slon7-cc[.]site
Forensic brief
PhishDestroy identifies slon7-cc.site as an active crypto drainer impersonating Slonik Exchange, a cryptocurrency trading platform. This domain is designed to trick users into connecting their crypto wallets under the false pretense of a legitimate trading interface. Once connected, the drainer silently transfers tokens to attacker-controlled wallets, often exploiting users who assume the site is safe due to its professional appearance. Given the domain’s recent creation date and low detection rate, users should exercise extreme caution before interacting with any links or wallet connection prompts on this site. This domain was flagged by PhishDestroy after analysis revealed its recent registration and deployment. The domain slon7-cc.site was created on April 16, 2026, and currently shows 0 detections out of 95 scans on VirusTotal, indicating it has not yet been widely recognized as malicious. It is registered through the Regional Network Information Center, JSC dba RU-CENTER, and resolves to IP address 104.21.33.159. Additionally, the site uses a Let’s Encrypt SSL certificate, which may lend it an air of legitimacy despite its malicious intent. These technical indicators—combined with the domain’s suspicious naming convention mimicking the legitimate Slonik Exchange—paint a clear picture of a threat actor leveraging urgency and perceived safety to deceive users. If you have visited slon7-cc.site, immediately disconnect your wallet and revoke any permissions granted to unknown or suspicious domains. Use a reputable wallet extension or blockchain explorer to verify any unauthorized transactions. Do not interact with wallet connection prompts or input any credentials, as these may be harvested by the drainer. Report the domain to PhishDestroy and consider running a malware scan on your device. Share your findings with security communities to help others avoid falling victim to this evolving threat. Staying vigilant and verifying sites before engagement remains your strongest defense against crypto drainers like this. Seed: a78fec
Threat response pipeline
 Cloudflare Radar
Cloudflare Radar VirusTotal
VirusTotal Forensic Evidence Collection
Forensic Evidence Collectiontld-adm@nic.ru with forensic evidence (metadata, screenshots, PDF).Evidence capture
Domain Intelligence
 Regional Network Information Center, JSC dba RU-CENTER
Regional Network Information Center, JSC dba RU-CENTER
Technical details
Public blocklist status
Technologies
Technologies · 7 identified
VirusTotal consensus
Aggregated detection across 95 security vendors.
Site performance
Site performance analysis
Google PageSpeed Insights — mobile audit of slon7-cc.site
Evidence & external reports
Were you affected by this site?
Were You Affected?
Recommendations & Advice for Victims
- Do not pay anything else. Recovery agents demanding upfront fees are a second-stage scam.
- Disconnect compromised wallets. Move remaining funds to a fresh seed phrase generated offline.
- Preserve evidence. Screenshot transactions, save URLs, archive emails — chain-of-custody matters for prosecution.
- Report to authorities (see section 15 below) — even small reports help build case patterns.
- Notify your bank/exchange. Some chargebacks may still be possible within 24-72h.
Report to your local authorities
Email template — registrar abuse
tld-adm@nic.ru
Registrar: Regional Network Information Center, JSC dba RU-CENTER Case: PD-20260427-377654
Embed this report
About this report
About this report: slon7-cc.site
This domain security report is maintained by PhishDestroy's automated threat-intelligence pipeline. Our system continuously monitors this domain across 95 security vendors on VirusTotal and 1 public blocklists.
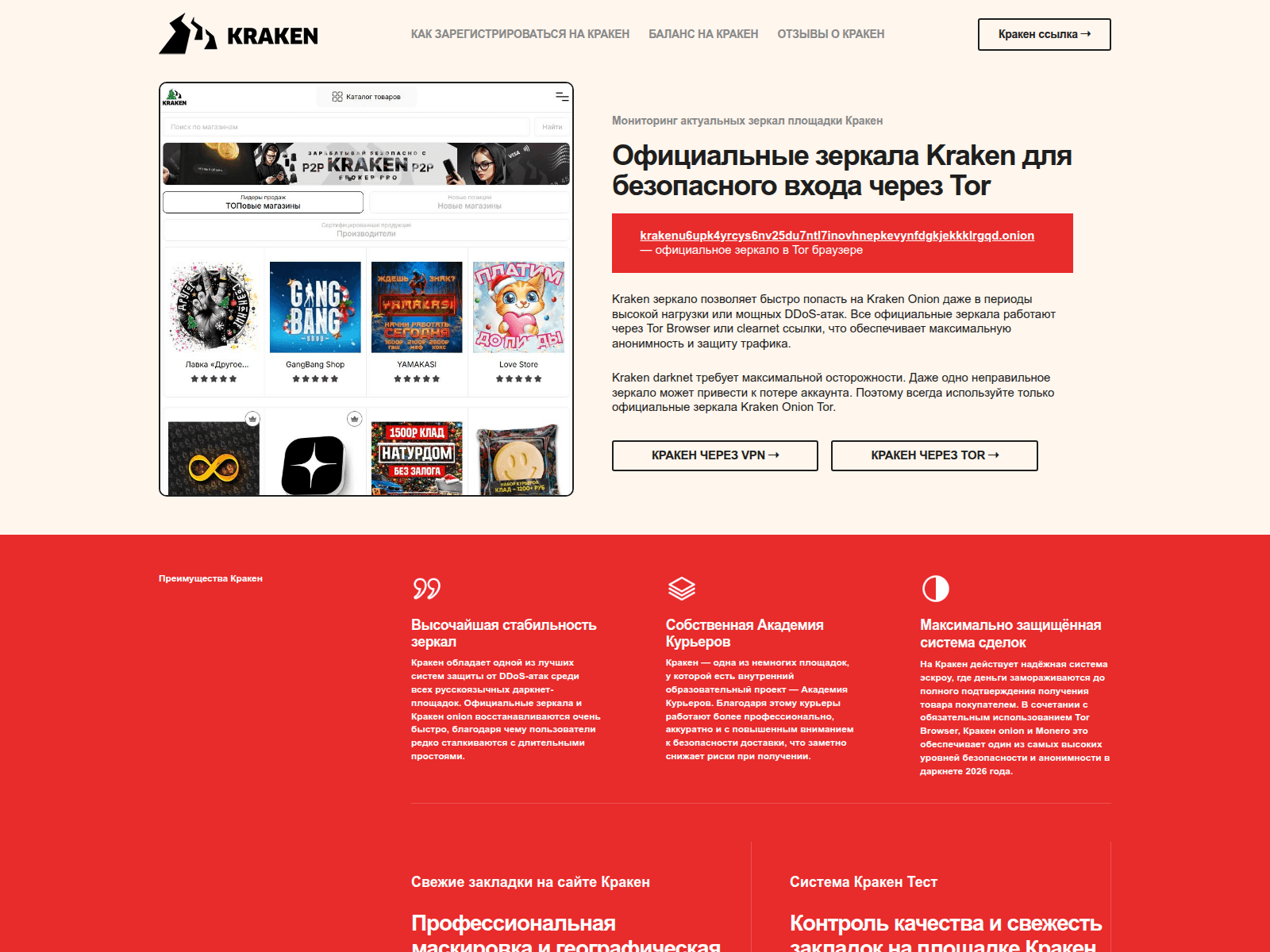
The site displays a page titled “ÐеÑкало Kraken оÑиÑиалÑное 2026. СÑÑлка на ÐÑакен Ðнион Тоє.
slon7-cc.site has been flagged by 3 security vendors as of May 17, 2026.
If you believe this listing is inaccurate, you can submit an appeal. For more information about our methodology, visit our FAQ page.

