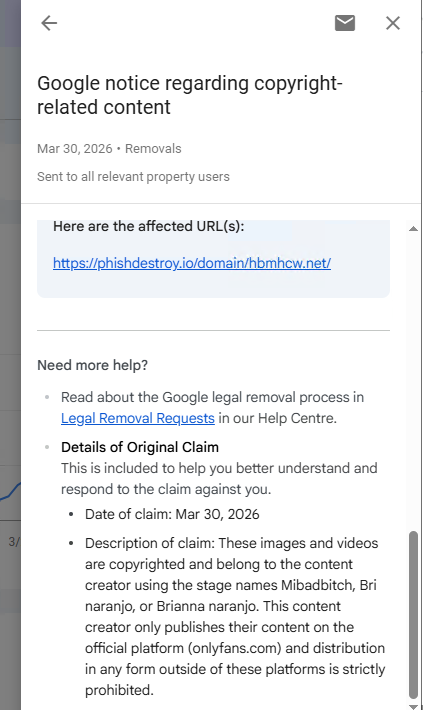
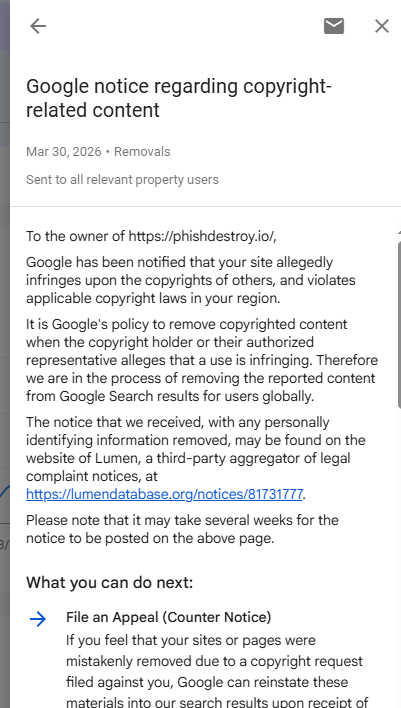
Fake DMCA Attack
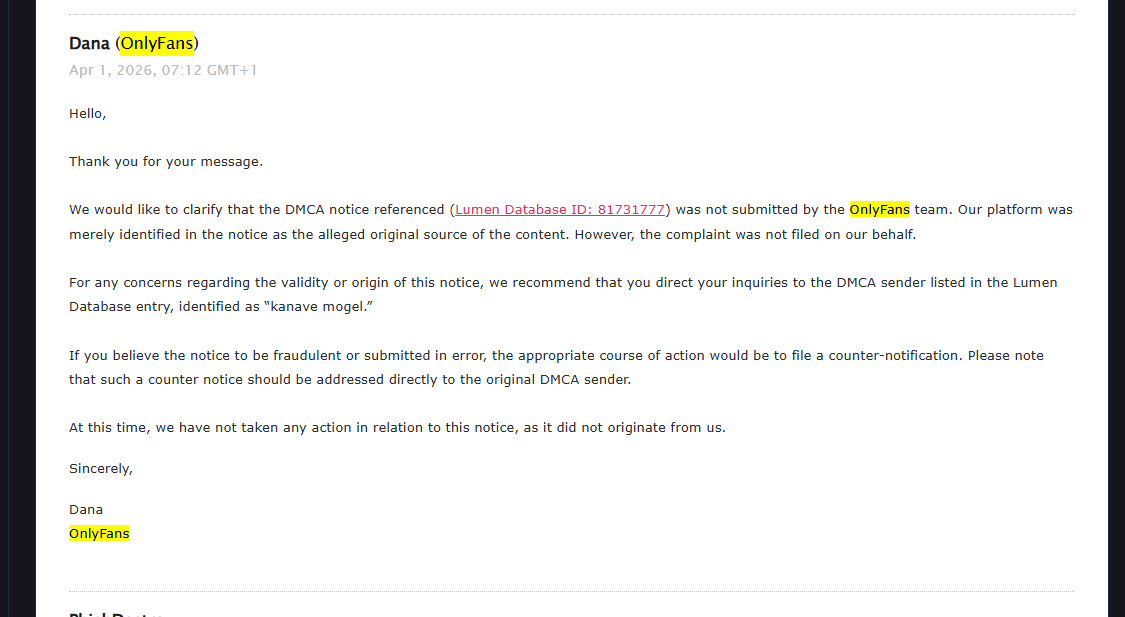
On March 30, 2026, Google notified us of a copyright complaint against our domain report page phishdestroy.io/domain/hbmhcw.net/. The claim alleged that our page contained copyrighted OnlyFans content belonging to performers "Mibadbitch, Bri naranjo, or Brianna naranjo". The complaint was filed by someone named "kanave mogel".
