chainwatch[.]live
Forensic brief
Read full brief
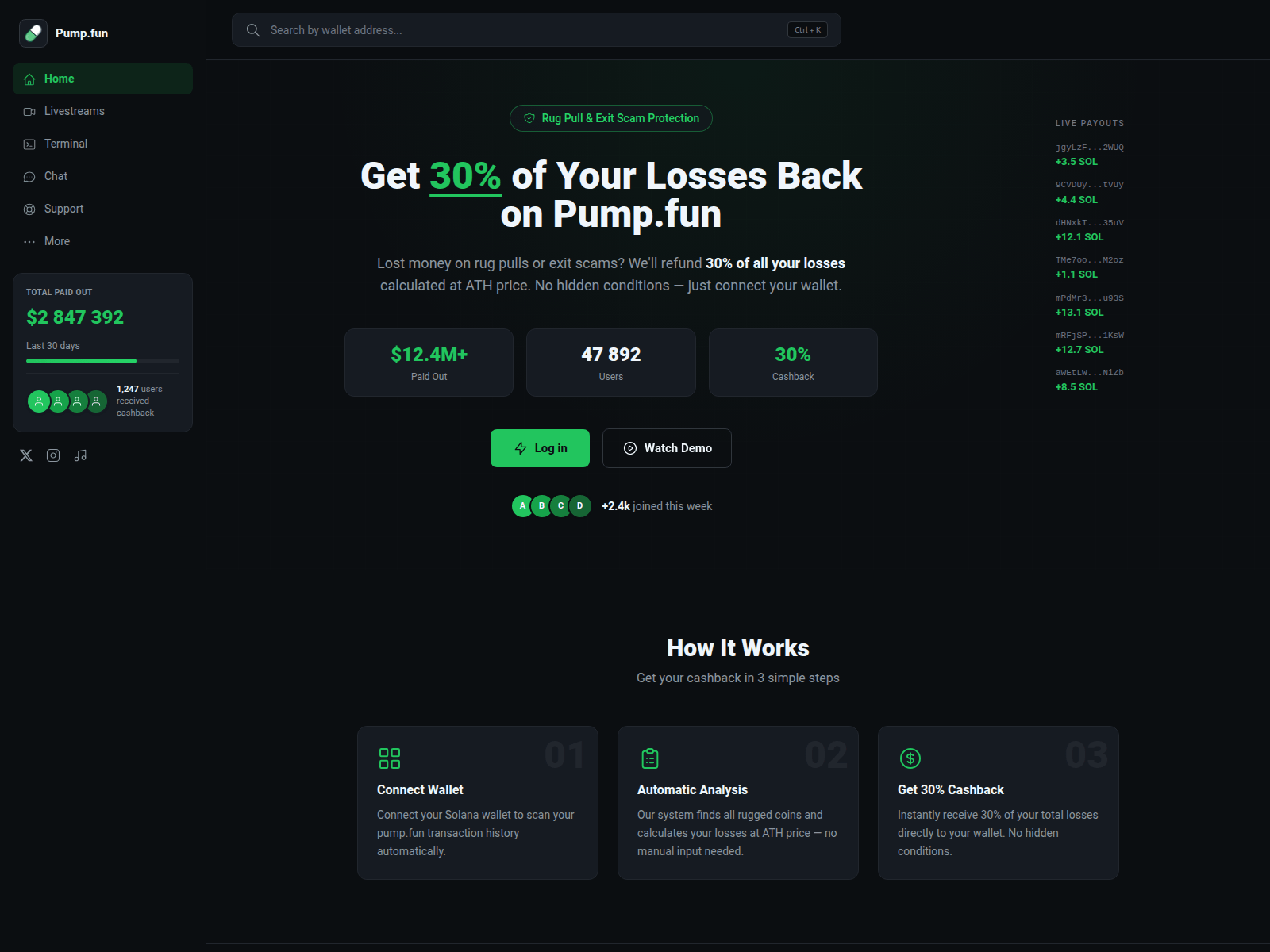
PhishDestroy identifies chainwatch.live as an active crypto phishing domain designed to steal wallet passphrases and exchange logins. The site presents itself as a real-time crypto tracker while silently exfiltrating entered credentials to attacker-controlled servers. Investigators note that once credentials are captured, funds are drained within hours, often irreversibly.
The domain was registered on April 16, 2026 through PDR Ltd. d/b/a PublicDomainRegistry.com and is currently hosted at IP 188.114.96.3. VirusTotal scanning engines report 0 out of 95 detections at the time of analysis, indicating low signature coverage and a high likelihood that the page remains undetected by most endpoint and network defenses. Let’s Encrypt provides an SSL certificate, giving the false impression of legitimacy, while the IP address is known to host multiple fraudulent dashboards targeting crypto investors.
If you visited chainwatch.live and entered any credentials or recovery phrases, immediately disconnect the device from the internet, revoke API keys on exchanges, and transfer remaining assets to a new, unrelated wallet. Reset passwords on all crypto services with reused credentials and enable hardware-based two-factor authentication. Report the domain and any wallet addresses to your local financial cybercrime unit and consider freezing compromised accounts.
Monitor transaction histories daily for 30 days; attackers often delay withdrawals to bypass fraud detection thresholds.
Threat response pipeline
 Cloudflare Radar
Cloudflare Radar Forensic Evidence Collection
Forensic Evidence Collectionabuse@publicdomainregistry.com with forensic evidence (metadata, screenshots, PDF).Evidence capture
Domain Intelligence
 PDR Ltd. d/b/a PublicDomainRegistry.com
PDR Ltd. d/b/a PublicDomainRegistry.com
Technical details
Public blocklist status
Technologies
Technologies · 3 identified
VirusTotal consensus
Aggregated detection across 95 security vendors.
Site performance
Site performance analysis
Google PageSpeed Insights — mobile audit of chainwatch.live
Evidence & external reports
Were you affected by this site?
Were You Affected?
Recommendations & Advice for Victims
- Do not pay anything else. Recovery agents demanding upfront fees are a second-stage scam.
- Disconnect compromised wallets. Move remaining funds to a fresh seed phrase generated offline.
- Preserve evidence. Screenshot transactions, save URLs, archive emails — chain-of-custody matters for prosecution.
- Report to authorities (see section 15 below) — even small reports help build case patterns.
- Notify your bank/exchange. Some chargebacks may still be possible within 24-72h.
Report to your local authorities
Email template — registrar abuse
abuse@publicdomainregistry.com
Registrar: PDR Ltd. d/b/a PublicDomainRegistry.com Case: PD-20260517-EC5E30
Embed this report
About this report
About this report: chainwatch.live
This domain security report is maintained by PhishDestroy's automated threat-intelligence pipeline. Our system continuously monitors this domain across 95 security vendors on VirusTotal and 1 public blocklists.
The site displays a page titled “ChainCheck — Solana token analytics”.
chainwatch.live has been flagged by 0 security vendors as of May 17, 2026.
If you believe this listing is inaccurate, you can submit an appeal. For more information about our methodology, visit our FAQ page.


