zoomtoken[.]net
Forensic brief
Read full brief
PhishDestroy identifies zoomtoken.net as an active domain engaged in brand impersonation targeting the OKX cryptocurrency exchange. This threat involves the creation of a counterfeit token domain designed to deceive users into interacting with fraudulent OKX-branded materials, potentially leading to financial loss through wallet compromise or fake token purchases. The domain leverages the trusted reputation of a well-known brand to exploit user trust and harvest credentials or cryptocurrency assets.
Users should treat this domain as hostile and avoid any interaction, including wallet connections or data entry. zoomtoken.net exhibits several red flags consistent with malicious intent. The domain is currently resolving to IP address 145.223.77.134 and was registered through HOSTINGER operations, UAB on May 14, 2026. VirusTotal analysis shows 0 detections out of 95 scanning engines, indicating this threat has not yet been widely recognized by automated security systems.
The domain is listed on 1 security blocklist and has been blocked by MetaMask, demonstrating proactive blocking by a major wallet provider. Despite using a Let's Encrypt SSL certificate, which provides no meaningful security assurance for users, the combination of recent registration, absence from detection systems, and immediate brand impersonation activity creates a dangerous threat profile that requires immediate attention from security teams and end users. Mitigation against this specific threat requires immediate domain blocking and user education on cryptocurrency scam tactics.
Organizations should add zoomtoken.net and its IP address (145.223.77.134) to network blocklists and endpoint detection rules to prevent accidental exposure. Users should be advised to never enter credentials or connect cryptocurrency wallets to unfamiliar domains, regardless of branding. The combination of MetaMask blocking and low detection rates suggests this threat is newly emerged, making traditional signature-based defenses ineffective.
Security teams should monitor for similar domains registered around the same date (May 14, 2026) and proactively block any newly registered domains containing 'token' or 'okx' in their naming convention. Cryptocurrency users should verify any token sale or exchange communication directly through official OKX channels and avoid clicking promotional links from unsolicited sources.
Threat response pipeline
 Cloudflare Radar
Cloudflare Radar Forensic Evidence Collection
Forensic Evidence Collectionabuse-tracker@hostinger.com with forensic evidence (metadata, screenshots, PDF).Evidence capture
Domain Intelligence
 HOSTINGER operations, UAB
HOSTINGER operations, UAB
Technical details
Public blocklist status
Technologies
Technologies · 3 identified
VirusTotal consensus
Aggregated detection across 95 security vendors.
Site performance
Site performance analysis
Google PageSpeed Insights — mobile audit of zoomtoken.net
Evidence & external reports
Were you affected by this site?
Were You Affected?
Recommendations & Advice for Victims
- Do not pay anything else. Recovery agents demanding upfront fees are a second-stage scam.
- Disconnect compromised wallets. Move remaining funds to a fresh seed phrase generated offline.
- Preserve evidence. Screenshot transactions, save URLs, archive emails — chain-of-custody matters for prosecution.
- Report to authorities (see section 15 below) — even small reports help build case patterns.
- Notify your bank/exchange. Some chargebacks may still be possible within 24-72h.
Report to your local authorities
Email template — registrar abuse
abuse-tracker@hostinger.com, report@abuseradar.com
Registrar: HOSTINGER operations, UAB Case: PD-20260516-F647F5
Embed this report
About this report
About this report: zoomtoken.net
This domain security report is maintained by PhishDestroy's automated threat-intelligence pipeline. Our system continuously monitors this domain across 95 security vendors on VirusTotal and 2 public blocklists.