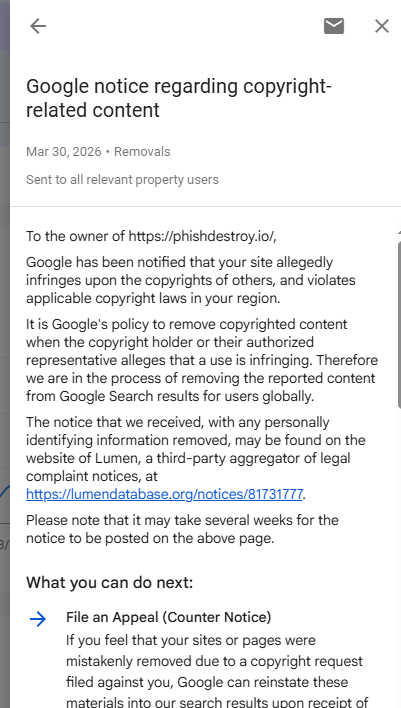
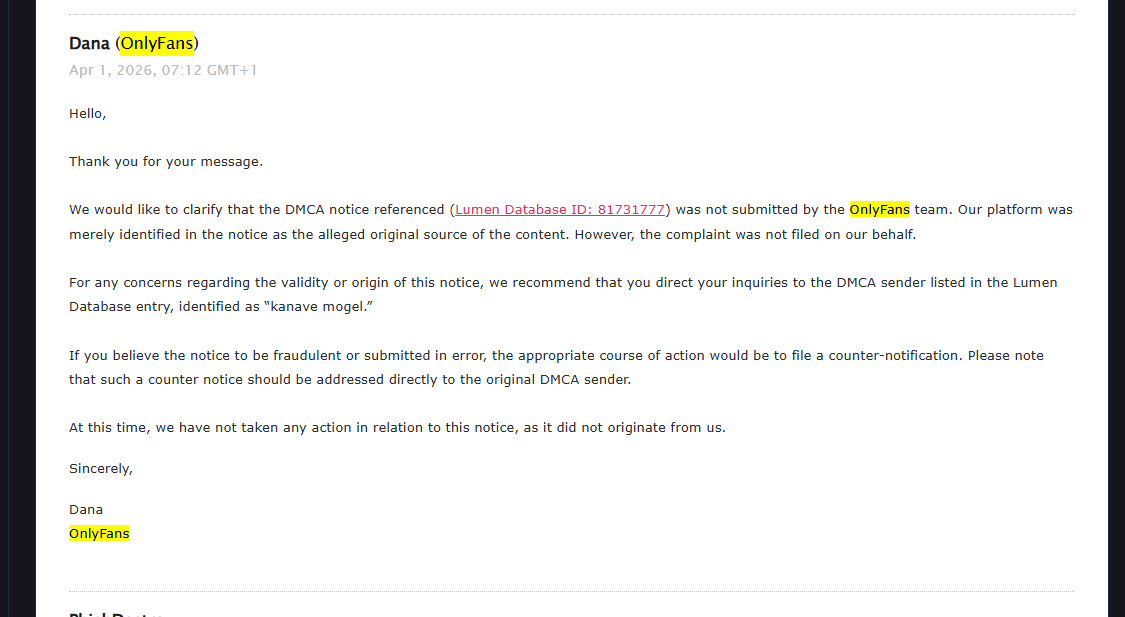
We contacted OnlyFans directly. Their response was clear: "The DMCA notice referenced (Lumen Database ID: 81731777) was not submitted by the OnlyFans team. Our platform was merely identified in the notice as the alleged original source of the content. However, the complaint was not filed on our behalf."
lumendatabase.org/notices/81731777 — The full fraudulent DMCA notice is public record. Filed by "kanave mogel". A scammer trying to use copyright law to remove evidence of their phishing domains from our reports.
Social Media Takedowns
Our social accounts are systematically targeted. X (Twitter), Telegram, Medium, Reddit — all suspended or banned via mass reports, likely using forged government emergency requests. Our latest X account was killed in April 2026. We've decided not to restore it. We're done playing whack-a-mole with platform suspensions.
After the second suspension, we decided: enough. We're not wasting time restoring accounts on platforms where scammers with money can file fake government requests to kill accounts. Our operations never depended on social media. The takedowns continue regardless.
We tell the truth and help block what needs to be blocked. Some people don't like that. They think banning or deleting our accounts will stop us or hurt us. We're not complaining — it's honestly funny at this point. We're ready for any bans and takedowns. Scammers with money and no brains = buying attacks and attempting to destroy us. But PhishDestroy is still here. And we destroy.
