bridgeios[.]cc
Forensic brief
Read full brief
PhishDestroy identifies bridgeios.cc as an active Apple ID credential harvesting domain with elevated risk, currently classified under generic phishing threats. The domain bridgeios.cc was flagged by PhishDestroy with an elevated risk classification based on confirmed intelligence. VirusTotal analysis reveals detection by 3 out of 95 security vendors, indicating partial coverage but not universal blocking.
This domain was registered through NICENIC INTERNATIONAL GROUP CO., LIMITED and went live on May 03, 2026. Infrastructure analysis shows resolution to IP address 172.67.175.225, which is associated with cloud hosting environments commonly exploited for phishing campaigns. The domain operates with a valid SSL certificate issued by Let's Encrypt, enhancing its deceptive authenticity.
Critical risk factors include its recent creation date, leveraging fresh domains to evade historical reputation systems, and the use of trusted SSL infrastructure to appear legitimate. The immediate threat posed by bridgeios.cc involves deceptive login pages designed to mimic official Apple ID authentication portals. This specifically targets Apple users through phishing emails or malicious links, aiming to harvest Apple ID credentials and potentially associated payment methods.
Technical indicators supporting this assessment include the domain’s recent registration aligned with phishing lifecycle patterns, hosting on IP 172.67.175.225 (a known fast-flux and bulletproof hosting IP range), and the use of legitimate SSL certificates to bypass browser security warnings. While VirusTotal detection remains limited at 3/95, this is not uncommon for newly activated phishing domains that have not yet propagated across all threat intelligence platforms. Organizations and end-users are advised to implement immediate mitigation steps to neutralize this threat.
Users should verify website URLs before entering credentials and avoid clicking links from unsolicited communications. Domain blocking policies should be updated to include bridgeios.cc and its associated IP 172.67.175.225, with consideration for CIDR-based blocks covering the hosting provider’s IP ranges. Network defenders should deploy email filtering rules targeting indicators such as Let’s Encrypt SSL certificates combined with newly registered domains.
Continuous monitoring of this domain is recommended due to its active status and potential for rapid evolution into more sophisticated attack infrastructure.
Threat response pipeline
 Cloudflare Radar
Cloudflare Radar VirusTotal
VirusTotal Forensic Evidence Collection
Forensic Evidence CollectionEvidence capture
Domain Intelligence
 NICENIC INTERNATIONAL GROUP CO., LIMITED
NICENIC INTERNATIONAL GROUP CO., LIMITED
Technical details
Public blocklist status
Technologies
Technologies · 3 identified
VirusTotal consensus
Aggregated detection across 95 security vendors.
Site performance
Site performance analysis
Google PageSpeed Insights — mobile audit of bridgeios.cc
Evidence & external reports
Were you affected by this site?
Were You Affected?
Recommendations & Advice for Victims
- Do not pay anything else. Recovery agents demanding upfront fees are a second-stage scam.
- Disconnect compromised wallets. Move remaining funds to a fresh seed phrase generated offline.
- Preserve evidence. Screenshot transactions, save URLs, archive emails — chain-of-custody matters for prosecution.
- Report to authorities (see section 15 below) — even small reports help build case patterns.
- Notify your bank/exchange. Some chargebacks may still be possible within 24-72h.
Report to your local authorities
Email template — registrar abuse
abuse@nicenic.net
Registrar: NICENIC INTERNATIONAL GROUP CO., LIMITED Case: PD-
Embed this report
About this report
About this report: bridgeios.cc
This domain security report is maintained by PhishDestroy's automated threat-intelligence pipeline. Our system continuously monitors this domain across 95 security vendors on VirusTotal and 2 public blocklists.