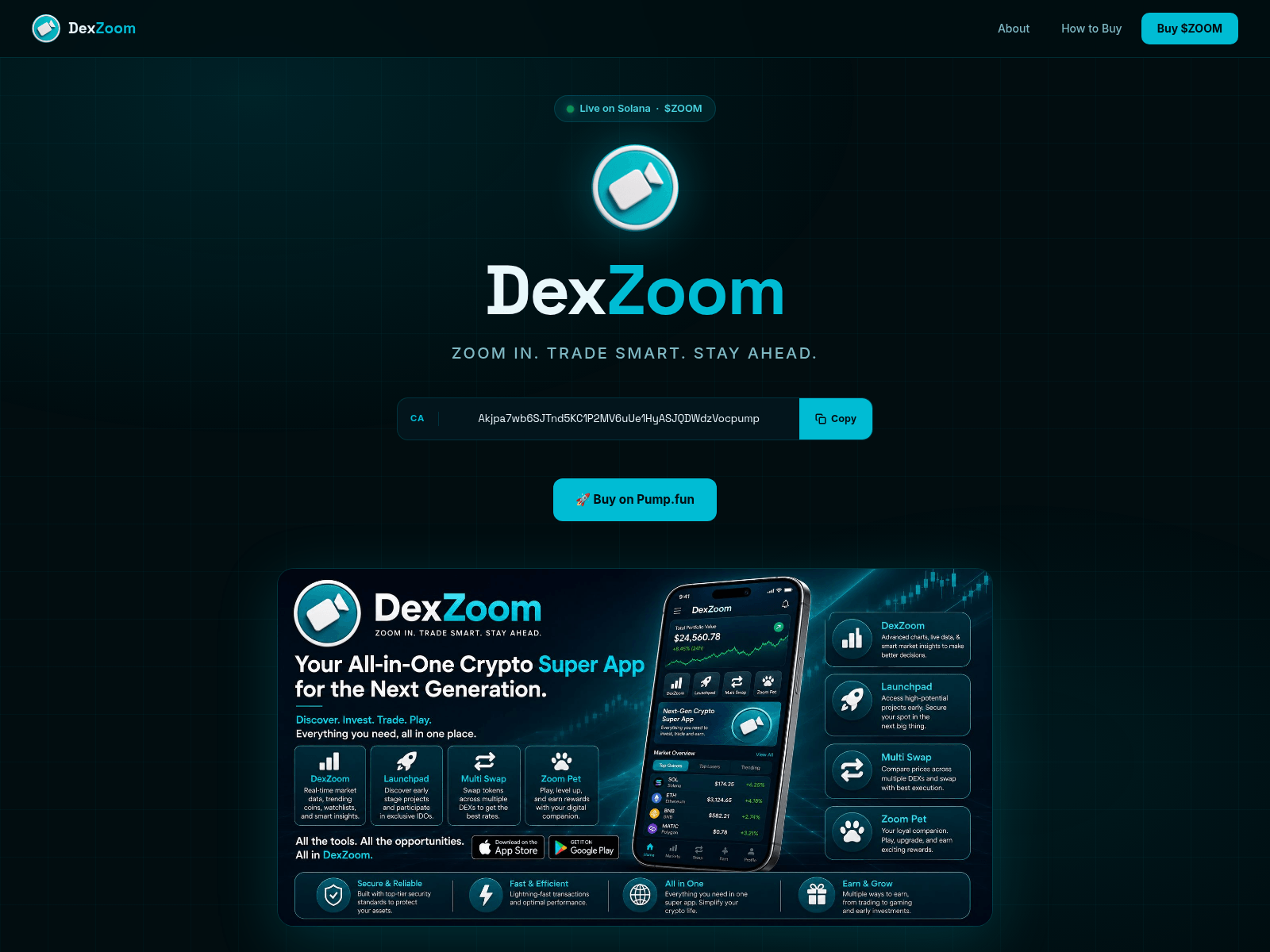
The site displays a page titled “DexZoom — $ZOOM | Zoom In. Trade Smart. Stay Ahead.”.
zoomtoken.net has been flagged by 0 security vendors as of May 17, 2026.
If you believe this listing is inaccurate, you can submit an appeal. For more information about our methodology, visit our FAQ page.



