secority[.]top
Forensic brief
Read full brief
PhishDestroy identifies secority.top as an active phishing domain designed to harvest sensitive user credentials under the guise of a security service. The site mimics legitimate authentication portals, tricking visitors into entering usernames, passwords, or payment details which are then exfiltrated to attacker-controlled servers. Security researchers note that phishing pages like this often deploy urgency tactics (e.g., fake security alerts, expired account warnings) to override user caution, leading to immediate compromise of accounts or financial data.
Avoid interacting with this site entirely—it offers no legitimate value and exists solely to deceive. This domain was flagged under seed 828d5e after analysis revealed it registered on May 01, 2026, through PDR Ltd, resolving to IP address 188.114.97.3. Despite deploying a valid Let’s Encrypt SSL certificate (often used to appear trustworthy), it remains undetected by 95 security engines on VirusTotal as of the assessment.
The combination of a recently registered domain, low detection rate, and hosting via a bulletproof registrar like PDR Ltd suggests a newly launched campaign with evasion tactics. Technical indicators include the use of a Let’s Encrypt certificate to mimic legitimacy and reliance on short-lived infrastructure to avoid blacklisting. If you visited secority.top, do not enter any personal or financial information.
Immediately change passwords for any accounts you may have shared, enable two-factor authentication where possible, and scan your devices for malware using reputable antivirus software. Report the domain to your browser’s safe browsing program and consider filing a complaint with your national cybercrime unit. Avoid revisiting the site entirely—it is actively monitored for malicious activity and should not be trusted.
Stay vigilant for similar spoofed domains, especially those mimicking security or tech services.
Threat response pipeline
 Cloudflare Radar
Cloudflare Radar VirusTotal
VirusTotal Forensic Evidence Collection
Forensic Evidence CollectionEvidence capture
Domain Intelligence
 PDR Ltd.
PDR Ltd.
Technical details
Public blocklist status
Technologies
Technologies · 3 identified
VirusTotal consensus
Aggregated detection across 95 security vendors.
Evidence & external reports
Were you affected by this site?
Were You Affected?
Recommendations & Advice for Victims
- Do not pay anything else. Recovery agents demanding upfront fees are a second-stage scam.
- Disconnect compromised wallets. Move remaining funds to a fresh seed phrase generated offline.
- Preserve evidence. Screenshot transactions, save URLs, archive emails — chain-of-custody matters for prosecution.
- Report to authorities (see section 15 below) — even small reports help build case patterns.
- Notify your bank/exchange. Some chargebacks may still be possible within 24-72h.
Report to your local authorities
Email template — registrar abuse
abuse-contact@publicdomainregistry.com
Registrar: PDR Ltd. Case: PD-
Embed this report
About this report
About this report: secority.top
This domain security report is maintained by PhishDestroy's automated threat-intelligence pipeline. Our system continuously monitors this domain across 95 security vendors on VirusTotal and 1 public blocklists.
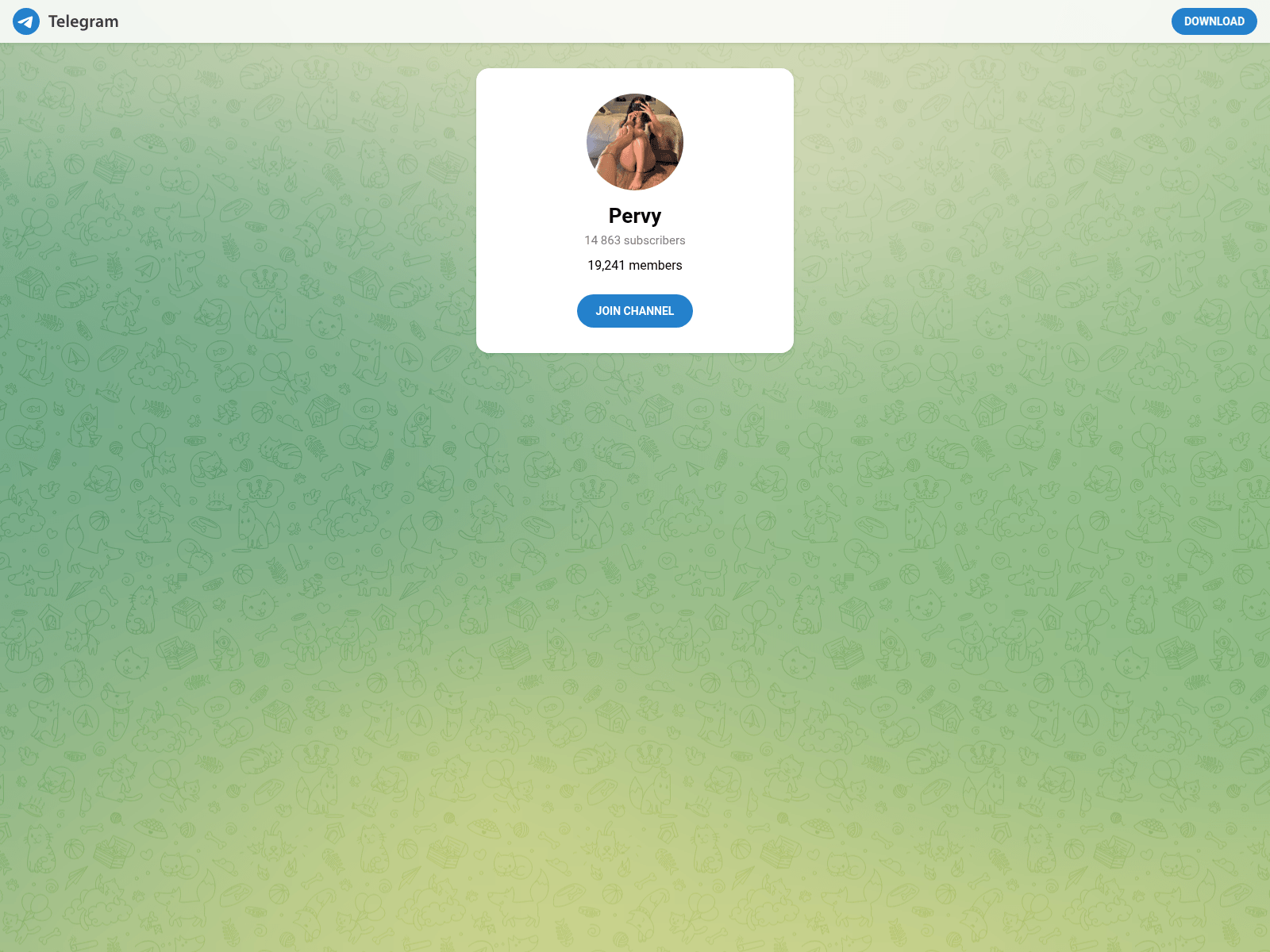
The site displays a page titled “Telegram: Join Group Chat”.
secority.top has been flagged by 3 security vendors as of May 17, 2026.
If you believe this listing is inaccurate, you can submit an appeal. For more information about our methodology, visit our FAQ page.

