megae[.]org
Forensic brief
Read full brief
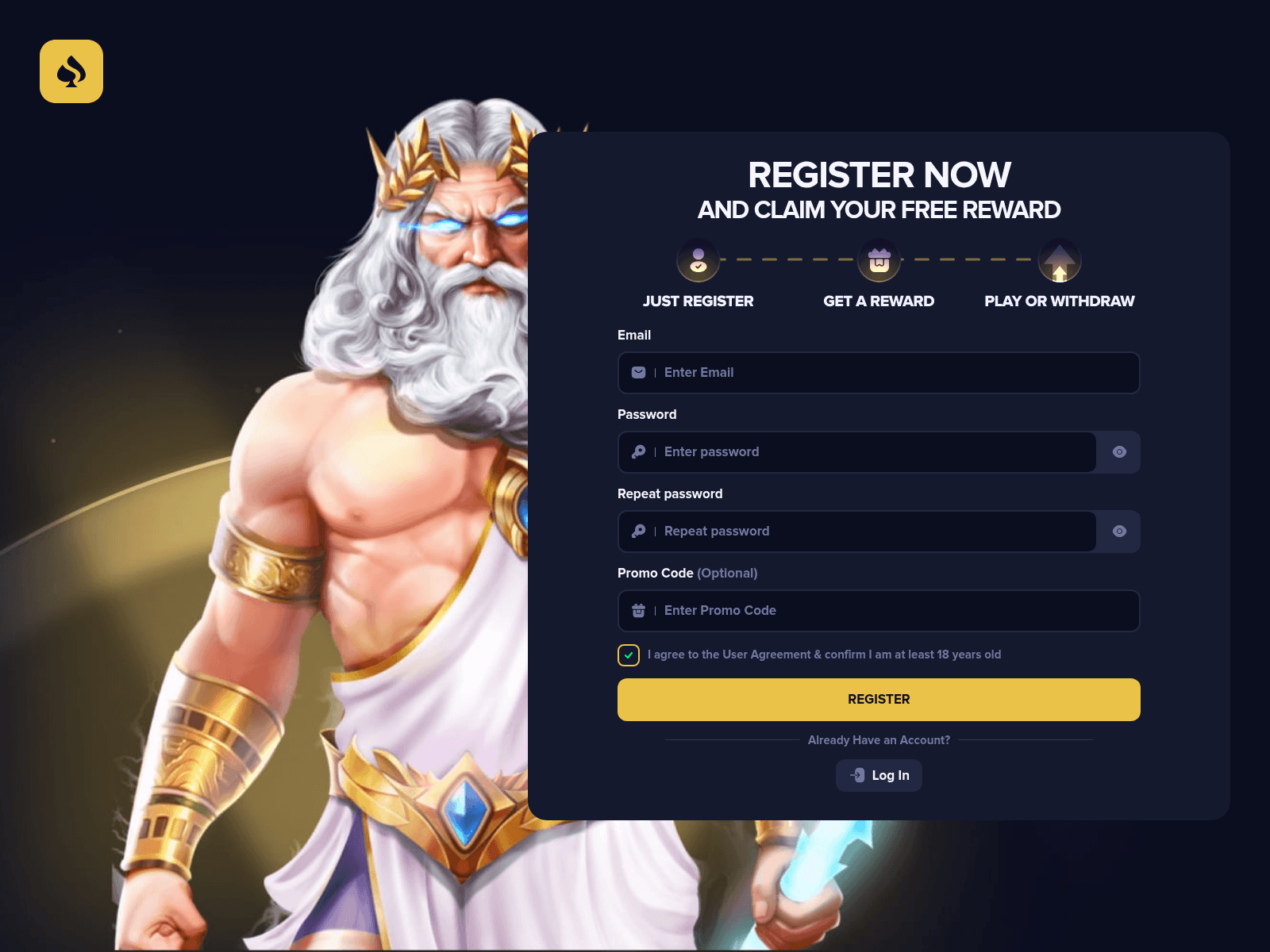
PhishDestroy identifies megae.org as an active phishing domain operating under an elevated risk classification. This domain resolves to IP address 66.198.225.39 and hosts fraudulent login pages designed to harvest user credentials under the guise of legitimate services. The threat actor leverages this domain to deceive visitors into submitting sensitive information, which is then exfiltrated for malicious purposes including credential theft and potential account takeover.
The deceptive nature of this campaign relies on the domain's superficial resemblance to trusted platforms, exploiting user trust to facilitate unauthorized access to personal and corporate accounts. This represents a clear and present danger to individuals and organizations alike. This domain was flagged by 3/95 VirusTotal security vendors, indicating a moderate but concerning detection rate.
The domain was registered through HOSTINGER operations, UAB on February 06, 2026, suggesting a recent and rapidly deployed threat infrastructure. The presence of a Let's Encrypt SSL certificate further enhances the appearance of legitimacy, potentially lowering user suspicion. The short domain age combined with the low but non-zero detection rate highlights the need for immediate attention from security teams and end-users.
Historical blocklists and threat intelligence feeds may show additional detections or associated malicious activities, reinforcing the elevated risk profile of this domain. Users who have visited megae.org should immediately cease any interaction with the site and avoid entering any credentials or personal information. If credentials were submitted, those passwords should be changed immediately, and multi-factor authentication should be enabled on all related accounts.
Users are advised to run a full antivirus scan and review financial or sensitive accounts for any signs of unauthorized activity. Organizations should block this domain at the network perimeter and investigate any potential lateral movement or data exfiltration. Security researchers are encouraged to monitor for additional domains resolving to 66.198.225.39 or exhibiting similar registration patterns.
Proactive threat hunting based on these indicators can prevent further compromise within enterprise environments.
Threat response pipeline
 Cloudflare Radar
Cloudflare Radar VirusTotal
VirusTotal Forensic Evidence Collection
Forensic Evidence Collectionabuse@hostinger.com with forensic evidence (metadata, screenshots, PDF).Evidence capture
Domain Intelligence
 HOSTINGER operations, UAB
HOSTINGER operations, UAB
Technical details
Public blocklist status
Technologies
Technologies · 2 identified
VirusTotal consensus
Aggregated detection across 95 security vendors.
Site performance
Site performance analysis
Google PageSpeed Insights — mobile audit of megae.org
Evidence & external reports
Were you affected by this site?
Were You Affected?
Recommendations & Advice for Victims
- Do not pay anything else. Recovery agents demanding upfront fees are a second-stage scam.
- Disconnect compromised wallets. Move remaining funds to a fresh seed phrase generated offline.
- Preserve evidence. Screenshot transactions, save URLs, archive emails — chain-of-custody matters for prosecution.
- Report to authorities (see section 15 below) — even small reports help build case patterns.
- Notify your bank/exchange. Some chargebacks may still be possible within 24-72h.
Report to your local authorities
Email template — registrar abuse
abuse@hostinger.com, abuse@skntelecom.com
Registrar: HOSTINGER operations, UAB Case: PD-20260517-6BA755
Embed this report
About this report
About this report: megae.org
This domain security report is maintained by PhishDestroy's automated threat-intelligence pipeline. Our system continuously monitors this domain across 95 security vendors on VirusTotal and 1 public blocklists.
The site displays a page titled “Megae: Most Popular Online Crypto Casino Based on Blockchain”.
megae.org has been flagged by 3 security vendors as of May 17, 2026.
If you believe this listing is inaccurate, you can submit an appeal. For more information about our methodology, visit our FAQ page.