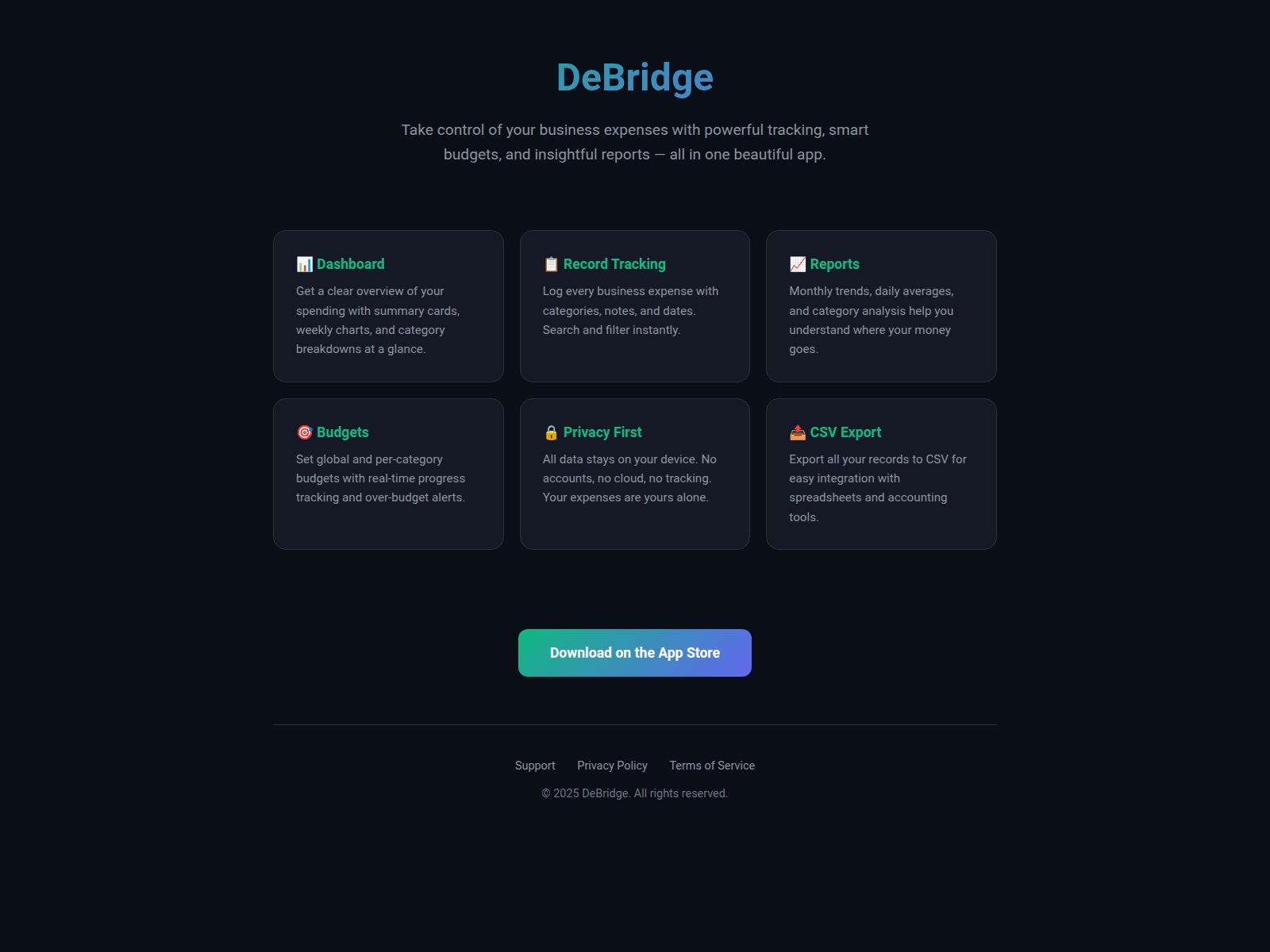
The site displays a page titled “DeBridge — Smart Business Expense Tracker”.
bridgeios.cc has been flagged by 3 security vendors as of May 17, 2026.
If you believe this listing is inaccurate, you can submit an appeal. For more information about our methodology, visit our FAQ page.


