fidelityworkplacelh[.]click
Forensic brief
Read full brief
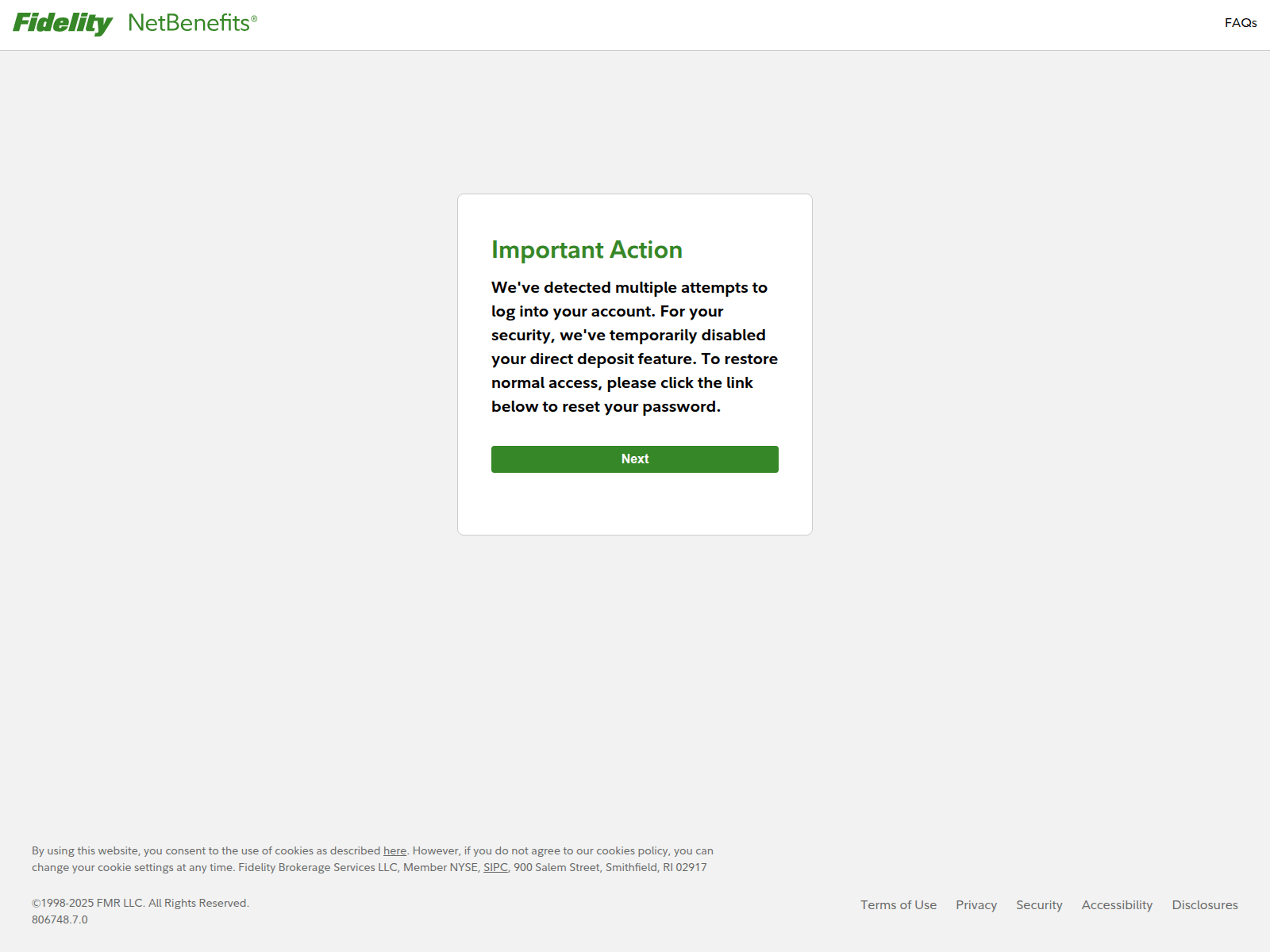
PhishDestroy identifies fidelityworkplacelh.click as an active high-risk phishing domain impersonating the Fidelity NetBenefits login page. This threat aims to steal sensitive user credentials by exploiting trust in the Fidelity brand, potentially leading to financial loss and identity theft. The domain fidelityworkplacelh.click was registered recently on February 21, 2026, and resolves to the IP address 43.162.124.172.
It currently appears on at least one security blocklist and has been flagged by 11 out of 11 security vendors on VirusTotal. Additionally, AlienVault OTX reports its presence in 13 threat intelligence pulses, indicating active monitoring and consistent detection across multiple platforms. Users are strongly advised to avoid interacting with fidelityworkplacelh.click or entering any personal information.
Always verify URLs carefully and access Fidelity accounts through official channels only. Security professionals should update blocklists and monitor related infrastructure to mitigate potential phishing campaigns linked to this domain.
Threat response pipeline
 VirusTotal
VirusTotal Forensic Evidence Collection
Forensic Evidence CollectionEvidence capture
Domain Intelligence
Technical details
Public blocklist status
VirusTotal consensus
Aggregated detection across 11 security vendors.
Evidence & external reports
Were you affected by this site?
Were You Affected?
Recommendations & Advice for Victims
- Do not pay anything else. Recovery agents demanding upfront fees are a second-stage scam.
- Disconnect compromised wallets. Move remaining funds to a fresh seed phrase generated offline.
- Preserve evidence. Screenshot transactions, save URLs, archive emails — chain-of-custody matters for prosecution.
- Report to authorities (see section 15 below) — even small reports help build case patterns.
- Notify your bank/exchange. Some chargebacks may still be possible within 24-72h.
Report to your local authorities
Email template — registrar abuse
abuse@
Case: PD-
Embed this report
About this report
About this report: fidelityworkplacelh.click
This domain security report is maintained by PhishDestroy's automated threat-intelligence pipeline. Our system continuously monitors this domain across 11 security vendors on VirusTotal and 1 public blocklists.
The site displays a page titled “Log In to Fidelity NetBenefits”.
fidelityworkplacelh.click has been flagged by 11 security vendors as of May 17, 2026.
If you believe this listing is inaccurate, you can submit an appeal. For more information about our methodology, visit our FAQ page.