Evidence Preservation Protocol
Every action we take follows a strict evidence preservation protocol designed for maximum transparency and potential legal proceedings:
- Pre-takedown archiving: Web Archive snapshots + local forensic copies of every phishing site before reporting
- Chain of evidence: All communications with registrars, hosting providers, and law enforcement are logged and timestamped
- Escalation protocol: When identity is confirmed and legal lines are crossed, evidence packages are passed to authorities
- No vendetta policy: We prefer infrastructure removal to person-centric hunts. It's cleaner, faster, and scales better
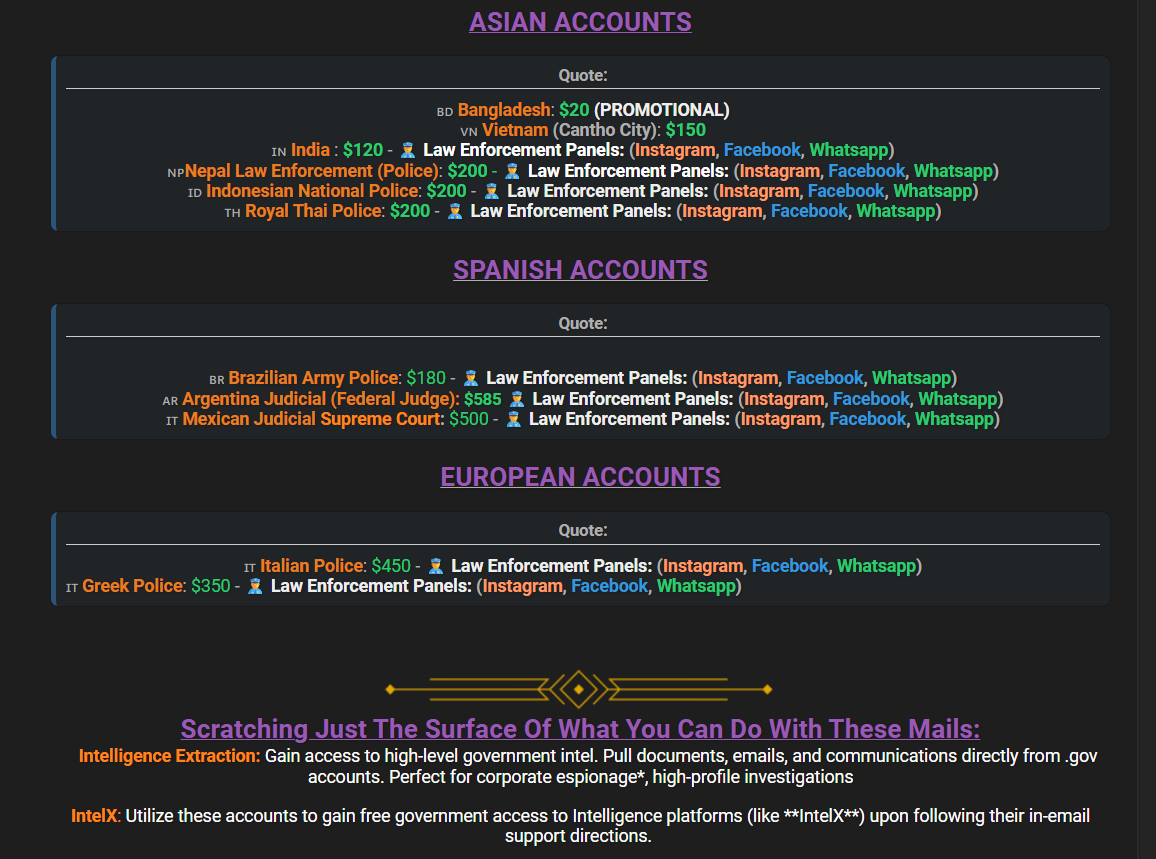
Infosecurity Magazine: Law Enforcement & Government Emails — Registrar response quality varies dramatically. Namecheap consistently acts fast; others, less so.
The $0 Model in Practice
Our cost structure is intentionally asymmetric. Every dollar they spend on retaliation is wasted. Every domain we remove costs us nothing.
| Their spend | Our spend |
|---|---|
| $3,000+ per "government-style" social takedown | $0 per automated abuse report |
| $200-2,000 for DDoS botnet rental | $0 — behind Cloudflare, email flows continue |
| $500-2,000 for UK paper company + legal forgeries | $0 — private registration, claims auto-rejected |
| $50-300/mo for email flood services | $0 — we don't use inbound email for operations |
| $50-300 for bot farm fake reports | $0 — reported and wiped by platforms |
The Scoreboard
They burn thousands trying to stop us. We spend $0 to remove their infrastructure. Our automation scales. Their panic doesn't. We warn them: "your infra turns off soon" — then chaos begins on their end. Meanwhile, we keep it boring: scan, archive, report, remove.
Want to Help?
If you've encountered a phishing site or want to contribute to the fight against crypto scams, here's how: