video-chat-call[.]com
Forensic brief
Read full brief
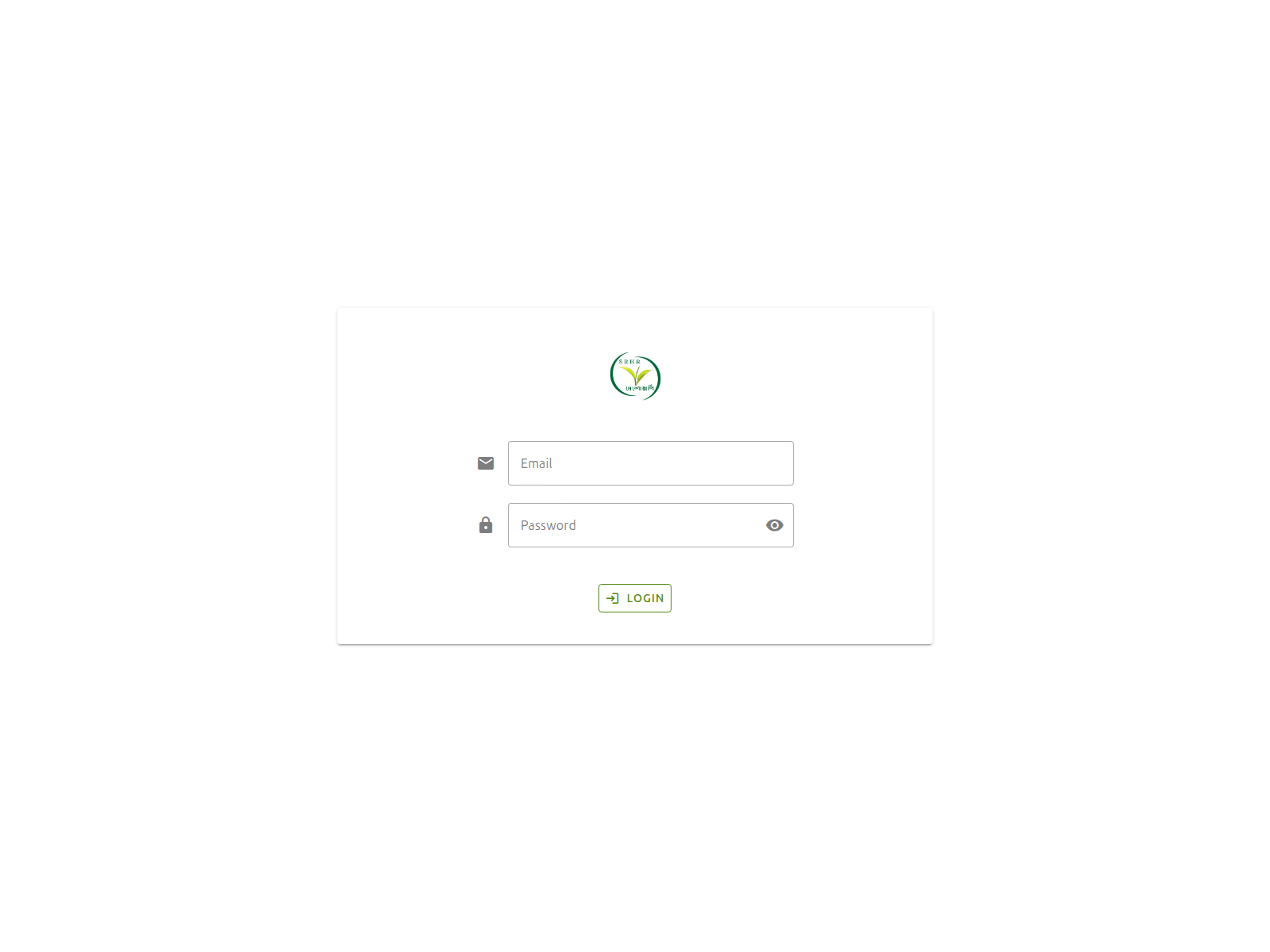
PhishDestroy identifies video-chat-call.com as a recently activated phishing domain masquerading as a video-chat service in order to harvest user logins and personal data. This generic phishing page leverages a Let’s Encrypt SSL certificate and a newly registered domain to appear legitimate, targeting victims via social media links and phishing emails. No known drainer kit or brand impersonation has been confirmed, so the threat is currently classified as a generic credential-harvesting scam.
Registrant details remain opaque via Atak Domain, leaving the true operator anonymous and the infrastructure fluid for rapid shifts in hosting or domain ownership. Technical indicators confirm the domain’s recent provenance and low detection footprint: VirusTotal shows 0 detections out of 95 engines as of March 2026, the IP address 188.114.97.3 is shared with other low-reputation hosts, the registrar Atak Domain provides WHOIS privacy protections, and the domain was created on February 22, 2026. Google Safe Browsing has not yet blacklisted the page, and public blocklists show zero listings.
These factors create a low-overhead, high-mobility threat that can persist undetected for days or weeks while luring victims to submit sensitive login information via a convincing fake chat portal. The campaign remains active with a status of under investigation. Immediate mitigation is limited without additional telemetry, but users should block 188.114.97.3 at the firewall and inspect DNS resolutions for video-chat-call.com.
Strong password hygiene and multi-factor authentication can blunt the impact of any credentials harvested via the site. Remaining risk is assessed as moderate due to the domain’s youth, undetected status, and potential for rapid expansion into broader phishing or malware campaigns. PhishDestroy continues to monitor for infrastructure pivots and will update stakeholders as new evidence emerges.
Threat response pipeline
 Cloudflare Radar
Cloudflare Radar VirusTotal
VirusTotal Forensic Evidence Collection
Forensic Evidence Collectiondomain@apiname.com with forensic evidence (metadata, screenshots, PDF).Evidence capture
Domain Intelligence
 Atak Domain
Atak Domain
Technical details
Registrar inaction · RAA §3.18
ICANN RAA §3.18 co-responsibility window expired on day 1; we re-mailed at 24h, 72h and 7d thresholds with a full forensic evidence bundle (HAR + DOM + screenshots + kit hashes). The registrar has not acknowledged. Public escalation is now warranted.
Public blocklist status
Technologies
Technologies · 4 identified
VirusTotal consensus
Aggregated detection across 95 security vendors.
Site performance
Site performance analysis
Google PageSpeed Insights — mobile audit of video-chat-call.com
Evidence & external reports
Were you affected by this site?
Were You Affected?
Recommendations & Advice for Victims
- Do not pay anything else. Recovery agents demanding upfront fees are a second-stage scam.
- Disconnect compromised wallets. Move remaining funds to a fresh seed phrase generated offline.
- Preserve evidence. Screenshot transactions, save URLs, archive emails — chain-of-custody matters for prosecution.
- Report to authorities (see section 15 below) — even small reports help build case patterns.
- Notify your bank/exchange. Some chargebacks may still be possible within 24-72h.
Report to your local authorities
Email template — registrar abuse
domain@apiname.com, zamilbd2016@gmail.com
Registrar: Atak Domain Case: PD-20260430-D2390C
Embed this report
About this report
About this report: video-chat-call.com
This domain security report is maintained by PhishDestroy's automated threat-intelligence pipeline. Our system continuously monitors this domain across 95 security vendors on VirusTotal and 3 public blocklists.
The site displays a page titled “দেশোয়ালি এডমিন”.
video-chat-call.com has been flagged by 2 security vendors as of May 17, 2026.
If you believe this listing is inaccurate, you can submit an appeal. For more information about our methodology, visit our FAQ page.


