royalfityneardelhiairport.spahotel[.]guru
Forensic brief
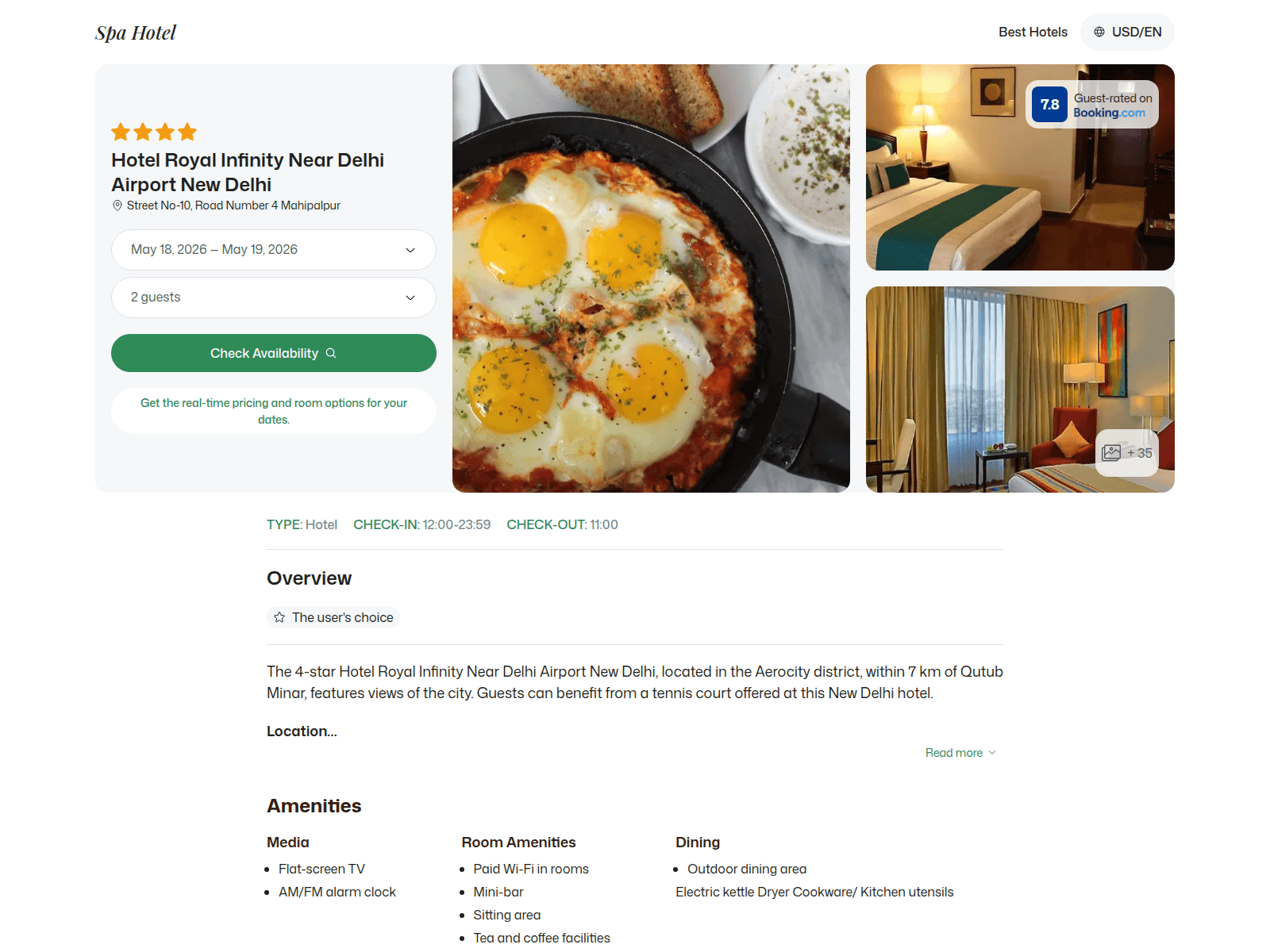
PhishDestroy identifies royalfityneardelhiairport.spahotel.guru as a fake airline spa booking phishing site that impersonates Delhi Airport’s premium spa services to steal payment and login details. The domain mimics a legitimate Royal Fityne Airline spa portal, luring users with false promises of discounted or exclusive spa treatments. Once victims enter their personal or payment information, attackers harvest the data for fraudulent transactions or identity theft. This is an elevated-risk threat designed to exploit trust in airline-branded services. This domain was flagged by PhishDestroy after 12 out of 95 VirusTotal security vendors detected malicious content. It resolved to IP address 52.29.26.157 and uses a Let’s Encrypt SSL certificate to appear legitimate. The domain was registered through a privacy-protected registrar and shows signs of recent creation, with no prior reputation in threat intelligence feeds. The mismatch between the domain name (spahotel.guru) and the claimed airline service further indicates malicious intent, as legitimate businesses rarely use .guru top-level domains. If you visited this site, stop entering any information immediately. Clear your browser cache and cookies, and scan your device with updated antivirus software. Do not trust follow-up emails claiming to help ‘secure your account’—they are likely part of the same campaign. Report the domain to your IT team or use PhishDestroy’s lookup tool to verify future links. Always navigate directly to official airline websites using verified URLs or bookmarked links to avoid similar scams.
Threat response pipeline
 Cloudflare Radar
Cloudflare Radar VirusTotal
VirusTotal Forensic Evidence Collection
Forensic Evidence CollectionEvidence capture
Domain Intelligence
Technical details
Public blocklist status
Technologies
Technologies · 5 identified
VirusTotal consensus
Aggregated detection across 12 security vendors.
Site performance
Site performance analysis
Google PageSpeed Insights — mobile audit of royalfityneardelhiairport.spahotel.guru
Evidence & external reports
Were you affected by this site?
Were You Affected?
Report to your local authorities
Email template — registrar abuse
abuse@
Case: PD-
Embed this report
About this report
About this report: royalfityneardelhiairport.spahotel.guru
This domain security report is maintained by PhishDestroy's automated threat-intelligence pipeline. Our system continuously monitors this domain across 12 security vendors on VirusTotal and 2 public blocklists.
The site displays a page titled “Hotel Royal Infinity Near Delhi Airport New Delhi - New Delhi, India”.
royalfityneardelhiairport.spahotel.guru has been flagged by 12 security vendors as of May 17, 2026.
If you believe this listing is inaccurate, you can submit an appeal. For more information about our methodology, visit our FAQ page.


