withdrawal.transactionshield[.]info
Forensic brief
Read full brief
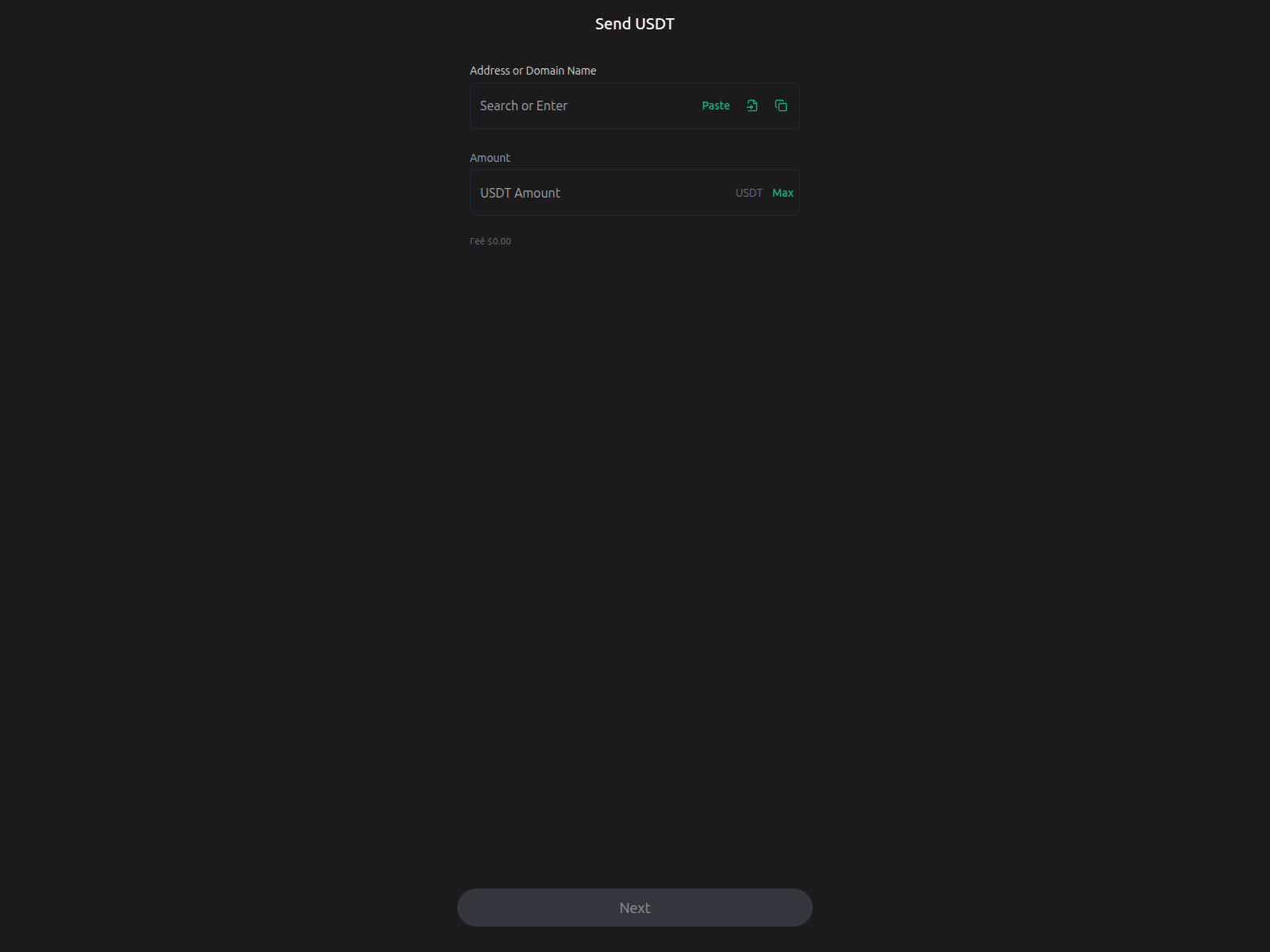
Security researchers at PhishDestroy have identified withdrawal.transactionshield.info as an active crypto-phishing domain designed to mimic legitimate withdrawal interfaces and harvest user credentials. The domain resolves to IP 104.21.14.198 and is currently leveraging Google Trust Services SSL certificates to appear authentic, which increases the likelihood of user deception. Threat actors are known to rapidly deploy similar decoy portals to target cryptocurrency users during transactional workflows.
This domain has been formally flagged by ScamSniffer and appears on a single security blocklist, indicating confirmed malicious activity. VirusTotal analysis shows 3 out of 95 participating security vendors have already marked the domain as malicious, underscoring its elevated risk profile. While the SSL certificate is issued by a reputable authority, the domain’s recent deployment and low detection rate suggest it is part of an emerging campaign rather than a well-established threat.
Users who have visited withdrawal.transactionshield.info should immediately cease any ongoing interactions, avoid entering sensitive credentials, and scan their devices for potential compromise. If credentials were entered, rotate passwords immediately, revoke any API keys or withdrawal permissions associated with the account, and monitor for unauthorized transactions. Report the domain to your security team or platform for further action.
Given the domain’s active status and SSL-backed appearance, heightened vigilance is strongly advised for anyone interacting with crypto-related web services.
Threat response pipeline
 Cloudflare Radar
Cloudflare Radar VirusTotal
VirusTotal Forensic Evidence Collection
Forensic Evidence CollectionEvidence capture
Domain Intelligence
 HOSTINGER operations, UAB
HOSTINGER operations, UAB
Technical details
Public blocklist status
Technologies
Technologies · 4 identified
VirusTotal consensus
Aggregated detection across 95 security vendors.
Site performance
Site performance analysis
Google PageSpeed Insights — mobile audit of withdrawal.transactionshield.info
Evidence & external reports
Were you affected by this site?
Were You Affected?
Recommendations & Advice for Victims
- Do not pay anything else. Recovery agents demanding upfront fees are a second-stage scam.
- Disconnect compromised wallets. Move remaining funds to a fresh seed phrase generated offline.
- Preserve evidence. Screenshot transactions, save URLs, archive emails — chain-of-custody matters for prosecution.
- Report to authorities (see section 15 below) — even small reports help build case patterns.
- Notify your bank/exchange. Some chargebacks may still be possible within 24-72h.
Report to your local authorities
Email template — registrar abuse
abuse@hostinger operations, uab
Registrar: HOSTINGER operations, UAB Case: PD-
Embed this report
About this report
About this report: withdrawal.transactionshield.info
This domain security report is maintained by PhishDestroy's automated threat-intelligence pipeline. Our system continuously monitors this domain across 95 security vendors on VirusTotal and 2 public blocklists.
The site displays a page titled “Transfer Trust Wallet”.
withdrawal.transactionshield.info has been flagged by 3 security vendors as of May 17, 2026.
If you believe this listing is inaccurate, you can submit an appeal. For more information about our methodology, visit our FAQ page.


