hyperliquid.com-wallets-app-connect-v3[.]com
Forensic brief
PhishDestroy identifies hyperliquid.com-wallets-app-connect-v3.com as a dangerous phishing domain designed to steal cryptocurrency assets. This site poses a high risk to users by pretending to offer legitimate wallet connection services, but its true intent is to drain funds from victims’ crypto wallets. This phishing scam typically works by mimicking trusted crypto wallet interfaces or apps, tricking users into entering sensitive information such as private keys or seed phrases. Once entered, attackers gain unauthorized access and can quickly transfer out all digital assets, leading to irreversible financial loss. If you have visited this site, immediately cease any interactions and do not provide any personal or wallet information. Consider transferring your funds to a new wallet with fresh credentials and enable two-factor authentication where possible. Monitoring your accounts for suspicious activity and consulting with a cybersecurity professional is also recommended to protect your assets.
Threat response pipeline
 VirusTotal
VirusTotal Forensic Evidence Collection
Forensic Evidence CollectionEvidence capture
Domain Intelligence
Technical details
Public blocklist status
VirusTotal consensus
Aggregated detection across 12 security vendors.
Evidence & external reports
Were you affected by this site?
Were You Affected?
Report to your local authorities
Email template — registrar abuse
abuse@
Case: PD-
Embed this report
About this report
About this report: hyperliquid.com-wallets-app-connect-v3.com
This domain security report is maintained by PhishDestroy's automated threat-intelligence pipeline. Our system continuously monitors this domain across 12 security vendors on VirusTotal and 1 public blocklists.
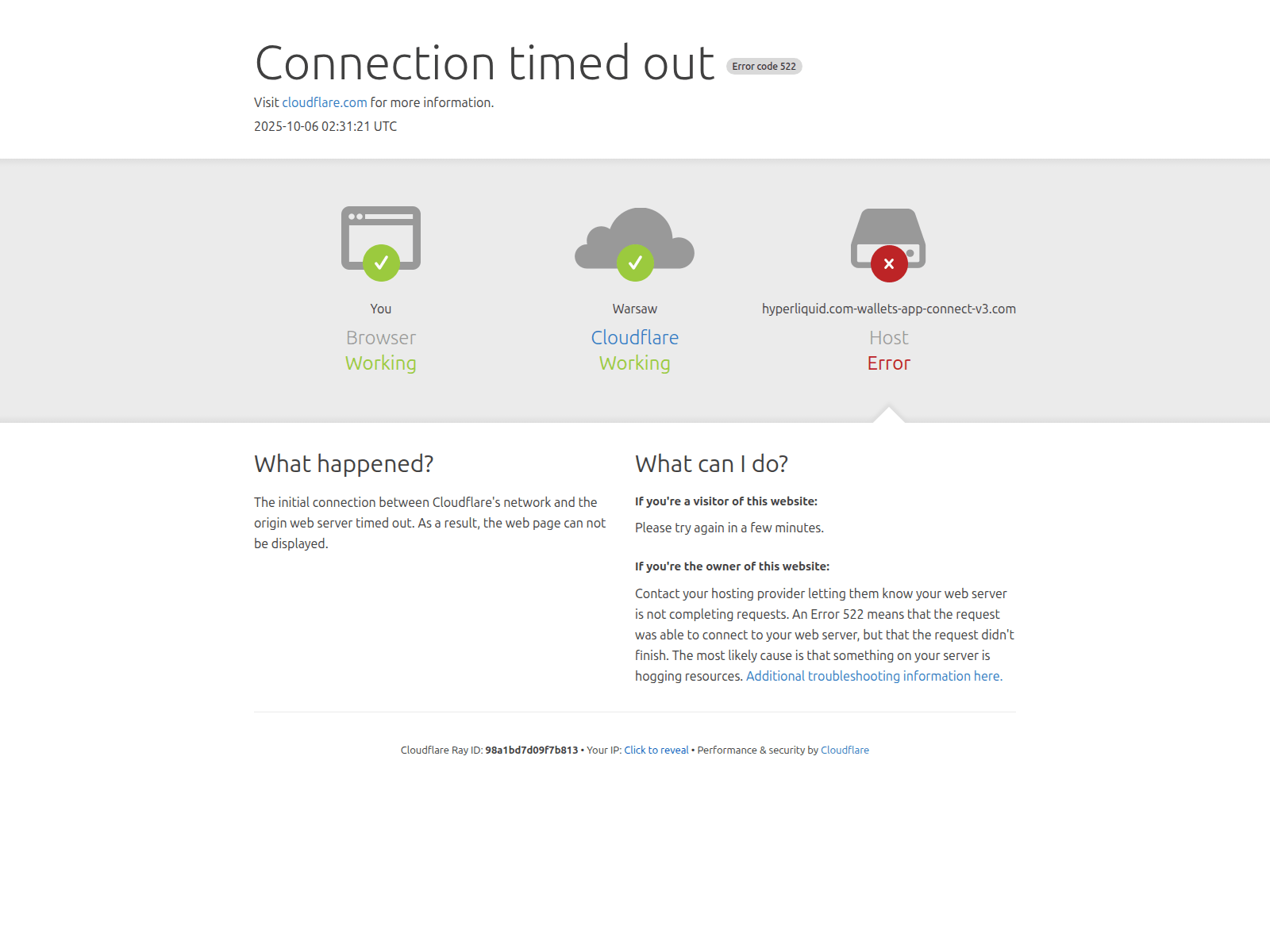
The site displays a page titled “com-wallets-app-connect-v3.com | 522: Connection timed out”.
hyperliquid.com-wallets-app-connect-v3.com has been flagged by 12 security vendors as of May 17, 2026.
If you believe this listing is inaccurate, you can submit an appeal. For more information about our methodology, visit our FAQ page.


