fartnite[.]top
Forensic brief
Read full brief
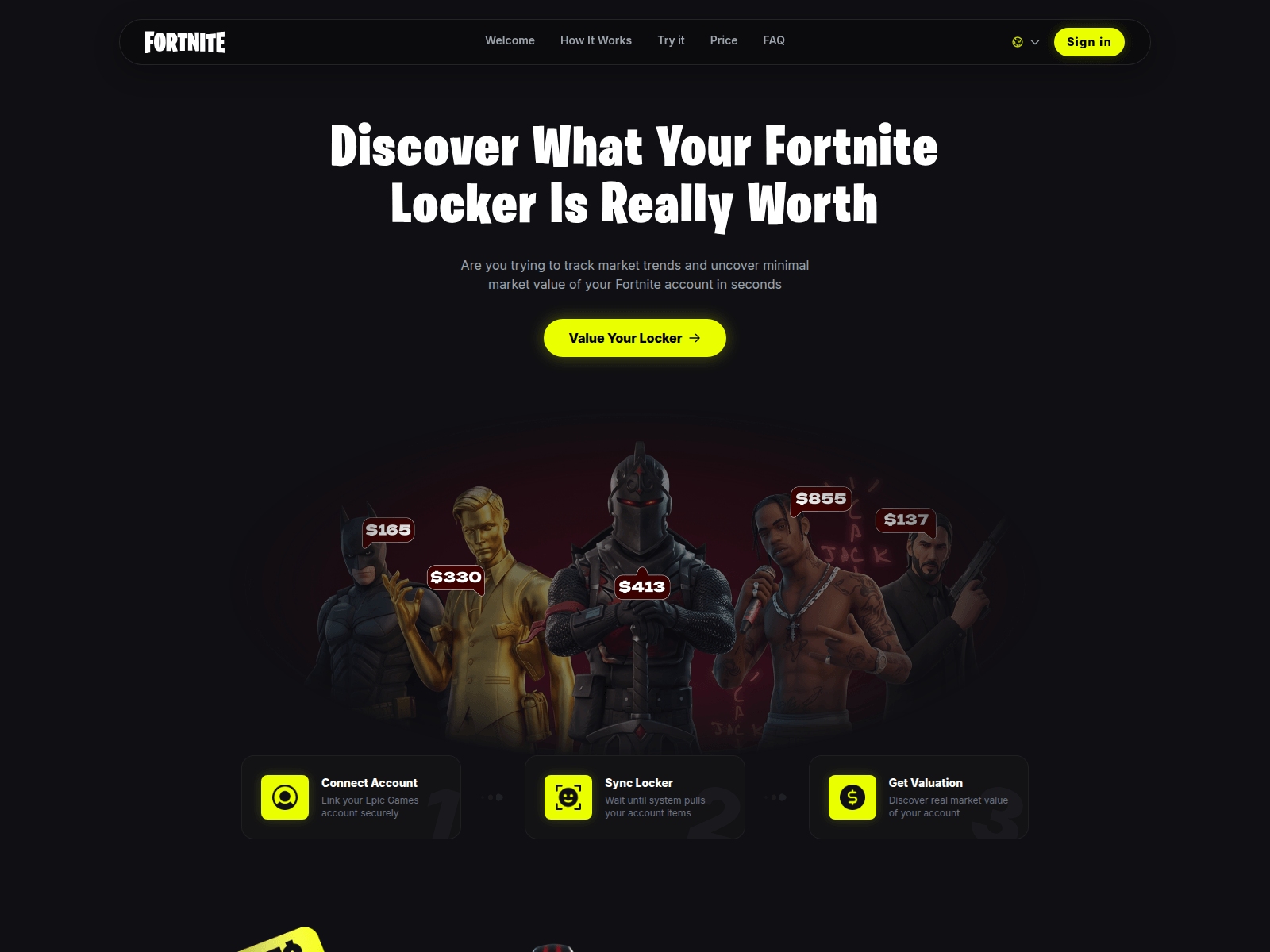
PhishDestroy identifies fartnite.top as an active fake login phishing domain currently under investigation for impersonating Epic Games, aiming to harvest user credentials through deceptive login pages. The domain remains unflagged by mainstream security vendors but exhibits red flags warranting elevated scrutiny. This report consolidates known intelligence and provides actionable recommendations for users and security researchers. fartnite.top was registered through PDR Ltd, resolving to IP address 188.114.96.3 with a Let's Encrypt SSL certificate.
The domain was created on May 15, 2026, and remains unflagged by 0 of 95 VirusTotal vendors as of the latest scan. With no confirmed blocklist entries or trust score data available, the domain's recent creation and low detection rate suggest either a newly deployed threat or a sophisticated evasion strategy. The absence of detections does not indicate safety, given the domain's suspicious registration details and alignment with known phishing patterns.
Concrete recommendations include avoiding any interaction with fartnite.top, particularly login attempts or personal information submission. Users who suspect exposure should immediately change passwords for Epic Games and linked accounts, enable multi-factor authentication, and report the domain to PhishDestroy for further analysis. Security researchers are advised to monitor the domain for emerging threats, noting the IP address and SSL certificate as primary indicators for network-based detection.
The domain's status remains active, with a risk level pending further investigation. Immediate caution is strongly advised until definitive threat intelligence or blocklist confirmations are established.
Threat response pipeline
 Cloudflare Radar
Cloudflare Radar Forensic Evidence Collection
Forensic Evidence Collectionabuse-contact@publicdomainregistry.com with forensic evidence (metadata, screenshots, PDF).Evidence capture
Domain Intelligence
 PDR Ltd
PDR Ltd
Technical details
Public blocklist status
Technologies
Technologies · 4 identified
VirusTotal consensus
Aggregated detection across 95 security vendors.
Site performance
Site performance analysis
Google PageSpeed Insights — mobile audit of fartnite.top
Evidence & external reports
Were you affected by this site?
Were You Affected?
Recommendations & Advice for Victims
- Do not pay anything else. Recovery agents demanding upfront fees are a second-stage scam.
- Disconnect compromised wallets. Move remaining funds to a fresh seed phrase generated offline.
- Preserve evidence. Screenshot transactions, save URLs, archive emails — chain-of-custody matters for prosecution.
- Report to authorities (see section 15 below) — even small reports help build case patterns.
- Notify your bank/exchange. Some chargebacks may still be possible within 24-72h.
Report to your local authorities
Email template — registrar abuse
abuse-contact@publicdomainregistry.com
Registrar: PDR Ltd Case: PD-20260517-4C6D1A
Embed this report
About this report
About this report: fartnite.top
This domain security report is maintained by PhishDestroy's automated threat-intelligence pipeline. Our system continuously monitors this domain across 95 security vendors on VirusTotal and 1 public blocklists.
The site displays a page titled “Inventory Check | Fortnite”.
fartnite.top has been flagged by 0 security vendors as of May 17, 2026.
If you believe this listing is inaccurate, you can submit an appeal. For more information about our methodology, visit our FAQ page.


